Розробка гібридної системи виявлення вторгнень на основі методу Suricata з pfSense для значного зниження DDOS-атак на IPv6-мережі
DOI:
https://doi.org/10.15587/1729-4061.2023.285275Ключові слова:
завантаження ЦП, DDoS-атаки, джиттер, pfSense, Suricata, DDoS, IDS, IPv6Анотація
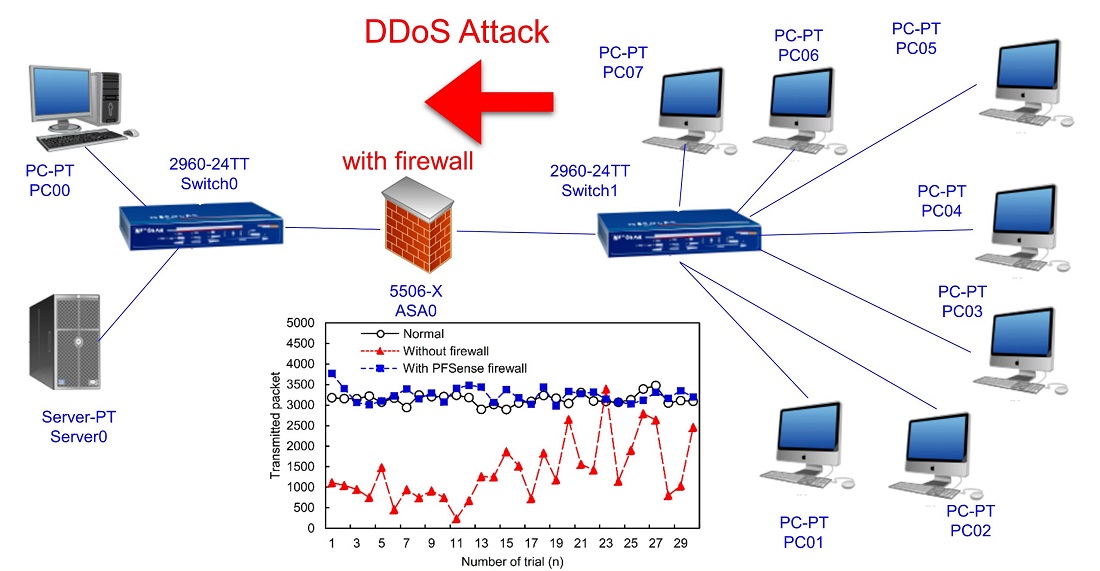
Розподілені атаки типу "відмова в обслуговуванні" (DDoS) є проблемою у комп'ютерних мережах. DDoS-атаки становлять серйозну загрозу для інтернет-мереж, оскільки вони викликають перевантаження і порушують оптимальне функціонування серверів. Виявлення джерела цих атак має важливе значення для ефективного захисту. Тому в даному дослідженні ми пропонуємо гібридну стратегію, що поєднує в собі систему виявлення вторгнень (IDS) Suricata з брандмауером pfSense для боротьби з DDoS-атаками. Система IDS Suricata здатна визначити місце призначення атаки, що дозволяє брандмауеру pfSense блокувати атаку, відкидаючи пакети, надіслані зловмисником. В результаті, використовуючи даний комбінований підхід, ми спостерігали значне поліпшення якості обслуговування (QoS). Результати нашого дослідження показують збільшення пропускної здатності на 1,08 %, з 1881,97 байт до 902,44 байт, що свідчить про підвищення ефективності передачі даних. Також ми спостерігали збільшення середньої загальної кількості відправлених пакетів на 57,32 %, з 1382 до 3238 пакетів, що вказує на підвищення продуктивності мережі. Крім того, запропонована стратегія дозволила значно знизити значення затримки та джиттера. Значення затримки зменшилося на 88,78 %, з 90,76 мс до 10,18 мс, а значення джиттера – на 88,99 %, з 181,85 мс до 20,03 мс. Дані поліпшення свідчать про помітне скорочення затримок і варіацій часу передачі пакетів, що призводить до більш плавної роботи мережі. Ще одним важливим аспектом, який ми оцінювали, було завантаження ЦП. Запропонована стратегія призвела до значного зниження завантаження ЦП на 81,23 %, з 78,3 % до 14,7 %. Комбінація pfSense і Suricata виявилася успішним підходом, що забезпечує надійний захист від DDoS-атак, у тому числі з використанням IPv6. Дане дослідження може бути реалізовано в якості рішення у кампусній спеціальній мережі з обмеженою кількістю комп'ютерів
Посилання
- Choi, K.-S., Lee, C. S., Louderback, E. R. (2020). Historical Evolutions of Cybercrime: From Computer Crime to Cybercrime. The Palgrave Handbook of International Cybercrime and Cyberdeviance, 27–43. doi: https://doi.org/10.1007/978-3-319-78440-3_2
- Al-Khater, W. A., Al-Maadeed, S., Ahmed, A. A., Sadiq, A. S., Khan, M. K. (2020). Comprehensive Review of Cybercrime Detection Techniques. IEEE Access, 8, 137293–137311. doi: https://doi.org/10.1109/access.2020.3011259
- Cascavilla, G., Tamburri, D. A., Van Den Heuvel, W.-J. (2021). Cybercrime threat intelligence: A systematic multi-vocal literature review. Computers & Security, 105, 102258. doi: https://doi.org/10.1016/j.cose.2021.102258
- Staroletov, S. (2022). Software Architecture for an Intelligent Firewall Based on Linux Netfilter. 2022 25th Conference on Innovation in Clouds, Internet and Networks (ICIN). doi: https://doi.org/10.1109/icin53892.2022.9758121
- Cinar, A. C., Kara, T. B. (2023). The current state and future of mobile security in the light of the recent mobile security threat reports. Multimedia Tools and Applications, 82 (13), 20269–20281. doi: https://doi.org/10.1007/s11042-023-14400-6
- Oloyede, O. A., Yekini, A. N., Akinwole, K. A., Ojo, O. (2021). Firewall Approach To Computer Network Security: Functional Viewpoint. International Journal of Advanced Networking and Applications, 13 (03), 4993–5000. doi: https://doi.org/10.35444/ijana.2021.13308
- Heino, J., Hakkala, A., Virtanen, S. (2022). Study of methods for endpoint aware inspection in a next generation firewall. Cybersecurity, 5 (1). doi: https://doi.org/10.1186/s42400-022-00127-8
- Ho, H. T. N., Luong, H. T. (2022). Research trends in cybercrime victimization during 2010–2020: a bibliometric analysis. SN Social Sciences, 2 (1). doi: https://doi.org/10.1007/s43545-021-00305-4
- Moneva, A., Leukfeldt, E. R., Klijnsoon, W. (2022). Alerting consciences to reduce cybercrime: a quasi-experimental design using warning banners. Journal of Experimental Criminology. doi: https://doi.org/10.1007/s11292-022-09504-2
- La Rosa, G. (2021). The 5G Technology Nexus: Assessing Threats and Risks of Implementation. Univerzita Karlova.
- Afolaranmi, A. O. (2022). Towards Understanding the Nexus between Pastoral Care, Social Media, and Sustainable Development in the Post-COVID-19 Era. doi: https://doi.org/10.21203/rs.3.rs-1630706/v1
- Gundur, R. V., Levi, M., Topalli, V., Ouellet, M., Stolyarova, M., Chang, L. Y.-C., Mejía, D. D. (2021). Evaluating Criminal Transactional Methods in Cyberspace as Understood in an International Context. CrimRxiv. doi: https://doi.org/10.21428/cb6ab371.5f335e6f
- Chowdhury, N., Gkioulos, V. (2021). Cyber security training for critical infrastructure protection: A literature review. Computer Science Review, 40, 100361. doi: https://doi.org/10.1016/j.cosrev.2021.100361
- Gupta, B. B., Perez, G. M., Agrawal, D. P., Gupta, D. (Eds.) (2020). Handbook of Computer Networks and Cyber Security. Springer Cham, 959. doi: https://doi.org/10.1007/978-3-030-22277-2
- Rawat, S., Srinivasan, A., Ravi, V., Ghosh, U. (2020). Intrusion detection systems using classical machine learning techniques vs integrated unsupervised feature learning and deep neural network. Internet Technology Letters, 5 (1). doi: https://doi.org/10.1002/itl2.232
- Reshmi, T. R. (2021). Information security breaches due to ransomware attacks - a systematic literature review. International Journal of Information Management Data Insights, 1 (2), 100013. doi: https://doi.org/10.1016/j.jjimei.2021.100013
- Balakrishnan, N., Rajendran, A., Pelusi, D., Ponnusamy, V. (2021). Deep Belief Network enhanced intrusion detection system to prevent security breach in the Internet of Things. Internet of Things, 14, 100112. doi: https://doi.org/10.1016/j.iot.2019.100112
- Naeem, M. A. A., Abubakar, A., Rahman, M. M. H. (2020). Dealing With Well-Formed and Malformed Packets, Associated With Point of Failure That Cause Network Security Breach. IEEE Access, 8, 197554–197566. doi: https://doi.org/10.1109/access.2020.3034383
- Ouiazzane, S., Addou, M., Barramou, F. (2022). A Suricata and Machine Learning Based Hybrid Network Intrusion Detection System. Lecture Notes in Networks and Systems, 474–485. doi: https://doi.org/10.1007/978-3-030-91738-8_43
- Gupta, A., Sharma, L. S. (2019). Performance Evaluation of Snort and Suricata Intrusion Detection Systems on Ubuntu Server. Proceedings of ICRIC 2019, 811–821. doi: https://doi.org/10.1007/978-3-030-29407-6_58
- Praptodiyono, S., Firmansyah, T., Murugesan, R. K., Alaydrus, M., Aprilia, R., Leau, Y.-B. (2021). Improving the security of mobile IPV6 signalling using KECCAK / SHA-3. Journal of Engineering Science and Technology, 16 (3), 2312–2325. Available at: https://jestec.taylors.edu.my/Vol%2016%20issue%203%20June%202021/16_3_33.pdf
- Scarfone, K. A., Mell, P. M. (2007). Guide to Intrusion Detection and Prevention Systems (IDPS). NIST. doi: https://doi.org/10.6028/nist.sp.800-94
- Shams, M., Sookhak, M., Gani, A., Buyya, R., Talebian, H. (2016). A comprehensive survey of network virtualization. Computer Networks, 108, 147–176.
- Ramachandran, A., Feamster, N. (2006). Understanding the network-level behavior of spammers. ACM SIGCOMM Computer Communication Review, 36 (4), 291–302. doi: https://doi.org/10.1145/1151659.1159947
- Mirkovic, J., Reiher, P. (2004). A taxonomy of DDoS attack and DDoS defense mechanisms. ACM SIGCOMM Computer Communication Review, 34 (2), 39–53. doi: https://doi.org/10.1145/997150.997156
- Karasaridis, A., Manousakis, K. (2017). Detection and mitigation of DDoS attacks using SDN: A comprehensive survey. IEEE Communications Surveys & Tutorials, 20 (3), 2233–2271.
- The Treacherous 12: Top Threats to Cloud Computing (2017). Cloud Security Alliance.
- Kolias, C., Kambourakis, G., Stavrou, A., Gritzalis, D. (2016). Distributed Denial of Service Attacks in Software-Defined Networking with Cloud Computing. IEEE Transactions on Dependable and Secure Computing, 13 (3), 373–378.
- Ramli, R., Maarof, M. A., Zainal, A. (2017). A survey of machine learning in DDoS attack detection. Journal of Network and Computer Applications, 88, 60–76.
- Nunes, B. A. A., Mendonca, M., Nguyen, X.-N., Obraczka, K., Turletti, T. (2014). A Survey of Software-Defined Networking: Past, Present, and Future of Programmable Networks. IEEE Communications Surveys & Tutorials, 16 (3), 1617–1634. doi: https://doi.org/10.1109/surv.2014.012214.00180
- National Cyber Incident Response Plan (2010). U.S. Department of Homeland Security.
- Steinberger, J., Sperotto, A., Baier, H., Pras, A. (2020). Distributed DDoS Defense:A collaborative Approach at Internet Scale. NOMS 2020 - 2020 IEEE/IFIP Network Operations and Management Symposium. doi: https://doi.org/10.1109/noms47738.2020.9110300
##submission.downloads##
Опубліковано
Як цитувати
Номер
Розділ
Ліцензія
Авторське право (c) 2023 Supriyanto Praptodiyono, Teguh Firmansyah, Muhamad Haerul Anwar, Cakra Adipura Wicaksana, Anggoro Suryo Pramudyo, Ali Al-Allawee

Ця робота ліцензується відповідно до Creative Commons Attribution 4.0 International License.
Закріплення та умови передачі авторських прав (ідентифікація авторства) здійснюється у Ліцензійному договорі. Зокрема, автори залишають за собою право на авторство свого рукопису та передають журналу право першої публікації цієї роботи на умовах ліцензії Creative Commons CC BY. При цьому вони мають право укладати самостійно додаткові угоди, що стосуються неексклюзивного поширення роботи у тому вигляді, в якому вона була опублікована цим журналом, але за умови збереження посилання на першу публікацію статті в цьому журналі.
Ліцензійний договір – це документ, в якому автор гарантує, що володіє усіма авторськими правами на твір (рукопис, статтю, тощо).
Автори, підписуючи Ліцензійний договір з ПП «ТЕХНОЛОГІЧНИЙ ЦЕНТР», мають усі права на подальше використання свого твору за умови посилання на наше видання, в якому твір опублікований. Відповідно до умов Ліцензійного договору, Видавець ПП «ТЕХНОЛОГІЧНИЙ ЦЕНТР» не забирає ваші авторські права та отримує від авторів дозвіл на використання та розповсюдження публікації через світові наукові ресурси (власні електронні ресурси, наукометричні бази даних, репозитарії, бібліотеки тощо).
За відсутності підписаного Ліцензійного договору або за відсутністю вказаних в цьому договорі ідентифікаторів, що дають змогу ідентифікувати особу автора, редакція не має права працювати з рукописом.
Важливо пам’ятати, що існує і інший тип угоди між авторами та видавцями – коли авторські права передаються від авторів до видавця. В такому разі автори втрачають права власності на свій твір та не можуть його використовувати в будь-який спосіб.