Devising a procedure for defining the general criteria of abnormal behavior of a computer system based on the improved criterion of uniformity of input data samples
DOI:
https://doi.org/10.15587/1729-4061.2022.269128Keywords:
computer system, network activity, anomaly criterion, vector statistics, homogeneous sampleAbstract
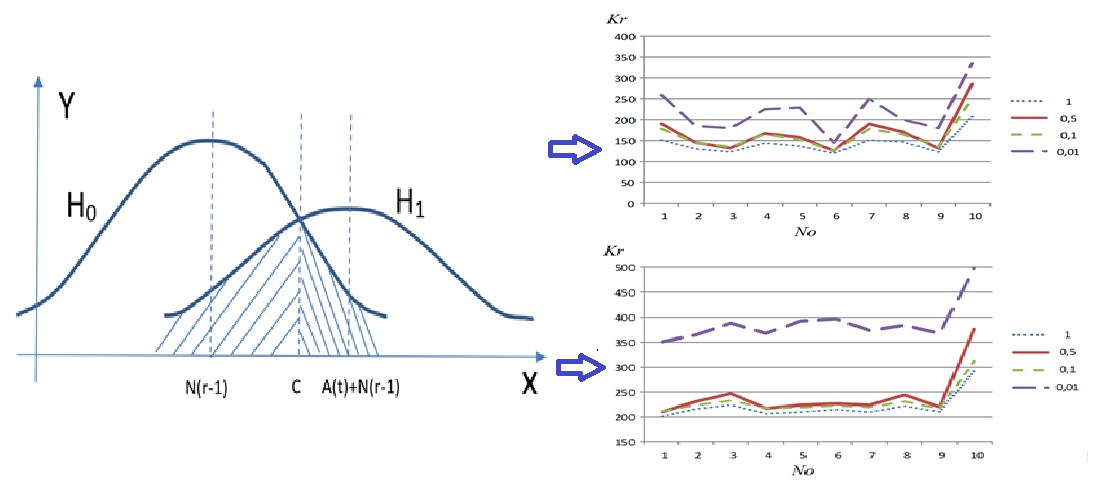
The object of this study was the process of detecting anomalies in computer systems. The task to timely detect anomalies in computer systems was solved, based on a mathematical model underlying which is the criteria for uniformity of samples of input data. The necessity and possibility to devise a universal and at the same time scientifically based approach to tracking the states of the system were determined. Therefore, the purpose of this work was to develop a methodology for determining the general criterion of anomaly in the behavior of a computer system depending on the input data. This will increase the reliability of identifying the anomaly in the behavior of the system, which, in turn, should increase its safety. To solve the problem, a mathematical model for detecting anomalies in the behavior of a computer system has been built. The mathematical model differs from the well-known ones in the possibility of isolating a series of observations, the results of which show the anomaly in the behavior of the computer system. This made it possible to ensure the necessary level of reliability of the results of monitoring and research. In the process of modeling, the criteria for uniformity of samples of input data have been investigated and improved. The expediency of using the improved criterion of uniformity of samples of input data in the case of a significantly unequal distribution of values from the sensors of computer systems has been proved. An algorithm for the functioning of the software test tool has been developed. The results of the study showed that the confidence probability that the value of the statistical values of the shift in a certain criterion does not deviate from the mathematical expectation by more than 0.05 is approximately equal to 0.94. The scope of the obtained results is systems for detecting anomalies of computer systems. A necessary condition for the use of the proposed results is the presence of a series of observations of the state of the computer system
References
- BasuMallick, C. (2022). 10 Network Behavior Anomaly Detection Tools in 2022. Available at: https://www.spiceworks.com/tech/networking/articles/network-behavior-anomaly-detection-tools/
- Wang, C., Zhou, H., Hao, Z., Hu, S., Li, J., Zhang, X. et al. (2022). Network traffic analysis over clustering-based collective anomaly detection. Computer Networks, 205, 108760. doi: https://doi.org/10.1016/j.comnet.2022.108760
- Ayensa-Jiménez, J., Pérez-Aliacar, M., Randelovic, T., Oliván, S., Fernández, L., Sanz-Herrera, J. A. et al. (2020). Mathematical formulation and parametric analysis of in vitro cell models in microfluidic devices: application to different stages of glioblastoma evolution. Scientific Reports, 10 (1). doi: https://doi.org/10.1038/s41598-020-78215-3
- Meleshko, Y., Drieiev, O., Yakymenko, M., Lysytsia, D. (2020). Developing a model of the dynamics of states of a recommendation system under conditions of profile injection attacks. Eastern-European Journal of Enterprise Technologies, 4 (2 (106)), 14–24. doi: https://doi.org/10.15587/1729-4061.2020.209047
- Bannai, E., Bannai, E., Ito, T., Rie, T. (2021). 6 P- and Q-polynomial schemes. Algebraic Combinatorics, Berlin, Boston: De Gruyter, 241–398. doi: https://doi.org/10.1515/9783110630251-006
- Semenov, S., Davydov, V., Lipchanska, O., Lipchanskyi, M. (2020). Development of unified mathematical model of programming modules obfuscation process based on graphic evaluation and review method. Eastern-European Journal of Enterprise Technologies, 3 (2 (105)), 6–16. doi: https://doi.org/10.15587/1729-4061.2020.206232
- Meleshko, Y., Raskin, L., Semenov, S., Sira, O. (2019). Methodology of probabilistic analysis of state dynamics of multidimensional semiMarkov dynamic systems. Eastern-European Journal of Enterprise Technologies, 6 (4 (102)), 6–13. doi: https://doi.org/10.15587/1729-4061.2019.184637
- Kovalenko, A., Kuchuk, H. (2022). Methods to Manage Data in Self-healing Systems. Studies in Systems, Decision and Control. Cham: Springer, 113–171. doi: https://doi.org/10.1007/978-3-030-96546-4_3
- Rempała, G., Wesołowski, J. (2023). Poisson limit theorems for the Cressie-Read statistics. Journal of Statistical Planning and Inference, 223, 15–32. doi: https://doi.org/10.1016/j.jspi.2022.07.004
- Escalante, J. M., Skipetrov, S. E. (2018). Level spacing statistics for light in two-dimensional disordered photonic crystals. Scientific Reports, 8 (1). doi: https://doi.org/10.1038/s41598-018-29996-1
- Tung, D. D., Rao Jammalamadaka, S. (2012). U-Statistics based on spacings. Journal of Statistical Planning and Inference, 142 (3), 673–684. doi: https://doi.org/10.1016/j.jspi.2011.09.007
- Raskin, L., Sukhomlyn, L., Sagaidachny, D., Korsun, R. (2021). Analysis of multi-threaded markov systems. Advanced Information Systems, 5 (4), 70–78. doi: https://doi.org/10.20998/2522-9052.2021.4.11
- Oleksenko, O., Khudov, H., Petrenko, K., Horobets, Y., Kolianda, V., Kuchuk, N. et al. (2021). The Development of the Method of Radar Observation System Construction of the Airspace on the Basis of Genetic Algorithm. International Journal of Emerging Technology and Advanced Engineering, 11 (8), 23–30. doi: https://doi.org/10.46338/ijetae0821_04
- Semenov, S., Sira, O., Gavrylenko, S., Kuchuk, N. (2019). Identification of the state of an object under conditions of fuzzy input data. Eastern-European Journal of Enterprise Technologies, 1 (4 (97), 22–30. doi: https://doi.org/10.15587/1729-4061.2019.157085
- Kovalenko, A., Kuchuk, H., Kuchuk, N., Kostolny, J. (2021). Horizontal scaling method for a hyperconverged network. 2021 International Conference on Information and Digital Technologies (IDT), 331–336. doi: https://doi.org/10.1109/idt52577.2021.9497534
- Yaloveha, V., Hlavcheva, D., Podorozhniak, A., Kuchuk, H. (2019). Fire Hazard Research of Forest Areas based on the use of Convolutional and Capsule Neural Networks. 2019 IEEE 2nd Ukraine Conference on Electrical and Computer Engineering (UKRCON). doi: https://doi.org/10.1109/ukrcon.2019.8879867
- Al-Anzi, F. S., Lababidi, H. M. S., Al-Sharrah, G., Al-Radwan, S. A., Seo, H. J. (2022). Plant health index as an anomaly detection tool for oil refinery processes. Scientific Reports, 12 (1). doi: https://doi.org/10.1038/s41598-022-18824-2
- Sohn, H., Czarnecki, J. A.,Farrar, C. R. (2000). Structural Health Monitoring Using Statistical Process Control. Journal of Structural Engineering, 126 (11), 1356–1363. doi: https://doi.org/10.1061/(asce)0733-9445(2000)126:11(1356)
- Lu, Y., Wang, T., Liu, T. (2020). Bayesian Network-Based Risk Analysis of Chemical Plant Explosion Accidents. International Journal of Environmental Research and Public Health, 17 (15). doi: https://doi.org/10.3390/ijerph17155364
- An, S. H., Heo, G., Chang, S. H. (2011). Detection of process anomalies using an improved statistical learning framework. Expert Systems with Applications, 38 (3), 1356–1363. doi: https://doi.org/10.1016/j.eswa.2010.07.031
- Pratama, A., Rafrastara, F. A. (2012). Computer Worm Classification. International Journal of Computer Science and Information Security, 10, 21–24. Available at: https://www.researchgate.net/publication/299580232_Computer_Worm_Classification
- Raskin, L., Ivanchikhin, Y., Sukhomlyn, L., Sviatkin, I., Korsun, R. (2022). Evaluation model of the recovery processes of non-markovian systems, considering the elements unreliability under arbitrary distribution laws. Advanced Information Systems, 6 (3), 28–35. doi: https://doi.org/10.20998/2522-9052.2022.3.04
- Joseph, U. M., Jacob, M. (2022). Real time detection of Phishing attacks in edge devices using LSTM networks. AIP Conference Proceedings. https://doi.org/10.1063/5.0103355
- Mozhaev, O., Kuchuk, H., Kuchuk, N., Mozhaev, M., Lohvynenko, M. (2017). Multiservice network security metric. 2017 2nd International Conference on Advanced Information and Communication Technologies (AICT), 133–136. doi: https://doi.org/10.1109/aiact.2017.8020083
- Guevara López, P., Delgado Reyes, G., Audelo González, J., Valdez Martínez, J., Perez Meana, H. (2015). Basic definitions for discrete modeling of computer worms epidemics. Ingeniería e Investigación, 35 (1), 79–85. doi: https://doi.org/10.15446/ing.investig.v35n1.44323
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2022 Serhii Semenov, Oleksandr Mozhaiev, Nina Kuchuk, Mykhailo Mozhaiev, Serhii Tiulieniev, Yurii Gnusov, Dmytro Yevstrat, Yuliia Chyrva, Heorhii Kuchuk

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





