Development of a hybrid probabilistic key generation method using multi-prime Rivest-Shamir-Adleman and learning with errors to enhance Hill cipher security
DOI:
https://doi.org/10.15587/1729-4061.2026.348890Keywords:
Hill cipher, multi-prime RSA, learning with errors, probabilistic encryptionAbstract
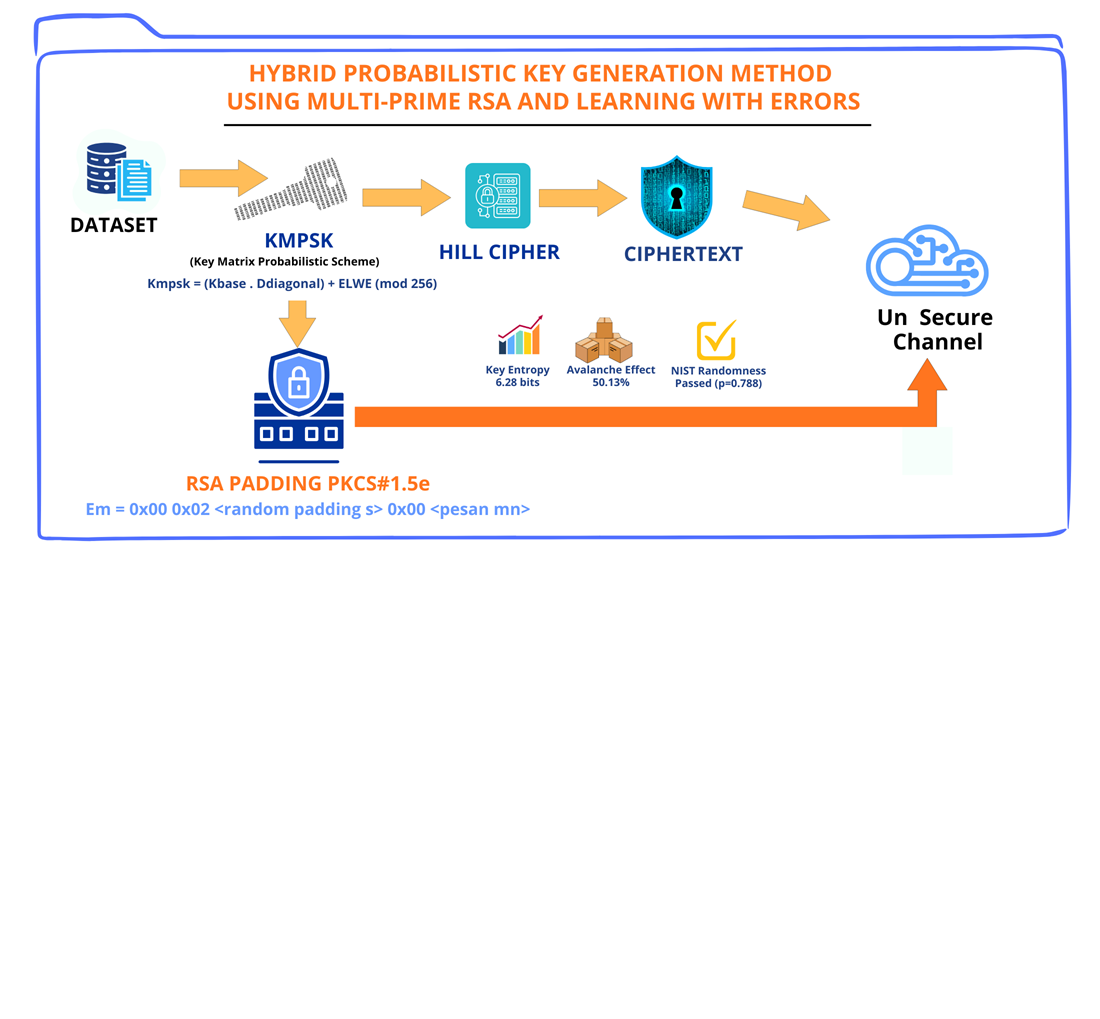
This study focuses on the vulnerabilities of classical matrix-based encryption and asymmetric padding schemes within hybrid cryptosystems for securing high-throughput enterprise data streams. The Hill cipher algorithm is highly vulnerable to known-plaintext attacks and frequency distribution analysis, whereas the standard Rivest-Shamir-Adleman (RSA) padding scheme of public-key cryptography standards (PKCS#1 v1.5) is vulnerable to padding oracle attacks. To overcome these issues, this study proposes a hybrid cryptographic model which integrates with the key matrix probabilistic scheme (KMPS) using multi-prime RSA architecture and learning with errors (LWE), alongside a modified padding scheme (PKCS #1 v1.5e) utilizing random noises. The feature of this method is the construction of a non-deterministic key matrix combining a random base matrix with a diagonal matrix derived from multi-prime RSA parameters and interjecting Gaussian probabilistic noise. This is followed by security validation using the National Institute of Standards and Technology (NIST) Statistical Test Suite. Experimental results demonstrate that for a 10 x 10 matrix, the ciphertext achieves a P-value of 0.788 in the frequency monobit test, significantly exceeding the NIST threshold of 0.01. This means that the output is statistically indistinguishable from random noise. An avalanche effect of 50.13% is observed, demonstrating strong compliance with the avalanche criterion and indicating substantial resistance to differential cryptanalytic attacks. The internal key entropy is enhanced to 6.28 bits. This model provides a robust solution for securing sensitive database records and transaction logs in enterprise environments, as well as ensuring confidentiality without compromising computational efficiency
References
- Frustaci, M., Pace, P., Aloi, G., Fortino, G. (2018). Evaluating Critical Security Issues of the IoT World: Present and Future Challenges. IEEE Internet of Things Journal, 5 (4), 2483–2495. https://doi.org/10.1109/jiot.2017.2767291
- Ali, G., Dida, M. A., Elikana Sam, A. (2021). A Secure and Efficient Multi-Factor Authentication Algorithm for Mobile Money Applications. Future Internet, 13 (12), 299. https://doi.org/10.3390/fi13120299
- Stallings, W. (2020). Cryptography and Network Security: Principles and Practice. Pearson.
- Hill, L. S. (1929). Cryptography in An Algebraic Alphabet. The American Mathematical Monthly, 36 (6), 306–312. https://doi.org/10.1080/00029890.1929.11986963
- Lone, P. N., Singh, D., Stoffová, V., Mishra, D. C., Mir, U. H., Kumar, N. (2022). Cryptanalysis and Improved Image Encryption Scheme Using Elliptic Curve and Affine Hill Cipher. Mathematics, 10 (20), 3878. https://doi.org/10.3390/math10203878
- Barrieta, R. G., Canlas, A. S., Cortez, D. M. A., Mata, K. E. (2022). Modified Hill Cipher Algorithm using Myszkowski Transposition to address Known-Plaintext attack. International Journal for Research in Applied Science and Engineering Technology, 10 (4), 3242–3249. https://doi.org/10.22214/ijraset.2022.41970
- Imam, R., Areeb, Q. M., Alturki, A., Anwer, F. (2021). Systematic and Critical Review of RSA Based Public Key Cryptographic Schemes: Past and Present Status. IEEE Access, 9, 155949–155976. https://doi.org/10.1109/access.2021.3129224
- Bleichenbacher, D. (1998). Chosen ciphertext attacks against protocols based on the RSA encryption standard PKCS #1. Advances in Cryptology – CRYPTO ’98, 1–12. https://doi.org/10.1007/bfb0055716
- Regev, O. (2009). On lattices, learning with errors, random linear codes, and cryptography. Journal of the ACM, 56 (6), 1–40. https://doi.org/10.1145/1568318.1568324
- Lyubashevsky, V., Peikert, C., Regev, O. (2013). On Ideal Lattices and Learning with Errors over Rings. Journal of the ACM, 60 (6), 1–35. https://doi.org/10.1145/2535925
- Sabani, M. E., Savvas, I. K., Garani, G. (2024). Learning with Errors: A Lattice-Based Keystone of Post-Quantum Cryptography. Signals, 5 (2), 216–243. https://doi.org/10.3390/signals5020012
- Schindler, W. (2000). A Timing Attack against RSA with the Chinese Remainder Theorem. Cryptographic Hardware and Embedded Systems – CHES 2000, 109–124. https://doi.org/10.1007/3-540-44499-8_8
- Henecka, W., May, A., Meurer, A. (2010). Correcting Errors in RSA Private Keys. Advances in Cryptology – CRYPTO 2010, 351–369. https://doi.org/10.1007/978-3-642-14623-7_19
- Rivain, M. (2009). Securing RSA against Fault Analysis by Double Addition Chain Exponentiation. Topics in Cryptology – CT-RSA 2009, 459–480. https://doi.org/10.1007/978-3-642-00862-7_31
- Jiang, Z., Zhou, Y., Liu, Y. (2024). New partial key exposure attacks on RSA with additive exponent blinding. Cybersecurity, 7 (1). https://doi.org/10.1186/s42400-024-00214-y
- Zheng, M. (2022). Revisiting the Polynomial-Time Equivalence of Computing the CRT-RSA Secret Key and Factoring. Mathematics, 10 (13), 2238. https://doi.org/10.3390/math10132238
- Venkatraman, S., Overmars, A. (2019). New Method of Prime Factorisation-Based Attacks on RSA Authentication in IoT. Cryptography, 3 (3), 20. https://doi.org/10.3390/cryptography3030020
- Tahat, N., Tahat, A. A., Abu-Dalu, M., Albadarneh, R. B., Abdallah, A. E., Al-Hazaimeh, O. M. (2020). A new RSA public key encryption scheme with chaotic maps. International Journal of Electrical and Computer Engineering (IJECE), 10 (2), 1430. https://doi.org/10.11591/ijece.v10i2.pp1430-1437
- Thiziers, A. H., Cisse, H., T., J., Michel, B. (2019). Enhanced, Modified and Secured RSA Cryptosystem based on n Prime Numbers and Offline Storage for Medical Data Transmission via Mobile Phone. International Journal of Advanced Computer Science and Applications, 10 (10). https://doi.org/10.14569/ijacsa.2019.0101050
- Kamardan, M. G., Aminudin, N., Che-Him, N., Sufahani, S., Khalid, K., Roslan, R. (2018). Modified Multi Prime RSA Cryptosystem. Journal of Physics: Conference Series, 995, 012030. https://doi.org/10.1088/1742-6596/995/1/012030
- Farooq, S., Altaf, A., Iqbal, F., Thompson, E. B., Vargas, D. L. R., Díez, I. de la T., Ashraf, I. (2023). Resilience Optimization of Post-Quantum Cryptography Key Encapsulation Algorithms. Sensors, 23 (12), 5379. https://doi.org/10.3390/s23125379
- Libert, B., Ling, S., Nguyen, K., Wang, H. (2023). Zero-Knowledge Arguments for Lattice-Based Accumulators: Logarithmic-Size Ring Signatures and Group Signatures Without Trapdoors. Journal of Cryptology, 36 (3). https://doi.org/10.1007/s00145-023-09470-6
- Liang, W., Liu, Z., Zhao, X., Yang, Y., Liang, Z. (2024). Flexible and Compact MLWE-Based KEM. Mathematics, 12 (11), 1769. https://doi.org/10.3390/math12111769
- Kieu-Do-Nguyen, B., The Binh, N., Pham-Quoc, C., Nghi, H. P., Tran, N.-T., Hoang, T.-T., Pham, C.-K. (2024). Compact and Low-Latency FPGA-Based Number Theoretic Transform Architecture for CRYSTALS Kyber Postquantum Cryptography Scheme. Information, 15 (7), 400. https://doi.org/10.3390/info15070400
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2026 Mahdianta Pandia, Poltak Sihombing, Mohammad Andri Budiman, Erna Budhiarti Nababan

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





