Development of a method for solving the problem of it product configuration analysis
DOI:
https://doi.org/10.15587/1729-4061.2022.269133Keywords:
IT product, architecture description, configuration item, divisive algorithm, Chebyshev distance, Hamming distanceAbstract
The object of this study is the process of managing the configuration of an IT project.
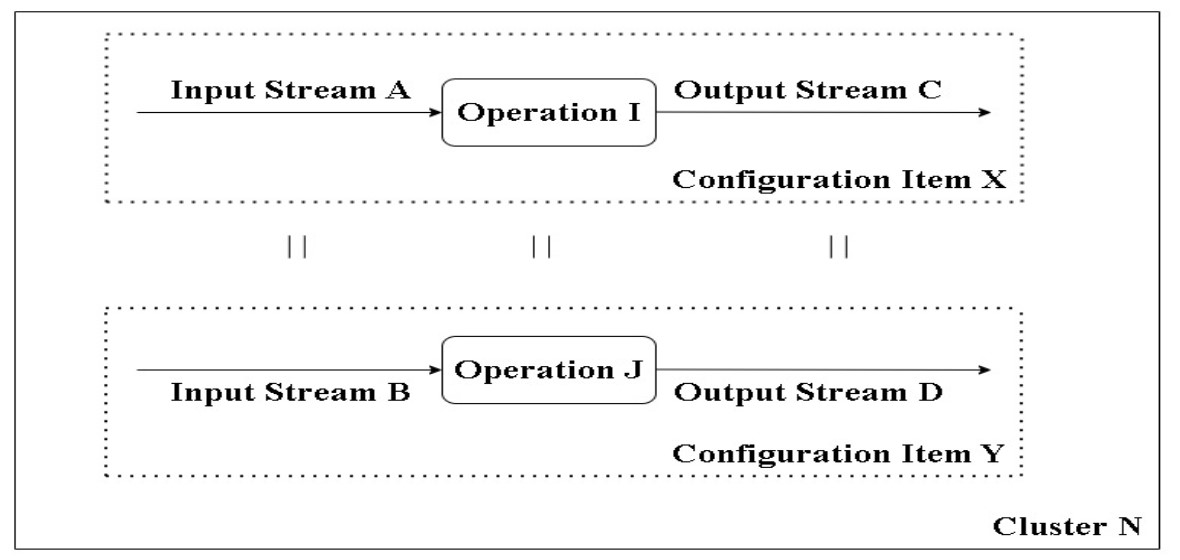
During the study, the problem of analyzing the configuration of an IT product was solved. Research in this area is mainly aimed at solving the problem of configuration analysis during the refactoring of a monolithic IT product into individual services or microservices. Questions about the methods of decomposing the description of the architecture of the developed IT product into separate functional configuration items (CI) remain almost unexplored.
As a result of the study, a method has been developed that makes it possible to build in the form of a dendrogram all possible options for decomposing the description of the IT product architecture into separate CIs. Unlike existing ones, the proposed method takes into account the degree of repetition of CI descriptions. The method is based on a Smith Maknaoton's divisive algorithm for solving the clustering problem. For its use, when solving the problem, the method for determining the distance between two functional CIs was modified.
The devised method passed an experimental test during the development of the functional task "Formation and maintenance of the individual plan of the scientific and pedagogical employee of the department". As CI, 10 functions of the task were considered. To define these functions, the descriptions of 12 entities in the problem database were used. As a result, a dendrogram was constructed with all possible options for decomposing the description of the task architecture into separate CIs.
Using the results of the study, it is possible to distinguish separate functional CIs and CI groups, the descriptions of which are strongly similar to each other. This allows one to improve the quality of IT product development by assigning such CI groups to one and the same executor of the IT project.
The reported results are used to form backlogs of the IT product and further distribute their elements among the executors of the IT project
References
- Bourque, P., Fairley, R. E. (Eds.) (2014). Guide to the Software Engineering Body of Knowledge. Version 3.0. IEEE Computer Society, 335.
- Cadavid, H., Andrikopoulos, V., Avgeriou, P., Broekema, P. C. (2022). System and software architecting harmonization practices in ultra-large-scale systems of systems: A confirmatory case study. Information and Software Technology, 150, 106984. doi: https://doi.org/10.1016/j.infsof.2022.106984
- Suljkanović, A., Milosavljević, B., Inđić, V., Dejanović, I. (2022). Developing Microservice-Based Applications Using the Silvera Domain-Specific Language. Applied Sciences, 12 (13), 6679. doi: https://doi.org/10.3390/app12136679
- Sellami, K., Saied, M. A., Ouni, A. (2022). A Hierarchical DBSCAN Method for Extracting Microservices from Monolithic Applications. The International Conference on Evaluation and Assessment in Software Engineering 2022, 201–210. doi: https://doi.org/10.1145/3530019.3530040
- Krause, A., Zirkelbach, C., Hasselbring, W., Lenga, S., Kroger, D. (2020). Microservice Decomposition via Static and Dynamic Analysis of the Monolith. 2020 IEEE International Conference on Software Architecture Companion (ICSA-C). doi: https://doi.org/10.1109/icsa-c50368.2020.00011
- Matias, T., Correia, F. F., Fritzsch, J., Bogner, J., Ferreira, H. S., Restivo, A. (2020). Determining Microservice Boundaries: A Case Study Using Static and Dynamic Software Analysis. 14th European Conference on Software Architecture, ECSA 2020, 315–332. doi: https://doi.org/10.1007/978-3-030-58923-3_21
- Fritzsch, J., Bogner, J., Zimmermann, A., Wagner, S. (2019). From monolith to microservices: A classification of refactoring approaches. 1st International Workshop on Software Engineering Aspects of Continuous Development and New Paradigms of Software Production and Deployment, DEVOPS 2018, 128–141. doi: https://doi.org/10.1007/978-3-030-06019-0_10
- Shahin, R. (2021). Towards Assurance-Driven Architectural Decomposition of Software Systems. 40th International Conference on Computer Safety, Reliability and Security, SAFECOMP 2021 held in conjunction with Workshops on DECSoS, MAPSOD, DepDevOps, USDAI and WAISE 2021, 187–196. doi: https://doi.org/10.48550/arXiv.2106.09237
- Reiff-Marganiec, S., Tilly, M. (Eds.) (2012). Handbook of Research on Service-Oriented Systems and Non-Functional Properties: Future Directions. Hershey: IGI Global, 521. doi: https://doi.org/10.4018/978-1-61350-432-1
- Faitelson, D., Heinrich, R., Tyszberowicz, S. (2017). Supporting Software Architecture Evolution by Functional Decomposition. Proceedings of the 5th International Conference on Model-Driven Engineering and Software Development, 435–442. doi: https://doi.org/10.5220/0006206204350442
- Wierzchoń, S., Kłopotek, M. (2018). Modern Algorithms of Cluster Analysis. Cham: Springer, 441. doi: https://doi.org/10.1007/978-3-319-69308-8
- Barsegian, A. A., Kupriianov, M. S., Kholod, I. I., Tess, M. D., Elizarov, S. I. (2009). Analiz dannykh i protcessov. Saint Petersburg: BKhV-Peterburg, 512.
- Yevlanov, M. V., Vasyltsova, N. V., Panforova, I. Yu. (2015). Modeli i metody syntezu opysu ratsionalnoi arkhitektury informatsiinoi systemy. Visnyk naukovoho universytetu «Lvivska politekhnika». Seriia «Informatsiini systemy ta merezhi», 829, 135–152. Available at: https://science.lpnu.ua/sites/default/files/journal-paper/2018/jun/12881/9ievlanovmvvasilcovanv.pdf
- Evlanov, M. V. (2016). Development of the model and method of selecting the description of rational architecture of information system. Eastern-European Journal of Enterprise Technologies, 1 (2 (79)), 4–12. doi: https://doi.org/10.15587/1729-4061.2016.60583
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2022 Maksym Ievlanov, Nataliya Vasiltcova, Olga Neumyvakina, Iryna Panforova

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





