Developing a method for the detection and identification of rootstock blockchain network nodes
DOI:
https://doi.org/10.15587/1729-4061.2024.297903Keywords:
peer discovery, network crawling, peer-to-peer networks, Rootstock blockchain, Kademlia, decentralizationAbstract
The object of this study is the protocol for detecting nodes in the Rootstock blockchain network and crawling tools. Node discovery protocols are the foundation of any decentralized peer-to-peer network. In blockchain systems, full nodes store and maintain a complete copy of all transactions performed in the network. However, they do not store information about all other nodes, such as their IDs or IP addresses. Each node usually maintains an incomplete list of nodes to which it connects to exchange blockchain data. In decentralized networks, nodes join and leave the network and their IP addresses can change, making it impractical to maintain a complete, up-to-date list of all nodes. Therefore, the only way to get a list of all nodes in the network is to poll each node sequentially.
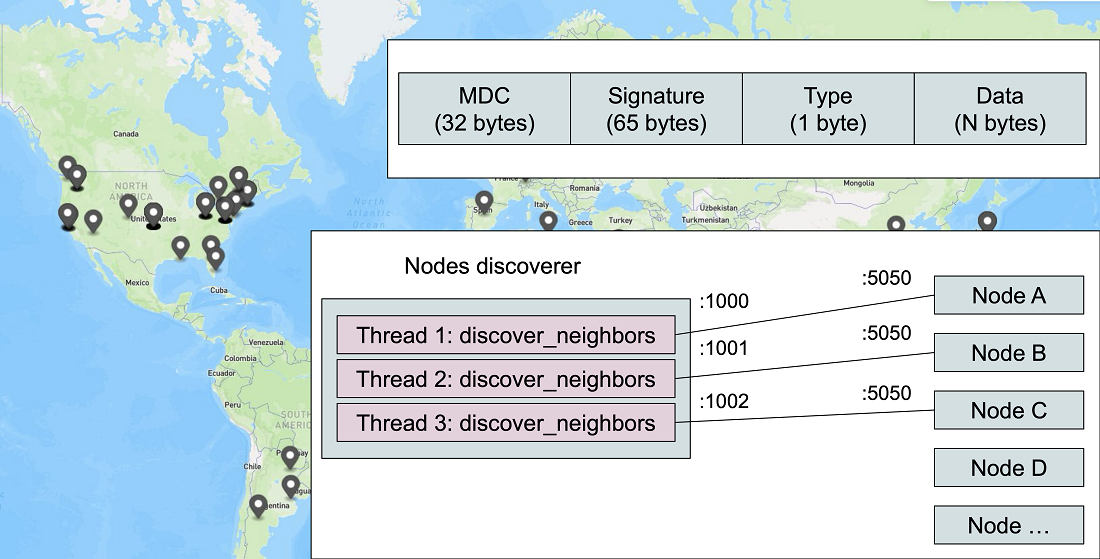
The developed method involves sending specially formed messages to nodes to obtain their neighbors. The graph search algorithm is used to traverse all received neighboring nodes. This allows one to consistently detect all network nodes. Identifying the desired sequence of messages requires a preliminary analysis of the node software RSKj in the part of node discovery protocol.
Effectiveness of the proposed method was verified using the developed software and an experiment in the main network. 6 verification nodes were deployed in different physical locations and at different times. All test nodes were detected in less than 10 minutes. The developed method found 222 nodes that have 209 unique IP addresses.
Results of this study show how to perform analysis of node discovery protocol. They provide the means to obtain information about the available nodes of the Rootstock blockchain system, enabling the analysis of both the blockchain network in general and individual node
References
- Dorogiy, Y., Kolisnichenko, V. (2023). Application of logging in various participants of blockchain networks for de-anonymization of the end user. Herald of Khmelnytskyi national university, 1 (5), 60–66. Available at: http://journals.khnu.km.ua/vestnik/?p=20028
- Ethereum staking. Available at: https://ethereum.org/staking
- Smart contracts secured by Bitcoin. Available at: https://rootstock.io/
- Lerner, S. D. (2020). Building the Most Secure, Permissionless and Uncensorable Bitcoin Peg. Available at: https://medium.com/iovlabs-innovation-stories/building-the-most-secure-permissionless-and-uncensorable-bitcoin-peg-b5dc7020e5ec
- Howell, A., Saber, T., Bendechache, M. (2023). Measuring node decentralisation in blockchain peer to peer networks. Blockchain: Research and Applications, 4 (1), 100109. https://doi.org/10.1016/j.bcra.2022.100109
- Grundmann, M., Amberg, H., Hartenstein, H. (2021). On the Estimation of the Number of Unreachable Peers in the Bitcoin P2P Network by Observation of Peer Announcements. arXiv. Available at: https://doi.org/10.48550/ARXIV.2102.12774
- Eisenbarth, J.-P., Cholez, T., Perrin, O. (2022). Ethereum’s Peer-to-Peer Network Monitoring and Sybil Attack Prevention. Journal of Network and Systems Management, 30 (4). https://doi.org/10.1007/s10922-022-09676-2
- Henningsen, S., Teunis, D., Florian, M., Scheuermann, B. (2019). Eclipsing Ethereum Peers with False Friends. arXiv. Available at: https://doi.org/10.48550/ARXIV.1908.10141
- Deshpande, V., Badis, H., George, L. (2018). BTCmap: Mapping Bitcoin Peer-to-Peer Network Topology. 2018 IFIP/IEEE International Conference on Performance Evaluation and Modeling in Wired and Wireless Networks (PEMWN). https://doi.org/10.23919/pemwn.2018.8548904
- Xu, D., Gao, J., Zhu, L., Gao, F., Zhao, J. (2023). Statistical and clustering analysis of attributes of Bitcoin backbone nodes. PLOS ONE, 18 (11), e0292841. https://doi.org/10.1371/journal.pone.0292841
- Li, K., Tang, Y., Chen, J., Wang, Y., Liu, X. (2021). TopoShot: Uncovering Ethereum’s Network Topology Leveraging Replacement Transactions. arXiv. Available at: https://doi.org/10.48550/ARXIV.2109.14794
- Miller, A. K., Litton, J., Pachulski, A., Gupta, N., Levin, D., Spring, N., Bhattacharjee, B. (2015). Discovering Bitcoin’s Public Topology and Influential Nodes. Available at: https://www.cs.umd.edu/projects/coinscope/coinscope.pdf
- Rohrer, E., Tschorsch, F. (2019). Kadcast. Proceedings of the 1st ACM Conference on Advances in Financial Technologies. https://doi.org/10.1145/3318041.3355469
- Neudecker, T. (2019). Characterization of the Bitcoin Peer-to-Peer Network (2015-2018). Karlsruhe. Available at: https://doi.org/10.5445/IR/1000091933
- Eyong, M. (2019). Analyzing the Peer-to-Peer Network of Ethereum. Available at: https://www.researchgate.net/publication/354149867_Analyzing_the_Peer-to-Peer_Network_of_Ethereum
- Wang, T., Zhao, C., Yang, Q., Zhang, S., Liew, S. C. (2021). Ethna: Analyzing the Underlying Peer-to-Peer Network of Ethereum Blockchain. IEEE Transactions on Network Science and Engineering, 8 (3), 2131–2146. https://doi.org/10.1109/tnse.2021.3078181
- Wolchok, S., Halderman, J. (2010). Crawling BitTorrent DHTs for fun and profit. 4th USENIX Workshop on Offensive Technologies (WOOT ’10), Washington, D.C. Available at: https://jhalderm.com/pub/papers/dht-woot10.pdf
- rskj: RSKj is a Java implementation of the RSK protocol. Available at: https://github.com/rsksmart/rskj
- Node Discovery Protocol. Available at: https://github.com/ethereum/devp2p/blob/master/discv4.md
- Sedgewick, R., Wayne, K. (2011). Algorithms. Addison-Wesley Professional.
- SSD VPS Servers, Cloud Servers and Cloud Hosting. Available at: https://www.vultr.com/
- Vultr API. Available at: https://www.vultr.com/api/
- Hardware requirements. Available at: https://dev.rootstock.io/rsk/node/install/requirements/
- Maymounkov, P., Mazières, D. (2002). Kademlia: A Peer-to-Peer Information System Based on the XOR Metric. Lecture Notes in Computer Science, 53–65. https://doi.org/10.1007/3-540-45748-8_5
- PeerExplorer.java. Available at: https://github.com/rsksmart/rskj/blob/master/rskj-core/src/main/java/co/rsk/net/discovery/PeerExplorer.java
- NodeDistanceTable.java. Available at: https://github.com/rsksmart/rskj/blob/master/rskj-core/src/main/java/co/rsk/net/discovery/table/NodeDistanceTable.java
- KademliaOptions.java. Available at: https://github.com/rsksmart/rskj/blob/master/rskj-core/src/main/java/co/rsk/net/discovery/table/KademliaOptions.java
- ECKey.java. Available at: https://github.com/rsksmart/rskj/blob/6dde0cdeeb2138e61dc845810eaa8ce55a8d2b7f/rskj-core/src/main/java/org/ethereum/crypto/ECKey.java#L287
- DistanceCalculator.java. Available at: https://github.com/rsksmart/rskj/blob/master/rskj-core/src/main/java/co/rsk/net/discovery/table/DistanceCalculator.java
- PeerDiscoveryMessageFactory.java. Available at: https://github.com/rsksmart/rskj/blob/master/rskj-core/src/main/java/co/rsk/net/discovery/message/PeerDiscoveryMessageFactory.java
- PeerExplorer.java. L221. Available at: https://github.com/rsksmart/rskj/blob/e06686fe83554c6381db207857e13b6e76e79ace/rskj-core/src/main/java/co/rsk/net/discovery/PeerExplorer.java#L221
- PeerExplorer.java. L319. Available at: https://github.com/rsksmart/rskj/blob/e06686fe83554c6381db207857e13b6e76e79ace/rskj-core/src/main/java/co/rsk/net/discovery/PeerExplorer.java#L319
- main.conf. Available at: https://github.com/rsksmart/rskj/blob/master/rskj-core/src/main/resources/config/main.conf#L32
- Geolocation DB. Available at: https://geolocation-db.com/json/
- geojson.io. Available at: https://geojson.io/
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2024 Yaroslaw Dorogyy, Vadym Kolisnichenko

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





