Design and implement a real-time network traffic management system using SNMP protocol
DOI:
https://doi.org/10.15587/1729-4061.2023.286528Keywords:
SNMP, Real-time monitoring and management system, MIB, Traffic server managementAbstract
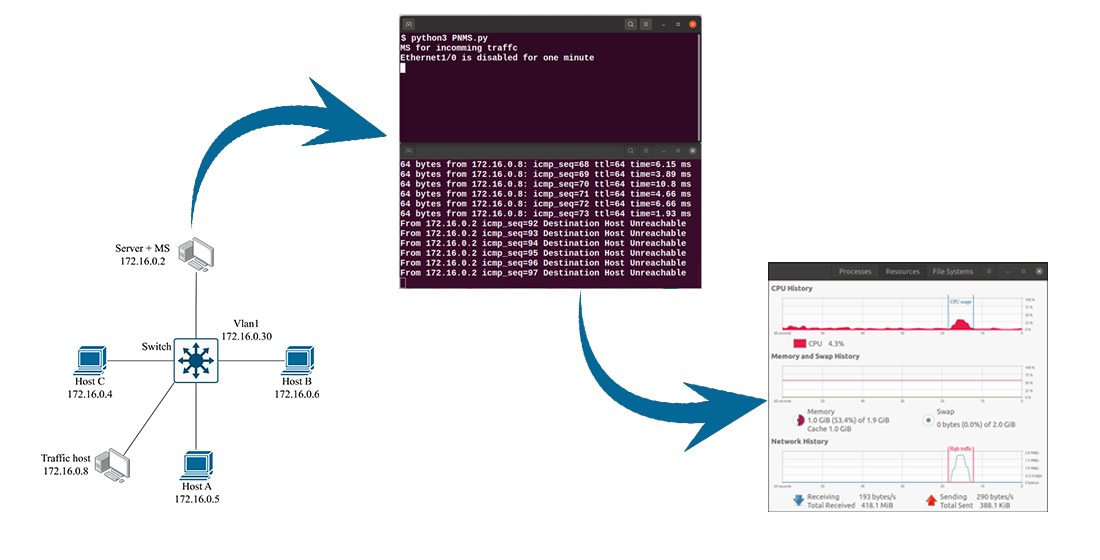
The research focuses on designing and implementing a system for managing incoming server traffic using the Simple Network Management Protocol (SNMP). The essence of the method is to provide a real-time monitoring system that empowers network managers to oversee all network activities efficiently. The key difference of the developed system lies in using the SNMP protocol to monitor and control the network without needing a third-party tool. The proposed approach addresses administrators' common network challenges, including inefficient bandwidth utilization and complex network resource monitoring. Upon implementation, the system gathered essential network equipment information from the Management Information Base (MIB). The research results indicate that the SNMP-based network management system prevents network devices from reaching their allotted bandwidth limits. The system notably reduces CPU utilization from 28 % to 8 % and decreases bandwidth usage from 1.7 MiB/s to 260 bytes/s. Additionally, the system's alerting capability enhances the network's resilience against incoming traffic anomalies that may otherwise interrupt server operations. An example of using the proposed system to manage incoming server traffic in small networks. It has several practical uses in managing and maintaining network infrastructure in different fields. Also, it enables real-time monitoring of network devices, resource management, fault detection, and performance optimization. The system can be used in small organizations to monitor network performance, track faults, and manage network resources efficiently. In addition, SNMP-based network monitoring systems can find applications in almost any field where networked devices and infrastructure require monitoring, management, and optimization
References
- Saarikko, T., Westergren, U. H., Blomquist, T. (2017). The Internet of Things: Are you ready for what’s coming? Business Horizons, 60 (5), 667–676. doi: https://doi.org/10.1016/j.bushor.2017.05.010
- Mjhool, A. Y., Alsabah, R., Aljshamee, M., Alajwadi, M., Al-Sabbagh, A. (2021). E-learning Trends and Internet challenges in Iraq. International Journal of Computing and Digital Systems, 10 (1), 1407–1414. doi: https://doi.org/10.12785/ijcds/1001124
- Aitymova, A., Shaporeva, A., Kopnova, O., Kushumbayev, A., Aitymov, Z. (2022). Development and modeling of combined components of the information environment. Eastern-European Journal of Enterprise Technologies, 2 (2 (116)), 51–60. doi: https://doi.org/10.15587/1729-4061.2022.255084
- Wairisal, M., Surantha, N. (2018). Design and Evaluation of Efficient Bandwidth Management for a Corporate Network. 2018 International Conference on Information Management and Technology (ICIMTech). doi: https://doi.org/10.1109/icimtech.2018.8528162
- Namee, K., Vantaneeyakul, C., Polpinij, J., Albadrani, G. M., Namee, S. (2020). Integration of Cloud Computing with Internet of Things for Network Management and Performance Monitoring. 2020 18th International Conference on ICT and Knowledge Engineering (ICT&KE). doi: https://doi.org/10.1109/ictke50349.2020.9289876
- Chris, H. (2019). What’s Not So Simple about SNMP? Information Security Management, 93–106. doi: https://doi.org/10.1201/9781351073547-8
- S, K. E., A, L. A. S. I., Widiartha, I. B. K. (2016). Perancangan Network Monitoring Tools Menggunakan Autonomous Agent Java. Lontar Komputer : Jurnal Ilmiah Teknologi Informasi, 7 (2), 115–121. doi: https://doi.org/10.24843/lkjiti.2016.v07.i02.p05
- Miftah, Z. (2019). Penerapan sistem monitoring jaringan dengan protokol snmp pada router mikrotik dan aplikasi dude studi kasus stikom cki. Faktor Exacta, 12 (1), 58. doi: https://doi.org/10.30998/faktorexacta.v12i1.3481
- Buchyk, S., Yudin, O., Ziubina, R., Bondarenko, I., Suprun, O. (2021). Devising a method of protection against zero-day attacks based on an analytical model of changing the state of the network sandbox. Eastern-European Journal of Enterprise Technologies, 1 (9 (109)), 50–57. doi: https://doi.org/10.15587/1729-4061.2021.225646
- Majidha Fathima, K. M. (2021). A Survey of the Exemplary Practices in Network Operations and Management. Algorithms for Intelligent Systems, 181–194. doi: https://doi.org/10.1007/978-981-15-8530-2_14
- Espinel Villalobos, R. I., Ardila Triana, E., Zarate Ceballos, H., Ortiz Triviño, J. E. (2021). Design and Implementation of Network Monitoring System for Campus Infrastructure Using Software Agents. Ingeniería e Investigación, 42 (1), e87564. doi: https://doi.org/10.15446/ing.investig.v42n1.87564
- Falih Kadhim, M., Al-Janabi, A., Hazim Alhilali, A., Salih Ali, N. (2022). Security approach for instant messaging applications: viber as a case study. Indonesian Journal of Electrical Engineering and Computer Science, 26 (2), 1109. doi: https://doi.org/10.11591/ijeecs.v26.i2.pp1109-1115
- Rasyiidin, M. Y. B., Murad, F. A., Murad, F. A. (2021). Monitoring Server Berbasis SNMP Menggunakan Cacti pada Server Lokal. Jurnal Ilmiah FIFO, 13 (1), 14. doi: https://doi.org/10.22441/fifo.2021.v13i1.002
- Matoušek, P., Ryšavý, O., Polčák, L. (2021). Unified SNMP Interface for IoT Monitoring. In 2021 IFIP/IEEE International Symposium on Integrated Network Management (IM), 938–943. Available at: http://dl.ifip.org/db/conf/im/im2021-ws3-manage-iot/213211.pdf
- Li, H. (2019). Design and Implementation of Spacecraft Network Monitoring System based on SNMP. 2019 IEEE 3rd Advanced Information Management, Communicates, Electronic and Automation Control Conference (IMCEC). doi: https://doi.org/10.1109/imcec46724.2019.8983796
- Da Costa, E., Mesquita, S. (2022). Computer Network Management and Monitoring System With SNMP and QoS Approach. Timor-Leste Journal of Engineering and Science, 3 (1), 19–27. Available at: https://tljes.org/index.php/tljes/article/download/30/13
- Barannik, V., Sidchenko, S., Barannik, N., Barannik, V. (2021). Development of the method for encoding service data in cryptocompression image representation systems. Eastern-European Journal of Enterprise Technologies, 3 (9 (111)), 103–115. doi: https://doi.org/10.15587/1729-4061.2021.235521
- Madi, N., Al-kasassbeh, M. (2019). Collecting MIB data from network managed by SNMP using multi mobile agents. arXiv. doi: https://doi.org/10.48550/arXiv.1909.02547
- Safrianti, E., Sari, L. O., Sari, N. A. (2021). Real-Time Network Device Monitoring System with Simple Network Management Protocol (SNMP) Model. 2021 3rd International Conference on Research and Academic Community Services (ICRACOS). doi: https://doi.org/10.1109/icracos53680.2021.9701973
- Sheeraz, M., Paracha, M. A., Haque, M. U., Durad, M. H., Mohsin, S. M., Band, S. S., Mosavi, A. (2023). Effective Security Monitoring Using Efficient SIEM Architecture. Human-centric Computing and Information Sciences, 13. doi: https://doi.org/10.22967/HCIS.2023.13.023
- Valencic, D., Mateljan, V. (2019). Implementation of NETCONF Protocol. 2019 42nd International Convention on Information and Communication Technology, Electronics and Microelectronics (MIPRO). doi: https://doi.org/10.23919/mipro.2019.8756925
- Maulana, F. (2016). Implementasi Simple Network Management Protocol (Snmp) Pada Aplikasi Monitoring Jaringan Berbasis Website(Studi Kasus Universitas Muhammadiyah Bengkulu). Jurnal Informatika, 16 (2), 126–135. Available at: https://jurnal.darmajaya.ac.id/index.php/JurnalInformatika/article/view/947/pdf
- The SNMP architecture. IBM. Available at: https://www.ibm.com/docs/en/informix-servers/14.10?topic=concepts-snmp-architecture
- Nidhishree, G., Manimala, S. (2017). Design and Implementation of SNMP based Network Device Monitoring System. International Journal of Trend in Research and Development (IJTRD), 4 (3), 383–385. Available at: http://www.ijtrd.com/ViewFullText.aspx?Id=9632
- Hammood, N. H., Al-Musawi, B., Alhilali, A. H. (2022). A Survey of BGP Anomaly Detection Using Machine Learning Techniques. Communications in Computer and Information Science, 109–120. doi: https://doi.org/10.1007/978-981-19-1166-8_9
- Global OID reference database. Available at: https://oidref.com/
- SNMP MIB. Oracle. Available at: https://docs.oracle.com/cd/E13203_01/tuxedo/tux91/snmpmref/1tmib.htm
- Lee, H.-J. (2023). Dynamic Context Awareness of Universal Middleware based for IoT SNMP Service Platform. Tehnički Glasnik, 17 (2), 185–191. doi: https://doi.org/10.31803/tg-20221221115431
- Simulating Network Architectures with GNS3 (2020). Systems and Network Infrastructure Integration, 9–25. doi: https://doi.org/10.1002/9781119779964.ch2
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2023 Ahmed Hazim Alhilali, Ali Al Farawn, Ahmed Yaseen Mjhool

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





