Development of a method for improving the efficiency of transaction classification in the Bitcoin network using an attention mechanism in graph neural networks
DOI:
https://doi.org/10.15587/1729-4061.2026.351685Keywords:
blockchain, BitcoinHeist, GATv2, graph neural networks, transfer learning, active learningAbstract
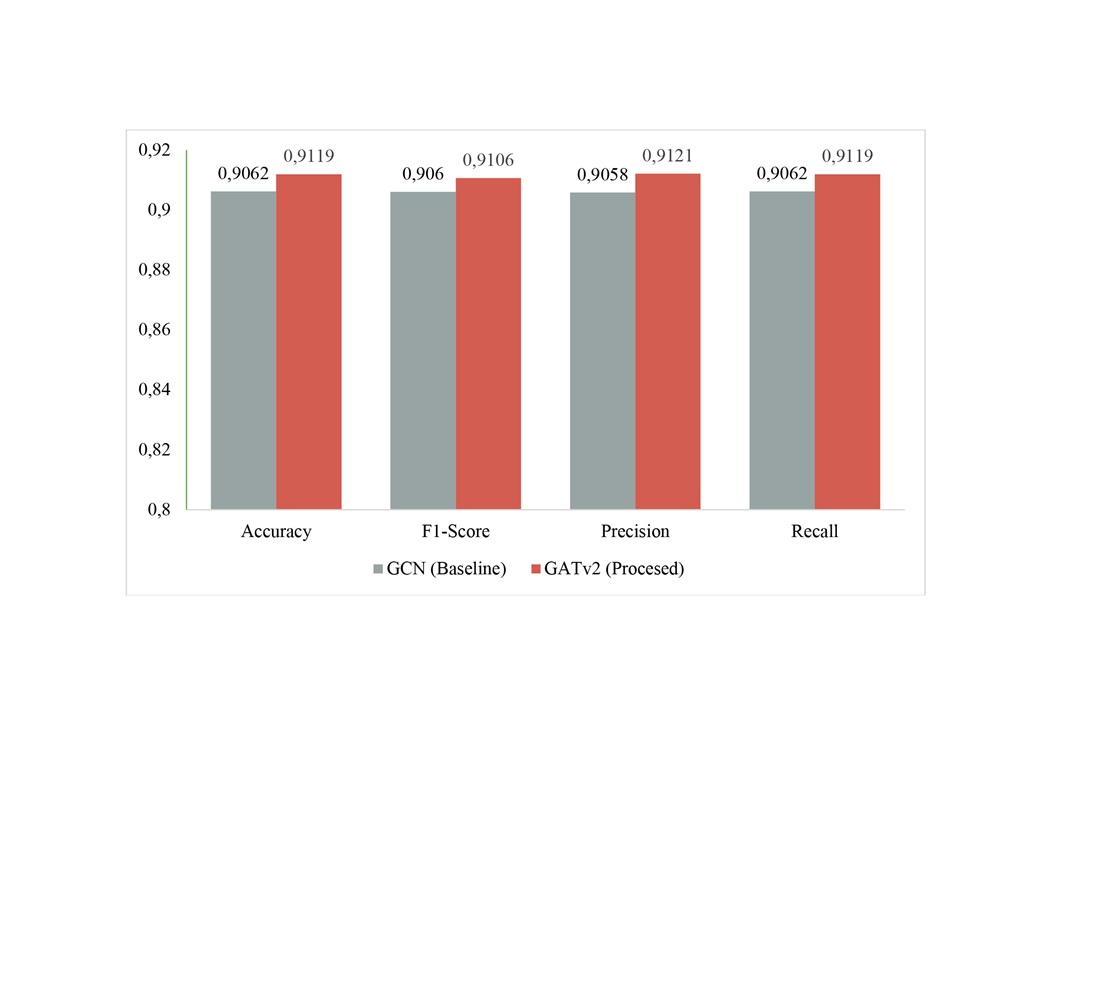
The object of the study is the processes of automated transaction classification and Bitcoin address identification for detecting malicious activity in conditions of pseudo-anonymity. The problem is the insufficient effectiveness of algorithms, such as graph convolutional networks, in conditions of strong class imbalance. This discovery is particularly important when less than ten percent of the data is clearly labelled. However, the main difficulty is excessive feature smoothing, which complicates the effective detection of anomalies for dense graphs. The results confirm that the Graph Attention Network v2 (GATv2) model is effective. It achieves an accuracy of 91.19% and an F1 score of 91.11% in testing. In addition, the stability of the approach is confirmed when 15% of topological noise is added to the graph structure. To prove the selectivity of the classifier, the Area Under the Curve (AUC) value of the approach is 0.889. The results are explained by the implementation of a dynamic anisotropic aggregation mechanism that adaptively distributes attention weights. This allows selectively amplifying weak signals of suspicious transactions while ignoring irrelevant connections and noise. A distinctive feature is the model of feature unification through logarithmic normalization of sums and non-linear processing of time intervals. Its uniqueness lies in the use of weighted loss functions and active learning strategies on boundary samples. Two-level transfer learning was applied to the Elliptic and BitcoinHeist datasets. The area of application is integration into real-time anti-money laundering (AML) systems. The approach allows overcoming conceptual shifts when new types of cyber threats emerge. The method detects the activity of CryptoLocker-type extortionists in the absence of data
References
- Akcora, C. G., Li, Y., Gel, Y. R., Kantarcioglu, M. (2020). BitcoinHeist: Topological Data Analysis for Ransomware Prediction on the Bitcoin Blockchain. Proceedings of the Twenty-Ninth International Joint Conference on Artificial Intelligence, 4439–4445. https://doi.org/10.24963/ijcai.2020/612
- Weber, M., Domeniconi, G., Chen, J., Weidele, D. K. I., Bellei, C., Robinson, T., Leiserson, C. E. (2019). Anti-Money Laundering in Bitcoin: Experimenting with Graph Convolutional Networks for Financial Forensics. arXiv. https://doi.org/10.48550/arXiv.1908.02591
- Bitcoin Heist Ransomware Address [Dataset] (2020). UCI Machine Learning Repository. https://doi.org/10.24432/C5BG8V
- Lorenz, J., Silva, M. I., Aparício, D., Ascensão, J. T., Bizarro, P. (2020). Machine learning methods to detect money laundering in the bitcoin blockchain in the presence of label scarcity. Proceedings of the First ACM International Conference on AI in Finance, 1–8. https://doi.org/10.1145/3383455.3422549
- Vassallo, D., Vella, V., Ellul, J. (2021). Application of Gradient Boosting Algorithms for Anti-money Laundering in Cryptocurrencies. SN Computer Science, 2 (3). https://doi.org/10.1007/s42979-021-00558-z
- Alarab, I., Prakoonwit, S., Nacer, M. I. (2020). Competence of Graph Convolutional Networks for Anti-Money Laundering in Bitcoin Blockchain. Proceedings of the 2020 5th International Conference on Machine Learning Technologies, 23–27. https://doi.org/10.1145/3409073.3409080
- Kipf, T. N., Welling, M. (2016). Semi-supervised classification with graph convolutional networks. arXiv. https://doi.org/10.48550/arXiv.1609.02907
- Veličković, P., Cucurull, G., Casanova, A., Romero, A., Lio, P., Bengio, Y. (2017). Graph attention networks. arXiv. https://doi.org/10.48550/arXiv.1710.10903
- Brody, S., Alon, U., Yahav, E. (2021). How attentive are graph attention networks? arXiv. https://doi.org/10.48550/arXiv.2105.14491
- Li, G., Tang, X. (2024). Exploring GCN, GAT, and GIN Fusion for Illicit Transaction Classification in Cryptocurrency Networks. Proceedings of the 2024 the 12th International Conference on Information Technology (ICIT), 49–53. https://doi.org/10.1145/3718391.3718399
- Rekik, S., Mehmood, S. (2025). A Hybrid Graph Neural Network and Neural ODE Model to Intrusion Detection in Dynamic Network Topologies. IEEE Access, 13, 198201–198227. https://doi.org/10.1109/access.2025.3635385
- Zhao, H., Liu, W., Gao, C., Shi, W., Zhang, Z., Chen, J. (2025). HGAA: A Heterogeneous Graph Adaptive Augmentation Method for Asymmetric Datasets. Symmetry, 17 (10), 1623. https://doi.org/10.3390/sym17101623
- Luša, R., Pintar, D., Vranić, M. (2025). TE-G-SAGE: Explainable Edge-Aware Graph Neural Networks for Network Intrusion Detection. Modelling, 6 (4), 165. https://doi.org/10.3390/modelling6040165
- H. G., M., Kumar, J., Mm, N. (2025). GrMA-CNN: Integrating Spatial-Spectral Layers with Modified Attention for Botnet Detection Using Graph Convolution for Securing Networks. International Journal of Intelligent Engineering and Systems, 18 (1), 1009. https://doi.org/10.22266/ijies2025.0229.72
- Hamilton, W., Ying, Z., Leskovec, J. (2017). Inductive representation learning on large graphs. arXiv. https://doi.org/10.48550/arXiv.1706.02216
- Ding, K., Li, J., Bhanushali, R., Liu, H. (2019). Deep Anomaly Detection on Attributed Networks. Proceedings of the 2019 SIAM International Conference on Data Mining, 594–602. https://doi.org/10.1137/1.9781611975673.67
- Lo, W. W., Kulatilleke, G. K., Sarhan, M., Layeghy, S., Portmann, M. (2023). Inspection-L: self-supervised GNN node embeddings for money laundering detection in bitcoin. Applied Intelligence, 53 (16), 19406–19417. https://doi.org/10.1007/s10489-023-04504-9
- Ma, X., Wu, J., Xue, S., Yang, J., Zhou, C., Sheng, Q. Z. et al. (2023). A Comprehensive Survey on Graph Anomaly Detection With Deep Learning. IEEE Transactions on Knowledge and Data Engineering, 35 (12), 12012–12038. https://doi.org/10.1109/tkde.2021.3118815
- Elliptic Data Set. Kaggle. Available at: https://www.kaggle.com/datasets/ellipticco/elliptic-data-set
- Ren, P., Xiao, Y., Chang, X., Huang, P.-Y., Li, Z., Gupta, B. B. et al. (2021). A Survey of Deep Active Learning. ACM Computing Surveys, 54 (9), 1–40. https://doi.org/10.1145/3472291
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2026 Oleksandr Kushnerov, Vladyslav Prosolov, Valerii Dudykevych, Serhii Yevseiev, Serhii Povaliaiev, Yevheniia Ivanchenko, Volodymyr Gorbulyk, Oleksandr Chechui, Dmytro Balagura, Vladyslav Sukhoteplyi

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





