Development of a method for ensuring confidentiality and authenticity in wireless channels
DOI:
https://doi.org/10.15587/1729-4061.2022.268368Keywords:
crypto-code constructions of McEliece and Niederreiter, smart technologies, security concept, multi-contour protection systemsAbstract
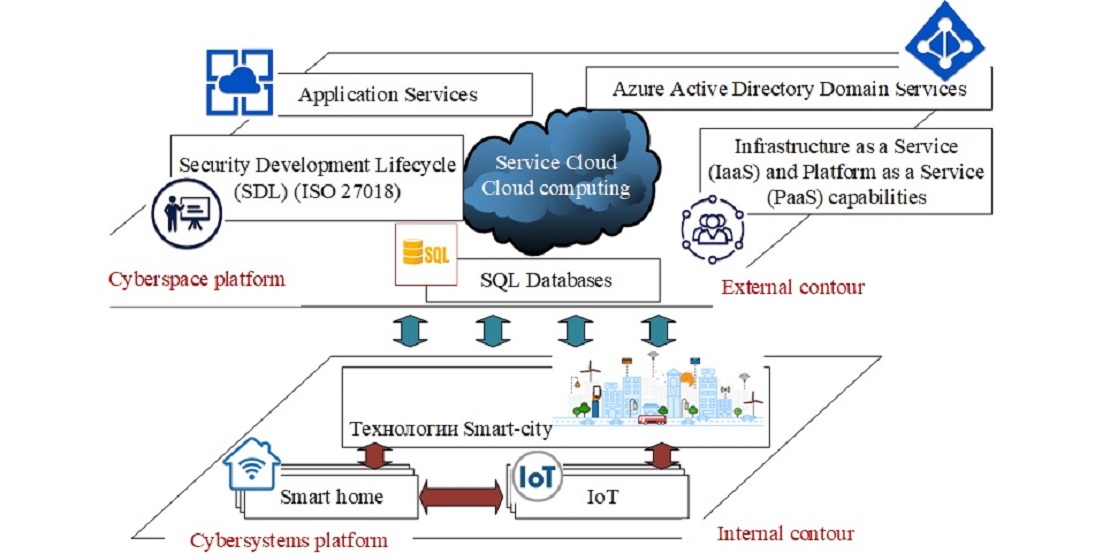
The object of the research is the development of a method for ensuring the authenticity and integrity of data in wireless channels based on post-quantum cryptosystems. The development of modern digital technologies ensures the transition to smart technologies and the formation of Next Generation Networks. The formation of smart technologies, as a rule, uses wireless communication channel standards IEEE 802.11X, IEEE 802.15.4, IEEE 802.16, which use only authentication protocols and privacy mechanisms, which are formed on symmetric algorithms. In the conditions of the post-quantum period (the advent of a full-scale quantum computer), the stability of such algorithms is questioned. Such systems, as a rule, are formed on the basis of the synthesis of socio-cyber-physical systems and cloud technologies, which simplifies the conduct of Advanced Persistent Threat attacks, both on the internal circuit of execution systems and on external control systems. The creation of multi-circuit information protection systems allows for an objective assessment of the current state of the system as a whole and the formation of preventive measures to counter cyber threats. The proposed method of providing basic security services: confidentiality, integrity and authenticity based on crypto-code constructions takes into account the level of secrecy of information transmitted over wireless channels and/or stored in databases of socio-cyber-physical systems. The use of post-quantum algorithms – McEliece/Niederreiter crypto-code constructions on elliptic/modified elliptic/lossy/Low-density parity-check code provides the necessary level of stability in the post-quantum cryptoperiod (crypto-stability at the level of 1025–1035 group operations), speed and probability of information (Рerr not lower than 10-9–10-12). The proposed method of information exchange using wireless communication channels ensures their practical implementation on resource-limited devices (creating of CCC on the GF field (24–26).
References
- Merz, H., Hansemann, T., Hübner, C. (2009). Building Automation: Communication systems with EIB/KNX, LON und BACnet. Springer, 282. doi: https://doi.org/10.1007/978-3-540-88829-1
- KNX Technical Manual. 2CKA001473B8668. Busch-Presence detector KNX / Busch-Watchdog Sky KNX (2017). Busch-Jaeger Elektro GmbH, 198. Available at: https://library.e.abb.com/public/ddedcbf7ab704705affb179ca91e0fa2/2CKA001473B8668_Prasenzmelder_6131_03_ABB_EN.pdf
- Technical documentation on KNX devices (2006). ABB.
- KNX Handbook Version 1.1 Revision 1 (2004). Konnex Association.
- ABB i-bus KNX KNX Security Panel GM/A 8.1 Product Manual. Busch-Watchdog Sky KNX (2016). Busch-Jaeger Elektro GmbH, 648.
- ABB GPG Building Automation Webinar ABB i-bus® KNX Basics and Products (2016). ABB, 86. Available at: https://library.e.abb.com/public/d26bd890d3ef476fbc3a59a2fdca6116/Webinar%20ABB%20i-bus%20KNX%20-%20KNX%20Basics%20and%20Products.pdf
- Manual for KNX Planning (2017). Siemens Switzerland Ltd, 100.
- Security Technology KNX-Intrusion Alarm System L240 Installation, Commissioning, Operation (2010). Busch-Watchdog Sky KNX. Busch-Jaeger Elektro GmbH, 116.
- Guide for Cybersecurity Event Recovery. NIST. Available at: https://nvlpubs.nist.gov/nistpubs/specialpublications/nist.sp.800-184.pdf
- Security requirements for cryptographic modules. Available at: https://csrc.nist.gov/csrc/media/publications/fips/140/2/final/documents/fips1402.pdf
- Guide to LTE Security. NIST Special Publication (SP) 800-187. Available at: https://csrc.nist.gov/csrc/media/publications/sp/800-187/draft/documents/sp800_187_draft.pdf
- Kottapalli, N. (2011). Diameter and LTE Evolved Packet System. Corporate Headquarters, 10. Available at: http://go.radisys.com/rs/radisys/images/paper-lte-diameter-eps.pdf
- Ventura, H. (2002). Diameter - Next generation’s AAA protocol. Institutionen för Systemteknik, 66. Available at: https://www.diva-portal.org/smash/get/diva2:18347/FULLTEXT01.pdf
- Vinay Kumar, S. B., Harihar, M. N. (2012). Diameter-Based Protocol in the IP Multimedia Subsystem. International Journal of Soft Computing and Engineering (IJSCE), 1 (6), 266–269. Available at: https://www.ijsce.org/wp-content/uploads/papers/v1i6/F0320121611.pdf
- Qanbari, S., Mahdizadeh, S., Rahimzadeh, R., Behinaein, N., Dustdar, S. (2016). Diameter of Things (DoT): A Protocol for Real-Time Telemetry of IoT Applications. Lecture Notes in Computer Science, 207–222. doi: https://doi.org/10.1007/978-3-319-43177-2_14
- Tschofenig, H. (2019). Diameter: new generation AAA protocol – design, practice, and applications. John Wiley & Sons, Ltd. doi: https://doi.org/10.1002/9781118875889
- Ugrozy bezopasnosti yadra paketnoy seti 4G. Available at: https://www.ptsecurity.com/ru-ru/research/analytics/epc-2017/
- Uyazvimosti protokola Diameter v setyakh 4G. Available at: https://www.ptsecurity.com/ru-ru/research/analytics/diameter-2018/
- Ashibani, Y., Mahmoud, Q. H. (2017). Cyber physical systems security: Analysis, challenges and solutions. Computers & Security, 68, 81–97. doi: https://doi.org/10.1016/j.cose.2017.04.005
- Graja, I., Kallel, S., Guermouche, N., Cheikhrouhou, S., Hadj Kacem, A. (2018). A comprehensive survey on modeling of cyber‐physical systems. Concurrency and Computation: Practice and Experience, 32 (15). doi: https://doi.org/10.1002/cpe.4850
- Minahil, Ayub, M. F., Mahmood, K., Kumari, S., Sangaiah, A. K. (2021). Lightweight authentication protocol for e-health clouds in IoT-based applications through 5G technology. Digital Communications and Networks, 7 (2), 235–244. doi: https://doi.org/10.1016/j.dcan.2020.06.003
- Inam ul haq, Wang, J., Zhu, Y., Maqbool, S. (2021). An efficient hash-based authenticated key agreement scheme for multi-server architecture resilient to key compromise impersonation. Digital Communications and Networks, 7 (1), 140–150. doi: https://doi.org/10.1016/j.dcan.2020.05.001
- Darem, A., Alhashmi, A. A., Jemal, H. A. (2022). Cybersecurity Threats and Countermeasures of the Smart Home. Ecosystem. International Journal of Computer Science and Network Security, 22 (3), 303–311. doi: https://doi.org/10.22937/IJCSNS.2022.22.3.39
- Munilla, J., Burmester, M., Barco, R. (2021). An enhanced symmetric-key based 5G-AKA protocol. Computer Networks, 198, 108373. doi: https://doi.org/10.1016/j.comnet.2021.108373
- Generic authentication architecture (GAA); generic bootstrapping architecture (GBA). TS 33.220. 3GPP. Available at: https://portal.3gpp.org/desktopmodules/Specifications/SpecificationDetails.aspx?specificationId=2280
- HMAC: Keyed-Hashing for Message Authentication. Available at: https://www.ietf.org/rfc/rfc2104.txt
- G Security; Specification of the MILENAGE algorithm set: an example algorithm set for the 3GPP authentication and key generation functions f1, f1*, f2, f3, f4, f5 and f5*; Document 5: Summary and results of design and evaluation. TR 35.909. 3GPP. Available at: https://portal.3gpp.org/desktopmodules/Specifications/SpecificationDetails.aspx?specificationId=2405
- Yevseiev, S., Tsyhanenko, O., Ivanchenko, S., Aleksiyev, V., Verheles, D., Volkov, S. et al. (2018). Practical implementation of the Niederreiter modified cryptocode system on truncated elliptic codes. Eastern-European Journal of Enterprise Technologies, 6 (4 (96)), 24–31. doi: https://doi.org/10.15587/1729-4061.2018.150903
- Yevseiev, S., Rzayev, K., Korol, O., Imanova, Z. (2016). Development of mceliece modified asymmetric crypto-code system on elliptic truncated codes. Eastern-European Journal of Enterprise Technologies, 4 (9 (82)), 18–26. doi: https://doi.org/10.15587/1729-4061.2016.75250
- Yevseiev, S., Hryhorii, K., Liekariev, Y. (2016). Developing of multi-factor authentication method based on niederreiter-mceliece modified crypto-code system. Eastern-European Journal of Enterprise Technologies, 6 (4 (84)), 11–23. doi: https://doi.org/10.15587/1729-4061.2016.86175
- Yevseiev, S., Ponomarenko, V., Laptiev, O., Milov, O., Korol, O., Milevskyi, S. et al.; Yevseiev, S., Ponomarenko, V., Laptiev, O., Milov, O. (Eds.) (2021). Synergy of building cybersecurity systems. Kharkiv: РС ТЕСHNOLOGY СЕNTЕR, 188. doi: http://doi.org/10.15587/978-617-7319-31-2
- Bleykhut, R. (1986). Teoriya i praktika kodov, kontroliruyuschikh oshibki. Moscow: Mir, 576.
- Naim, M., Ali-Pacha, H., Ali-Pacha, A., Hadj-Said, N. (2021). Lengthening the period of a Linear Feedback Shift Register. Journal of Engineering Technology and Applied Sciences. doi: https://doi.org/10.30931/jetas.778792
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2022 Serhii Yevseiev, Roman Korolev, Mykhailo Koval, Khazail Rzayev, Oleksandr Voitko, Olena Akhiiezer, Alla Hrebeniuk, Stanislav Milevskyi, Elnur Baghirov, Musa Mammadov

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.