Development of a cropping resilient watermarking scheme based on contourlet transform for secure IoT communication
DOI:
https://doi.org/10.15587/1729-4061.2023.273973Keywords:
contourlet transform, watermarking, Arnold transform, geometric attacks, cropping attack, SVDAbstract
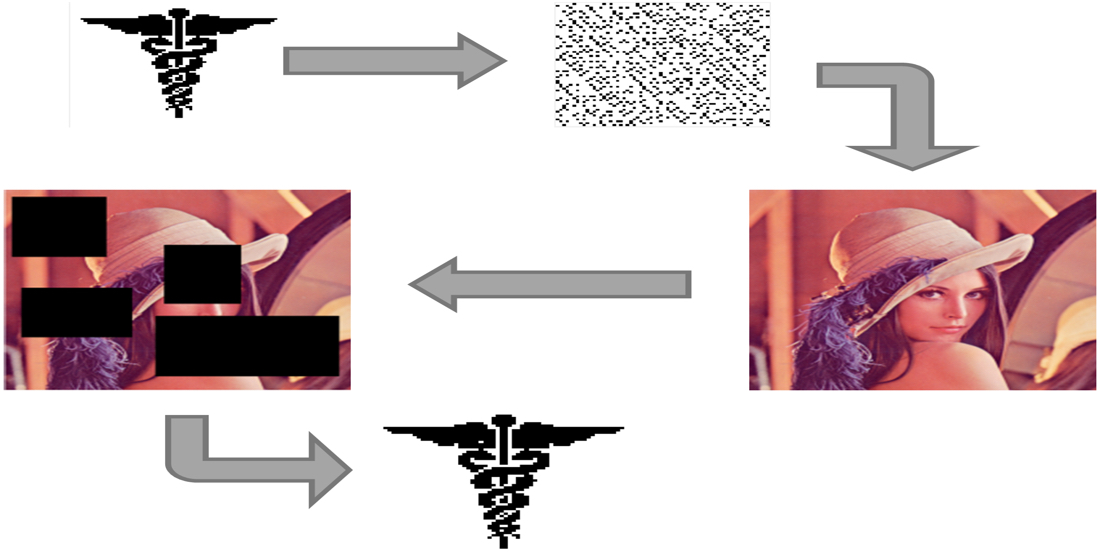
The objective of this work is to propose a robust watermarking method as watermarking techniques are widely used today for preventing image altering and duplication. With the growth of image-based IoT applications nowadays, the need for developing robust digital watermarking techniques is of high demand. In this work, a robust yet highly perceptible watermarking scheme is proposed. The proposed scheme is based on the Contourlet Transform (CT) and Singular Value Decomposition (SVD) as the embedding domain in which the high-frequency components are chosen for embedding. The frequency domain is selected in order to make the watermarking scheme resists image attacks as the watermark is spreaded across different frequency bands in the cover image and hence the possibility of altering all the embedded bands is not possible as it will results in destroying the cover image. On the other hand, the Arnold transformation was used to insure secure IOT communication where the Arnold transform is applied to the binary logo watermark before embedding for a more secure design. In this context, the host image has been decomposed into the first level of contourlet transform and the highest frequency sub-bands are selected for embedding after performing the SVD on those bands where the SVD matrix is chosen to be the embedding domain. Moreover, This work aims to resist the cropping attack on images where PSNR values were above 52 dB and NC values ranged from 0.8 to 0.9 under various types of cropping attacks. In addition, the proposed method demonstrates its ability to resist various geometric and noise attacks such as JPEG compression, histogram equalization, gaussian noising and image brightening. Comparisons with state-of-the-art work demonstrate the proposed scheme's efficienc
References
- The promise of telehealth for hospitals, health systems and their communities, TrendWatch (2015). American Hospital Association. Available at: https://www.aha.org/guidesreports/2015-01-20-promise-telehealth-hospitals-health-systems-and-their-communities
- Anand, A., Singh, A. K. (2020). An improved DWT-SVD domain watermarking for medical information security. Computer Communications, 152, 72–80. doi: https://doi.org/10.1016/j.comcom.2020.01.038
- Ananthaneni, V., Nelakuditi, U. R. (2017). Hybrid Digital Image Watermarking using Contourlet Transform (CT), DCT and SVD. International Journal of Image Processing(IJIP), 11 (3), 85–93. Available at: http://www.kresttechnology.com/krest-academic-projects/krest-major-projects/ECE/BTech%20DSP%20Major%202018/Base%20paper/8.pdf
- Aparna, P., Kishore, P. V. V. (2019). A Blind Medical Image Watermarking for Secure E-Healthcare Application Using Crypto-Watermarking System. Journal of Intelligent Systems, 29 (1), 1558–1575. doi: https://doi.org/10.1515/jisys-2018-0370
- Bajaj, A. (2014). Robust and reversible digital image watermarking technique based on RDWT-DCT-SVD. 2014 International Conference on Advances in Engineering & Technology Research (ICAETR - 2014). doi: https://doi.org/10.1109/icaetr.2014.7012955
- Surekha, B., Swamy, G. N. (2013). Sensitive digital image watermarking for copyright protection. International Journal of Network Security, 15 (2), 95–103. Available at: https://www.researchgate.net/profile/Surekha-Borra/publication/286714951_Sensitive_Digital_Image_Watermarking_for_Copyright_Prottection/links/5709516b08ae2eb9421e2ea6/Sensitive-Digital-Image-Watermarking-for-Copyright-Prottection.pdf
- Gavini, N. S., Borra, S. (2014). Lossless watermarking technique for copyright protection of high resolution images. 2014 IEEE REGION 10 SYMPOSIUM. doi: https://doi.org/10.1109/tenconspring.2014.6863000
- Surekha, B., Swamy, G., Reddy, K. R. L. (2012). A novel copyright protection scheme based on Visual Secret Sharing. 2012 Third International Conference on Computing, Communication and Networking Technologies (ICCCNT’12). doi: https://doi.org/10.1109/icccnt.2012.6395968
- Magdy, M., Ghali, N. I., Ghoniemy, S., Hosny, K. M. (2022). Multiple Zero-Watermarking of Medical Images for Internet of Medical Things. IEEE Access, 10, 38821–38831. doi: https://doi.org/10.1109/access.2022.3165813
- Wu, P., Chen, J. (2022). A New Information Hiding Scheme Using Discrete Wavelet Transform at Physical Layer. 2022 IEEE 2nd International Conference on Power, Electronics and Computer Applications (ICPECA). doi: https://doi.org/10.1109/icpeca53709.2022.9719283
- Anand, A., Singh, A. K. (2023). Dual Watermarking for Security of COVID-19 Patient Record. IEEE Transactions on Dependable and Secure Computing, 20 (1), 859–866. doi: https://doi.org/10.1109/tdsc.2022.3144657
- Ernawan, F., Ariatmanto, D., Musa, Z., Mustaffa, Z., Zain, J. M. (2020). An Improved Robust Watermarking Scheme using Flexible Scaling Factor. 2020 International Conference on Computational Intelligence (ICCI). doi: https://doi.org/10.1109/icci51257.2020.9247798
- Preet, C., Aggarwal, R. K. (2017). Multiple image watermarking using LWT, DCT and arnold transformation. 2017 International Conference on Trends in Electronics and Informatics (ICEI). doi: https://doi.org/10.1109/icoei.2017.8300908
- Gupta, N., Bhansali, A. (2021). Embedding Color Watermark by Adjusting DCT using RGB Gray Scale Watermarking. 2021 Emerging Trends in Industry 4.0 (ETI 4.0). doi: https://doi.org/10.1109/eti4.051663.2021.9619432
- Mohammed, A. A., Abdullah, M. A. M., Elbasi, E. (2021). A Hybrid Watermarking Scheme Based on Arnold Cat Map Against Lossy JPEG Compression. 2021 International Conference on Information Security and Cryptology (ISCTURKEY). doi: https://doi.org/10.1109/iscturkey53027.2021.9654333
- Novamizanti, L., Wahidah, I., Wardana, N. (2020). A Robust Medical Images Watermarking Using FDCuT-DCT-SVD. International Journal of Intelligent Engineering and Systems, 13 (6), 266–278. doi: https://doi.org/10.22266/ijies2020.1231.24
- Elbasi, E., Kaya, V. (2018). Robust Medical Image Watermarking Using Frequency Domain and Least Significant Bits Algorithms. 2018 International Conference on Computing Sciences and Engineering (ICCSE). doi: https://doi.org/10.1109/iccse1.2018.8374221
- Mohammed, A. A., Abdullah, M. A. M., Awad, S. R., Alghareb, F. S. (2022). A Novel FDCT-SVD Based Watermarking with Radon Transform for Telemedicine Applications. International Journal of Intelligent Engineering and Systems, 15 (1). doi: https://doi.org/10.22266/ijies2022.0228.07
- Kang, X., Zhao, F., Lin, G., Chen, Y. (2017). A novel hybrid of DCT and SVD in DWT domain for robust and invisible blind image watermarking with optimal embedding strength. Multimedia Tools and Applications, 77 (11), 13197–13224. doi: https://doi.org/10.1007/s11042-017-4941-1
- Mohammmed, A. A., Elbasi, E., Alsaydia, O. M. (2021). An Adaptive Robust Semi-blind Watermarking in Transform Domain Using Canny Edge Detection Technique. 2021 44th International Conference on Telecommunications and Signal Processing (TSP). doi: https://doi.org/10.1109/tsp52935.2021.9522657
- Kamili, A., Hurrah, N. N., Parah, S. A., Bhat, G. M., Muhammad, K. (2021). DWFCAT: Dual Watermarking Framework for Industrial Image Authentication and Tamper Localization. IEEE Transactions on Industrial Informatics, 17 (7), 5108–5117. doi: https://doi.org/10.1109/tii.2020.3028612
- Borra, S., Lakshmi, H., Dey, N., Ashour, A., Shi, F. (2017). Digital image watermarking tools: state-of-the-art. Frontiers in Artificial Intelligence and Applications, 296, 450–459.
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2023 Yahya Idham, Omar Alsaydia, Mohammed A. M. Abdullah, Ahmed Mohammed, Ersin Elbasi

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





