Features extraction of fingerprints based on hybrid particle swarm optimization and bat algorithms
DOI:
https://doi.org/10.15587/1729-4061.2022.266259Keywords:
image processing, biometrics, fingerprint, features extraction, minutiae, binarization, thinning, swarm intelligence, particle swarm optimization, bat algorithmAbstract
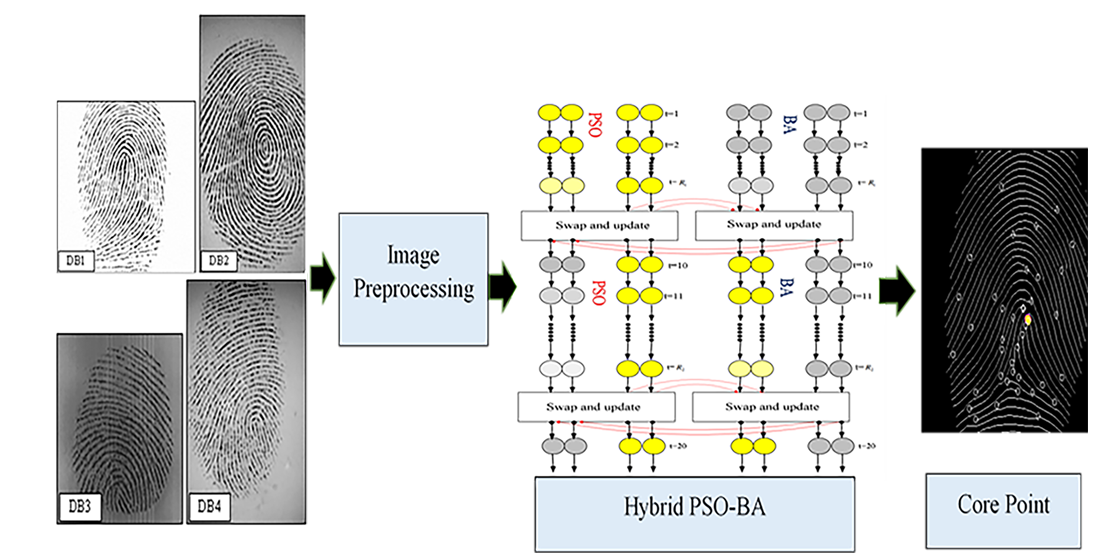
Most security system's essential errand is to check that the people are in fact who they claim to be. In Contrast to traditional techniques such as passwords and smart cards that are used in some organizations, fingerprint identification may be preferred as it makes the information virtually impossible to steal. The most extensive used biometric features are Fingerprints, in order to identify a person because of their uniqueness and invariance. The fingerprint consists of valleys and ridges on the surface of a fingertip. In this paper, a new hybrid strategy Particle Swarm Optimization (PSO) with Bat Algorithm (BA) is proposed to extract features from fingerprint images. Both PSO and BA algorithms are swarm-based algorithms that mimics the swarm behaviour of particles and bats in nature. In the field of image processing, features are extremely significant. Before obtaining features, the noisy area should be removed from the foreground first, and then several important techniques are applied on each sample image in the database such as Fingerprint Enhancement by using Fast Fourier Transform (FFT), Binarization, and Thinning. The hybrid (PSO-BA) algorithm is proposed as a pre-enhancing step to select the clear minutiae (or feature) structures across several iterations, which will be more suited for the matching phase. By comparing the proposed method with several methods in calculating FAR and FRR, the results showed that the FAR (0.001) and FRR (0.01) were less than the other proposed methods. That means the hybrid (PSO-BA) algorithm has the better results, which means it can be used as one of the best search approaches to extract features from fingerprints
References
- Tarjoman, M., Zarei, S. (2008). Automatic fingerprint classification using graph theory. In Proceedings of world academy of science, engineering and technology.
- Al-Ta’l, Z. T. M., Abdulhameed, O. Y. (2013). Features extraction of fingerprints using firefly algorithm. Proceedings of the 6th International Conference on Security of Information and Networks - SIN ’13. doi: https://doi.org/10.1145/2523514.2527014
- Zhang, D. D. (2000). Automated biometrics: Technologies and systems. Springer, 332. doi: https://doi.org/10.1007/978-1-4615-4519-4
- Ravi, J., Raja, K. B., Venugopal, K. R. (2009). Fingerprint recognition using minutia score matching. International Journal of Engineering Science and Technology, 1 (2), 35–42. doi: https://doi.org/10.48550/arXiv.1001.4186
- Abed, H. N., Ahmed, A. L., Hassoon, N. H., Albayaty, I. S. (2018). Hiding Information In An Image Based On Bats Algorithm. Iraqi Journal of Information Technology, 8 (2). doi: https://doi.org/10.34279/0923-008-002-011
- Bonabeau, E., Dorigo, M., Theraulaz, G. (1999). Swarm intelligence: from natural to artificial systems. Oxford Academic. doi: https://doi.org/10.1093/oso/9780195131581.001.0001
- Teodorovic´, D. (2003). Transport modeling by multi-agent systems: a swarm intelligence approach. Transportation Planning and Technology, 26 (4), 289–312. doi: https://doi.org/10.1080/0308106032000154593
- Al-Sahaf, H., Al-Sahaf, A., Xue, B., Johnston, M., Zhang, M. (2016). Automatically Evolving Rotation-invariant Texture Image Descriptors by Genetic Programming. IEEE Transactions on Evolutionary Computation. doi: https://doi.org/10.1109/tevc.2016.2577548
- Al-Sahaf, H., Song, A., Neshatian, K., Zhang, M. (2012). Two-Tier genetic programming: towards raw pixel-based image classification. Expert Systems with Applications, 39 (16), 12291–12301. doi: https://doi.org/10.1016/j.eswa.2012.02.123
- Albukhanajer, W. A., Briffa, J. A., Yaochu Jin. (2015). Evolutionary Multiobjective Image Feature Extraction in the Presence of Noise. IEEE Transactions on Cybernetics, 45 (9), 1757–1768. doi: https://doi.org/10.1109/tcyb.2014.2360074
- Mahmoodi, S. (2012). Edge Detection Filter based on Mumford–Shah Green Function. SIAM Journal on Imaging Sciences, 5 (1), 343–365. doi: https://doi.org/10.1137/100811349
- Athira Lekshmi, B. A., Linsely, J. A., Queen, M. P. F., Babu Aurtherson, P. (2018). Feature Extraction and Image Classification Using Particle Swarm Optimization by Evolving Rotation-Invariant Image Descriptors. 2018 International Conference on Emerging Trends and Innovations In Engineering And Technological Research (ICETIETR). doi: https://doi.org/10.1109/icetietr.2018.8529083
- Kareem Rasheed, M., Dawood, A. J. (2019). A new card authentication schema based on embed fingerprint in image watermarking and encryption. Journal of Theoretical and Applied Information Technology, 97 (3), 1018–1029. Available at: http://www.jatit.org/volumes/Vol97No3/26Vol97No3.pdf
- Maio, D., Maltoni, D., Cappelli, R., Wayman, J. L., Jain, A. K. (2004). FVC2004: Third Fingerprint Verification Competition. Lecture Notes in Computer Science, 1–7. doi: https://doi.org/10.1007/978-3-540-25948-0_1
- Pan, T.-S., Dao, T.-K., Nguyen, T.-T., Chu, S.-C. (2015). Hybrid Particle Swarm Optimization with Bat Algorithm. Genetic and Evolutionary Computing, 37–47. doi: https://doi.org/10.1007/978-3-319-12286-1_5
- Liao, M., Wan, Z., Yao, C., Chen, K., Bai, X. (2020). Real-Time Scene Text Detection with Differentiable Binarization. Proceedings of the AAAI Conference on Artificial Intelligence, 34 (07), 11474–11481. doi: https://doi.org/10.1609/aaai.v34i07.6812
- Mingote, V., Miguel, A., Ribas, D., Ortega, A., Lleida, E. (2019). Optimization of False Acceptance/Rejection Rates and Decision Threshold for End-to-End Text-Dependent Speaker Verification Systems. Interspeech 2019. doi: https://doi.org/10.21437/interspeech.2019-2550
- Ali, Mouad. M. H., Mahale, V. H., Yannawar, P., Gaikwad, A. T. (2016). Fingerprint Recognition for Person Identification and Verification Based on Minutiae Matching. 2016 IEEE 6th International Conference on Advanced Computing (IACC). doi: https://doi.org/10.1109/iacc.2016.69
- Rao, G. S., NagaRaju, C., Reddy, L. S. S., Prasad, E. V. (2008). A novel fingerprints identification system based on the edge detection. International Journal of Computer Science and Network Security, 8 (12), 394–397. Available at: http://paper.ijcsns.org/07_book/200812/20081256.pdf
- Kukula, E. P., Blomeke, C. R., Modi, S. K., Elliott, S. J. (2009). Effect of human-biometric sensor interaction on fingerprint matching performance, image quality and minutiae count. International Journal of Computer Applications in Technology, 34 (4), 270. doi: https://doi.org/10.1504/ijcat.2009.024079
- Cao, K., Yang, X., Chen, X., Zang, Y., Liang, J., Tian, J. (2012). A novel ant colony optimization algorithm for large-distorted fingerprint matching. Pattern Recognition, 45 (1), 151–161. doi: https://doi.org/10.1016/j.patcog.2011.04.016
- He, Y., Tian, J., Luo, X., Zhang, T. (2003). Image enhancement and minutiae matching in fingerprint verification. Pattern Recognition Letters, 24 (9-10), 1349–1360. doi: https://doi.org/10.1016/s0167-8655(02)00376-8
- Chaudhari, A. S., Patnaik, G. K., Patil, S. S. (2014). Implementation of Minutiae Based Fingerprint Identification System Using Crossing Number Concept. Informatica Economica, 18 (1), 17–26. doi: https://doi.org/10.12948/issn14531305/18.1.2014.02
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2022 Ahmed LuayAhmed, Noor Hassoon, Layla AL.hak, Mahdi Edan, Hazim Abed, Sura Abd

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





