Devising a method for complex steganographic embedding of information in the structural-psychovisual space
DOI:
https://doi.org/10.15587/1729-4061.2026.351181Keywords:
unmanned aerial systems, infocommunication systems, video-container, redundancy, structural dependences, positional basisAbstract
This study examines the set of processes aimed at improving the efficiency of steganographic methods for information protection, while ensuring a specified level of integrity and timeliness of transmission in infocommunication systems. The work addresses a scientific and applied task of increasing the level of information security while maintaining a specified level of integrity and timely delivery of data from unmanned aerial systems (UASs). It relates to the existence of a contradiction between ensuring the confidentiality of video information and the efficiency of its delivery with a given integrity.
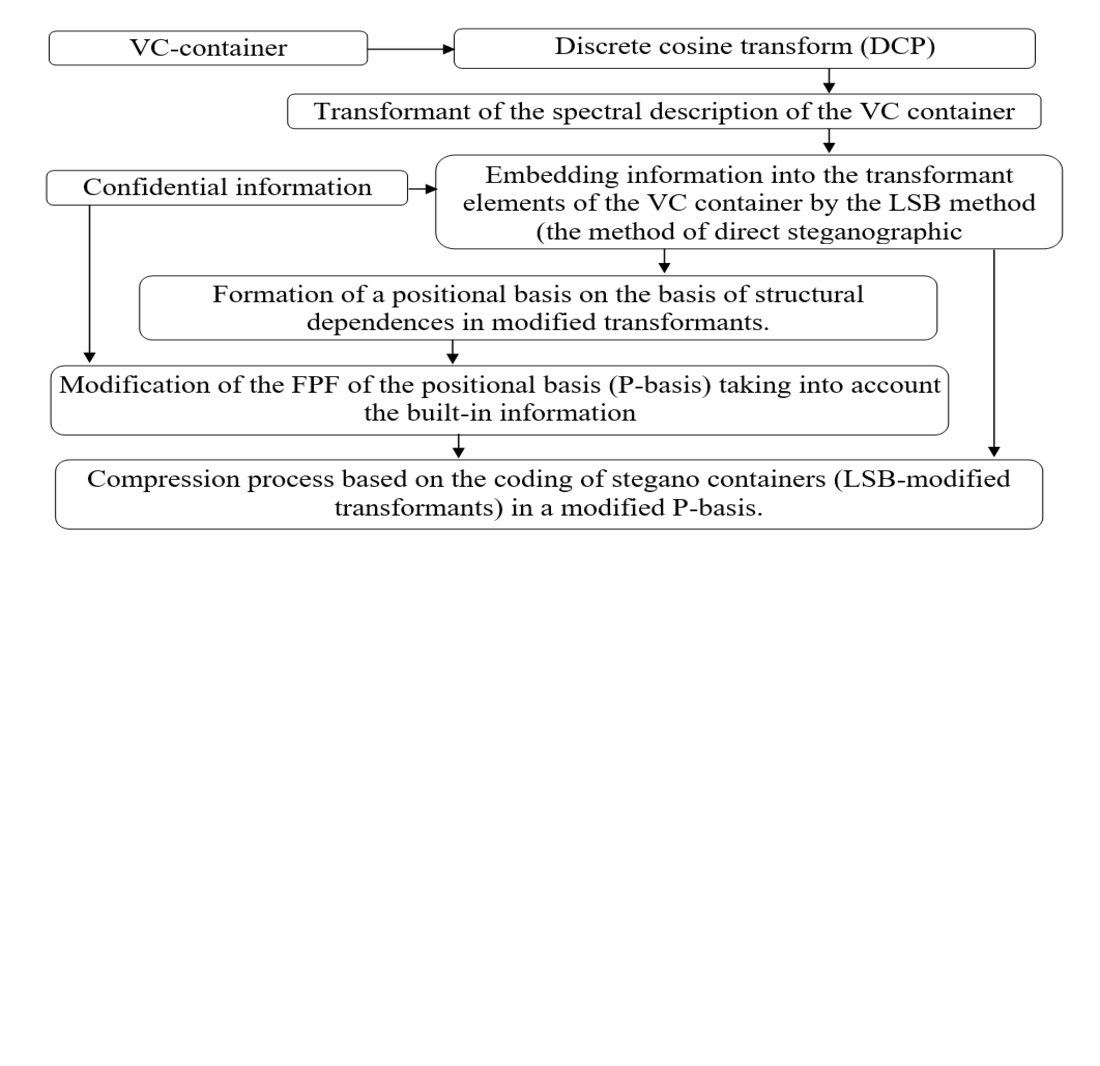
In the process of research, a method for structural steganographic embedding has been devised, based on changing the values of positional basis (PB). The difference is the embedding of information in the process of modifying the PB values, taking into account the detection of structural dependences in the spectrally modified space of a video container (VC). Such transformations are carried out under conditions of reducing the influence of spectral space modifications on the compression level. The above advantages make it possible to build a comprehensive method of steganographic transformations in the process of VC compression.
The method is distinguished by two principal aspects. The first is the use of a sequence of steganographic transformations in independent spaces to detect dependences that are used in the process of embedding information. The second is that information is embedded in the structural-spectral space, taking into account its modification by the youngest bits. This enables increasing the level of steganographic capacity by an average of 7% without distorting the integrity of the stegano-containers and removing hidden information on the receiving side.
The devised method is intended to be used to improve the confidentiality, efficiency, and integrity of video information delivery from unmanned systems
References
- Barannik, V., Lytvinenko, M., Okladnoy, D., Suprun, O. (2017). Description of the OFDM symbol with the help of mathematical laws. Analysis of technologies that were used in this case. 2017 2nd International Conference on Advanced Information and Communication Technologies (AICT), 183–187. https://doi.org/10.1109/aiact.2017.8020095
- Ai, D., Jiang, G., Lam, S.-K., He, P., Li, C. (2023). Computer vision framework for crack detection of civil infrastructure – A review. Engineering Applications of Artificial Intelligence, 117, 105478. https://doi.org/10.1016/j.engappai.2022.105478
- Sharma, R., Bollavarapu, S. (2015). Data Security using Compression and Cryptography Techniques. International Journal of Computer Applications, 117 (14), 15–18. https://doi.org/10.5120/20621-3342
- Barannik, V., Sidchenko, S., Barannik, D., Shulgin, S., Barannik, V., Datsun, A. (2021). Devising a conceptual method for generating cryptocompression codograms of images without loss of information quality. Eastern-European Journal of Enterprise Technologies, 4 (2 (112)), 6–17. https://doi.org/10.15587/1729-4061.2021.237359
- Chanda D’Layla, A. W., Nevin, M., Sunardi Putra, G. G., de La Croix, N. J., Ahmad, T. (2023). Steganography in Grayscale Images: Improving the Quality of a Stego Image. 2023 3rd International Conference on Smart Generation Computing, Communication and Networking (SMART GENCON), 1–6. https://doi.org/10.1109/smartgencon60755.2023.10442310
- Dipankar, D. (2025). Comparative Analysis Of Steganographic Techniques For Data Hiding In Digital Images. figshare. Journal contribution. https://doi.org/10.6084/m9.figshare.30621860.v1
- Rizal, R., Rahmatulloh, A., Widiyasono, N., R, R., Nursamsi, D. R. (2023). Steganography: Combination of Least Significant Bit (LSB) and Bit-Plane Complexity Segmentation (BPCS) Methods for Hiding Massage on Image and Audio. International Journal of Computer Applications, 185 (21), 1–7. https://doi.org/10.5120/ijca2023922929
- Hama, H. K., Ahmed, A., Hassan, B. A., Abdullah, A. A. (2025). Hybrid Encryption and Steganography for Secure Image Data Hiding. UHD Journal of Science and Technology, 9 (2), 287–296. https://doi.org/10.21928/uhdjst.v9n2y2025.pp287-296
- Emad, E., Safey, A., Refaat, A., Osama, Z., Sayed, E., Mohamed, E. (2018). A secure image steganography algorithm based on least significant bit and integer wavelet transform. Journal of Systems Engineering and Electronics, 29 (3), 639. https://doi.org/10.21629/jsee.2018.03.21
- Ravindra, A., Bansod, S., Singh, S. K. (2025). LSB-Based Image Steganography Using Image Enlargement. 2025 International Conference on Computing Technologies (ICOCT), 1–4. https://doi.org/10.1109/icoct64433.2025.11118799
- Majumder, J., Pradhan, C. (2022). An interpolation based steganographic technique with least-significant-bit and pixel value differencing in a pixel block. Indonesian Journal of Electrical Engineering and Computer Science, 27 (2), 1074. https://doi.org/10.11591/ijeecs.v27.i2.pp1074-1082
- Théophile, I., De La Croix, N. J., Ahmad, T. (2023). Fuzzy Logic-based Steganographic Scheme for high Payload Capacity with high Imperceptibility. 2023 11th International Symposium on Digital Forensics and Security (ISDFS), 1–6. https://doi.org/10.1109/isdfs58141.2023.10131727
- Chen, Z.-Q., Huang, Y.-H., Chen, X.-Y., Lo, S.-L. (2025). ADPGAN: Anti-Compression Attention-Based Diffusion Pattern Steganography Model Using GAN. Electronics, 14 (22), 4426. https://doi.org/10.3390/electronics14224426
- Tan, L., Li, Y., Zeng, Y., Chen, P. (2025). An Adaptive JPEG Steganography Algorithm Based on the UT-GAN Model. Electronics, 14 (20), 4046. https://doi.org/10.3390/electronics14204046
- Barannik, D., Barannik, V. (2022). Steganographic Coding Technology for Hiding Information in Infocommunication Systems of Critical Infrastructure. 2022 IEEE 4th International Conference on Advanced Trends in Information Theory (ATIT), 88–91. https://doi.org/10.1109/atit58178.2022.10024185
- Gonzalez, R., Woods, R. (2018). Digital Image Processing. Pearson, 1022. Available at: https://www.scirp.org/reference/referencespapers?referenceid=3227103
- Radosavljević, M., Brkljač, B., Lugonja, P., Crnojević, V., Trpovski, Ž., Xiong, Z., Vukobratović, D. (2020). Lossy Compression of Multispectral Satellite Images with Application to Crop Thematic Mapping: A HEVC Comparative Study. Remote Sensing, 12 (10), 1590. https://doi.org/10.3390/rs12101590
- Barannik, V., Ryabukha, Y., Barannik, N., Barannik, D. (2020). Indirect Steganographic Embedding Method Based on Modifications of the Basis of the Polyadic System. 2020 IEEE 15th International Conference on Advanced Trends in Radioelectronics, Telecommunications and Computer Engineering (TCSET), 699–702. https://doi.org/10.1109/tcset49122.2020.235522
- Barannik, V., Shulgin, S., Barannik, N., Barannik, V. (2022). Method of Coding Subbands of Non-Homogeneous Spectrum of Video Segments in Uneven Diagonal Space. 2022 IEEE 4th International Conference on Advanced Trends in Information Theory (ATIT), 72–75. https://doi.org/10.1109/atit58178.2022.10024236
- Ponomarenko, N., Jin, L., Ieremeiev, O., Lukin, V., Egiazarian, K., Astola, J. et al. (2015). Image database TID2013: Peculiarities, results and perspectives. Signal Processing: Image Communication, 30, 57–77. https://doi.org/10.1016/j.image.2014.10.009
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2026 Vladimir Barannik, Dmitry Barannik, Mykhailo Babenko, Rodion Prokopenko, Oleksandr Akimov, Nina Petrukha

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





