Improving the technology for processing the aggregated data flow of a secure corporate multiservice communication network
DOI:
https://doi.org/10.15587/1729-4061.2023.285414Keywords:
secure corporate multiservice communication network, aggregate flow, channel resource, VPN gatewayAbstract
This paper considers the process of dynamic reservation of the channel resource of a secure corporate multi-service communication network.
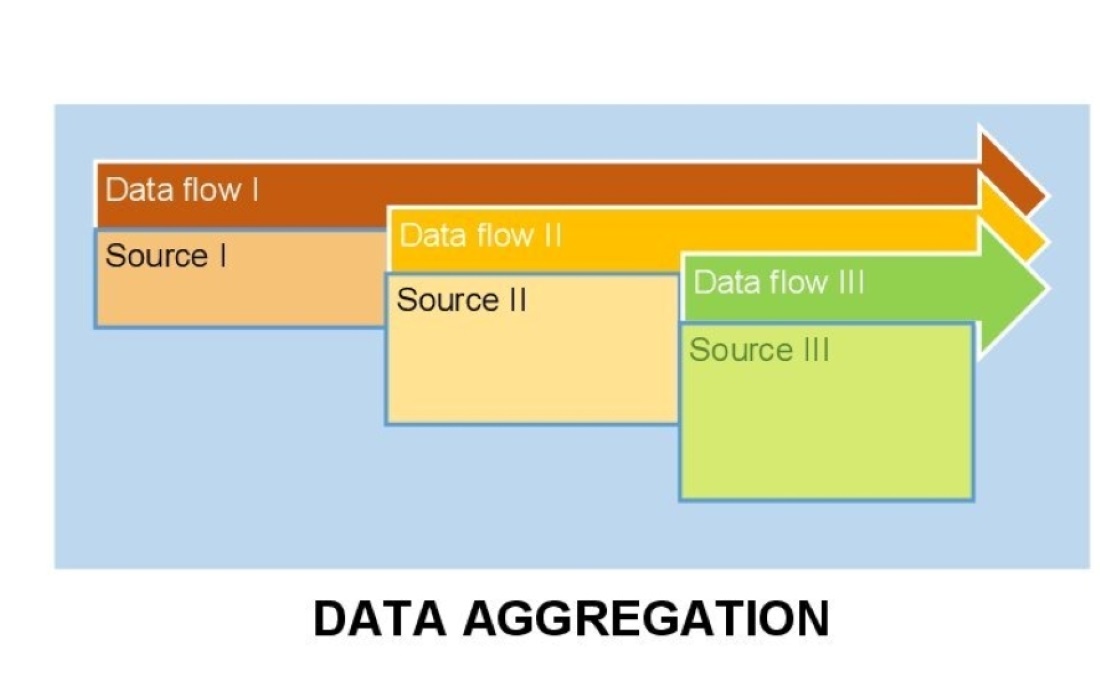
It has been established that the processes of building and functioning of the schemes of a secure corporate multi-service communication network and improving the quality of the implementation of its main work processes involve the evaluation and dynamic reservation of channel resources for incoming aggregated data flows of the network.
The model of dynamic reservation of the channel resource of the aggregated data stream of the secure corporate multi-service communication network was built and proposed. The proposed model makes it possible to set the quantitative values of the reserved channel resource for different service methods depending on the number of component flows in the total aggregated data flow of the VPN tunnel.
It was established that an increase in the density of the aggregated data stream requires an increase in the reserved channel resource. At the same time, its value is influenced by the way of servicing the aggregated data flow in the VPN tunnel of the secure corporate multi-service communication network. Application of the isolated service method gives a gain in the allocated resource for the channel reserve from 10 to 20 percent compared to the group service method for IR and video telephony. This is due to the more flexible management process of the border router's incoming data storage buffer under the isolated service mode.
The model of dynamic reservation of the channel resource of the secure corporate multi-service communication network reported in this paper could be used in the improvement of existing and development of new structures of the secure corporate multi-service communication network. The consequence of such an improvement is a reduction in the delay time for the processing of incoming data packets in the specified network
References
- Popivskyi, V. V., Lemeshko, O. V., Kovalchuk, V. K. Plotnikov, M. D., Kartushyn, Yu. P. et al. (2012). Telekomunikatsiini systemy ta merezhi. Struktura y osnovni funktsiyi. Vol. 1.
- Zakhyst informatsiyi na obiektakh informatsiynoi diyalnosti. Stvorennia kompleksu tekhnichnoho zakhystu informatsiyi. Osnovni polozhennia. ND TZI 1.1-005-07. Available at: https://tzi.com.ua/nd-tz-1.1-005-07.html
- Halkin, V. V., Parkhomenko, I. I. (2016). Vykorystannia VPN-tekhnolohiy dlia zakhystu informatsiyi v kanalakh korporatyvnykh merezh. Problema kiberbezpeky informatsiyno-telekomunikatsiynykh system: materialy nauk.- tekhn. konf. Kyiv: KNU, 66–76.
- Buriachok, V. L., Anosov, A. O., Semko, V. V., Sokolov, V. Yu., Skladannyi, P. M. (2019). Tekhnolohiyi zabezpechennia bezpeky merezhevoi infrastruktury. Kyiv: «KUBH», 218. Available at: https://elibrary.kubg.edu.ua/id/eprint/27191/1/VL_Buriachok_TZBMI.pdf
- Popovskyi, V. V., Oliinyk, V. F. (2011). Matematychni osnovy upravlinnia i adaptatsiyi v telekomunikatsiynykh systemakh. Kharkiv: TOV “Kompaniya SMIT”, 362.
- IPSec – protokol zakhystu merezhevoho trafiku na IP-rivni.
- Talib, H. A., Alothman, R. B., Mohammed, M. S. (2023). Malicious attacks modelling: a prevention approach for ad hoc network security. Indonesian Journal of Electrical Engineering and Computer Science, 30 (3), 1856. doi: https://doi.org/10.11591/ijeecs.v30.i3.pp1856-1865
- Almomani, A. (2022). Classification of Virtual Private networks encrypted traffic using ensemble learning algorithms. Egyptian Informatics Journal, 23 (4), 57–68. doi: https://doi.org/10.1016/j.eij.2022.06.006
- Balachandran, A., Amritha, P. P. (2022). VPN Network Traffic Classification Using Entropy Estimation and Time-Related Features. Smart Innovation, Systems and Technologies, 509–520. doi: https://doi.org/10.1007/978-981-16-3945-6_50
- Ma, X., Zhu, W., Wei, J., Jin, Y., Gu, D., Wang, R. (2023). EETC: An extended encrypted traffic classification algorithm based on variant resnet network. Computers & Security, 128, 103175. doi: https://doi.org/10.1016/j.cose.2023.103175
- Naas, M., Fesl, J. (2023). A novel dataset for encrypted virtual private network traffic analysis. Data in Brief, 47, 108945. doi: https://doi.org/10.1016/j.dib.2023.108945
- Lemeshko, O., Lebedenko, T., Nevzorova, O., Snihurov, A., Mersni, A., Al-Dulaimi, A. (2019). Development of the Balanced Queue Management Scheme with Optimal Aggregation of Flows and Bandwidth Allocation. 2019 IEEE 15th International Conference on the Experience of Designing and Application of CAD Systems (CADSM). doi: https://doi.org/10.1109/cadsm.2019.8779246
- Patil, H. K., Chen, T. M. (2017). Wireless Sensor Network Security. Computer and Information Security Handbook, 317–337. doi: https://doi.org/10.1016/b978-0-12-803843-7.00018-1
- Afuwape, A. A., Xu, Y., Anajemba, J. H., Srivastava, G. (2021). Performance evaluation of secured network traffic classification using a machine learning approach. Computer Standards & Interfaces, 78, 103545. doi: https://doi.org/10.1016/j.csi.2021.103545
- Geyer, F., Scheffler, A., Bondorf, S. (2023). Network Calculus With Flow Prolongation – A Feedforward FIFO Analysis Enabled by ML. IEEE Transactions on Computers, 72 (1), 97–110. doi: https://doi.org/10.1109/tc.2022.3204225
- Kovalenko, A., Kuchuk, H., Tkachov, V. (2021). Method of ensuring the survivability of the computer network based on vpn-tunneling. Control, Navigation and Communication Systems. Academic Journal, 1 (63), 90–95. doi: https://doi.org/10.26906/sunz.2021.1.090
- Kuchuk, N., Gavrylenko, S., Sobchuk, V., Lukova-Chuiko, N. (2019). Redistribution of information flows in a hyperconvergent system. Advanced Information Systems, 3 (2), 116–121. doi: https://doi.org/10.20998/2522-9052.2019.2.20
- Svyrydov, A., Kovalenko, A., Kuchuk, H. (2018). The pass-through capacity redevelopment method of net critical section based on improvement ON/OFF models of traffic. Advanced Information Systems, 2 (2), 139–144. doi: https://doi.org/10.20998/2522-9052.2018.2.24
- ITU-T Technical Report. XSTR-SEC-MANUAL Security in telecommunications and information technology (7th edition) (2022). International Telecommunication Union. Available at: https://www.itu.int/dms_pub/itu-t/opb/tut/T-TUT-ICTSS-2020-4-PDF-E.pdf
- Y.1541: Network performance objectives for IP-based services (2011). Available at: https://www.itu.int/rec/T-REC-Y.1541-201112-I/en
- Hnatushenko, V. V. (2014) Modeliuvannia ahrehovanoho trafiku peredachi danykh na osnovi modeli ON/OFF. Systemni tekhnolohiyi, 5, 65–72. Available at: http://nbuv.gov.ua/UJRN/st_2014_5_10
- Lebedenko, T., Goloveshko, M., Holodkova, A. (2019). Investigation of the method of active queue management on the interfaces of telecommunication networks routers. Control, Navigation and Communication Systems. Academic Journal, 4 (56), 57–62. doi: https://doi.org/10.26906/sunz.2019.4.057
- Lebedenko, T., Goloveshko, M., Severilov, A. (2019). The results of the experimental study of the Active Queue Management method at the interfaces of telecommunication networks. Problems of Telecommunications, 2 (25), 37–55. doi: https://doi.org/10.30837/pt.2019.2.03
- Gnatyuk, S., Kinzeryavyy, V., Kyrychenko, K., Yubuzova, K., Aleksander, M., Odarchenko, R. (2019). Secure Hash Function Constructing for Future Communication Systems and Networks. Advances in Intelligent Systems and Computing, 561–569. doi: https://doi.org/10.1007/978-3-030-12082-5_51
- Brumnik, R., Kovtun, V., Okhrimenko, A., Kavun, S. (2014). Techniques for Performance Improvement of Integer Multiplication in Cryptographic Applications. Mathematical Problems in Engineering, 2014, 1–7. doi: https://doi.org/10.1155/2014/863617
- Odarchenko, R., Gnatyuk, V., Gnatyuk, S., Abakumova, A. (2018). Security Key Indicators Assessment for Modern Cellular Networks. 2018 IEEE First International Conference on System Analysis & Intelligent Computing (SAIC). doi: https://doi.org/10.1109/saic.2018.8516889
- Berkman, L., Turovsky, O., Kyrpach, L., Varfolomeeva, O., Dmytrenko, V., Pokotylo, O. (2021). Analyzing the code structures of multidimensional signals for a continuous information transmission channel. Eastern-European Journal of Enterprise Technologies, 5 (9 (113)), 70–81. doi: https://doi.org/10.15587/1729-4061.2021.242357
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2023 Liubov Berkman, Andrii Zakharzhevskyi, Kostiantyn Lavrinets

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





