Evaluating image encryption algorithms for the hyperchaotic system and fibonacci q-matrix, secure internet of things, and advanced encryption standard
DOI:
https://doi.org/10.15587/1729-4061.2022.265862Keywords:
Fibonacci Q-matrix in hyperchaotic, secure internet of things, AESAbstract
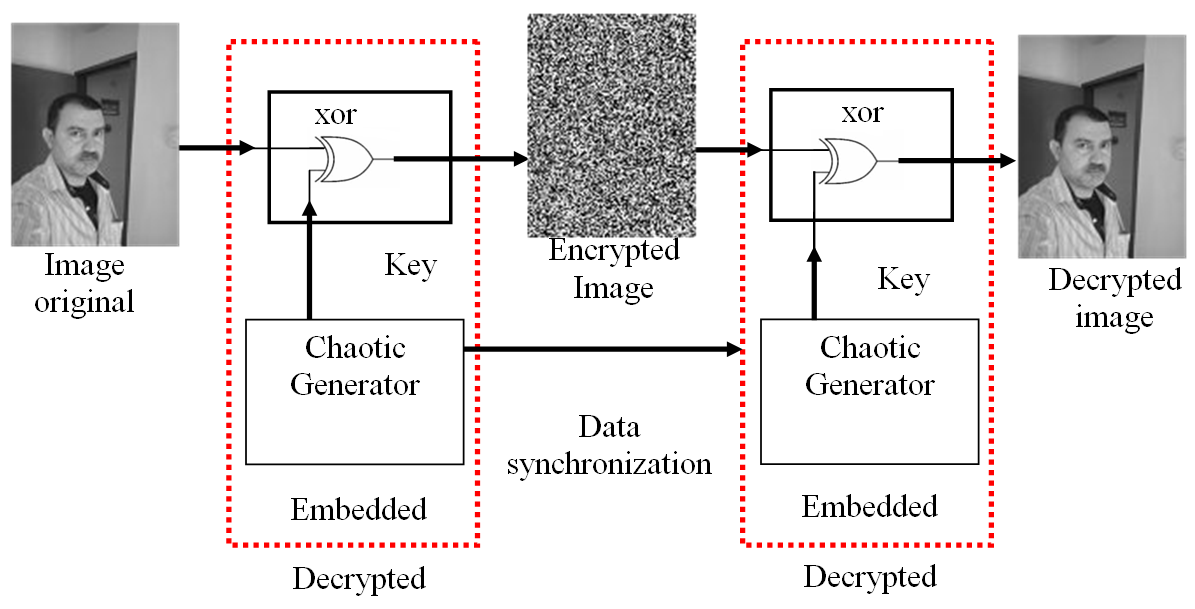
In the era of information technology, users had to send millions of images back and forth daily. It's crucial to secure these photos. It is important to secure image content using digital image encryption. Using secret keys, digital images are transformed into noisy images in image encryption techniques, and the same keys are needed to restore the images to their original form. The majority of image encryption methods rely on two processes: confusion and diffusion. However, previous studies didn’t compare recent techniques in the image encryption field.This research presents an evaluation of three types of image encryption algorithms includinga Fibonacci Q-matrix in hyperchaotic, Secure Internet of Things (SIT), and AES techniques. The Fibonacci Q-matrix in the hyperchaotic technique makes use of a six-dimension hyperchaotic system's randomly generated numbers and confuses the original image to dilute the permuted image. The objectives here areto analyze the image encryption process for the Fibonacci Q-matrix in hyperchaotic, Secure Internet of Things (SIT), and Advanced Encryption Standard (AES), and compare their encryption robustness. The discussed image encryption techniques were examined through histograms, entropy, Unified Average Changing Intensity (UACI), Number of Pixels Change Rate (NPCR), and correlation coefficients. Since the values of the Chi-squared test were less than (293) for the Hyperchaotic System & Fibonacci Q-matrix method, this indicates that this technique has a uniform distribution and is more efficient. The obtained results provide important confirmation that the image encryption using Fibonacci Q-matrix in hyperchaotic algorithm performed better than both the AES and SIT based on the image values of UACI and NPCR.
References
- Saddam, M. J., Ibrahim, A. A., Mohammed, A. H. (2020). A Lightweight Image Encryption And Blowfish Decryption For The Secure Internet Of Things. 2020 4th International Symposium on Multidisciplinary Studies and Innovative Technologies (ISMSIT). doi: https://doi.org/10.1109/ismsit50672.2020.9254366
- Mishra, Z., Acharya, B. (2020). High throughput and low area architectures of secure IoT algorithm for medical image encryption. Journal of Information Security and Applications, 53, 102533. doi: https://doi.org/10.1016/j.jisa.2020.102533
- Rabab, U. e, Ahmed, I., Aslam, M. I., Usman, M. (2018). FPGA Implementation of Secure Internet of Things (SIT) Algorithm for High Throughput Area Ratio. International Journal of Future Generation Communication and Networking, 11 (5), 63–72. doi: https://doi.org/10.14257/ijfgcn.2018.11.5.06
- Usman, M., Ahmed, I., Imran, M., Khan, S., Ali, U. (2017). SIT: A Lightweight Encryption Algorithm for Secure Internet of Things. International Journal of Advanced Computer Science and Applications, 8 (1). doi: https://doi.org/10.14569/ijacsa.2017.080151
- Hosny, K. M., Kamal, S. T., Darwish, M. M., Papakostas, G. A. (2021). New Image Encryption Algorithm Using Hyperchaotic System and Fibonacci Q-Matrix. Electronics, 10 (9), 1066. doi: https://doi.org/10.3390/electronics10091066
- Hosny, K. M., Kamal, S. T., Darwish, M. M. (2022). Novel encryption for color images using fractional-order hyperchaotic system. Journal of Ambient Intelligence and Humanized Computing, 13 (2), 973–988. doi: https://doi.org/10.1007/s12652-021-03675-y
- Padole, M. (2013). Distributed computing for structured storage, retrieval and processing of DNA sequencing data. International Journal ofInternet and Web Technology, 38, 1113–1118.
- Tanougast, C., Dandache, A., Salah, M., Sadoudi, S. (2012). Hardware Design of Embedded Systems for Security Applications. Embedded Systems – High Performance Systems, Applications and Projects. doi: https://doi.org/10.5772/38649
- Gamido, H. V., Sison, A. M., Medina, R. P. (2018). Implementation of Modified AES as Image Encryption Scheme. Indonesian Journal of Electrical Engineering and Informatics (IJEEI), 6 (3). doi: https://doi.org/10.11591/ijeei.v6i3.490
- Zhang, Y. (2018). Test and Verification of AES Used for Image Encryption. 3D Research, 9 (1). doi: https://doi.org/10.1007/s13319-017-0154-7
- Shariatzadeh, M., Rostami, M. J., Eftekhari, M. (2021). Proposing a novel Dynamic AES for image encryption using a chaotic map key management approach. Optik, 246, 167779. doi: https://doi.org/10.1016/j.ijleo.2021.167779
- Gaur, P. (2021). AES Image Encryption (Advanced Encryption Standard). International Journal for Research in Applied Science and Engineering Technology, 9 (12), 1357–1363. doi: https://doi.org/10.22214/ijraset.2021.39542
- Vijayakumar, P., Chittoju, C. K., Bharadwaja, A. V., Tayade, P. P., Tamilselvi, M., Rajashree, R., Gao, X. Z. (2019). FPGA implementation of AES for image encryption and decryption. International Journal of Innovative Technology and Exploring Engineering, 8 (7), 807–812.
- Gamido, H. V., Sison, A. M., Medina, R. P. (2018). Modified AES for Text and Image Encryption. Indonesian Journal of Electrical Engineering and Computer Science, 11 (3), 942. doi: https://doi.org/10.11591/ijeecs.v11.i3.pp942-948
- Mohammed, A. B., Al-Mafrji, A. A. M., Yassen, M. S., Sabry, A. H. (2022). Developing plastic recycling classifier by deep learning and directed acyclic graph residual network. Eastern-European Journal of Enterprise Technologies, 2 (10 (116)), 42–49. doi: https://doi.org/10.15587/1729-4061.2022.254285
- Kaur, M., Singh, S., Kaur, M. (2021). Computational Image Encryption Techniques: A Comprehensive Review. Mathematical Problems in Engineering, 2021, 1–17. doi: https://doi.org/10.1155/2021/5012496
- Zhang, X., Wang, L., Wang, Y., Niu, Y., Li, Y. (2020). An Image Encryption Algorithm Based on Hyperchaotic System and Variable-Step Josephus Problem. International Journal of Optics, 2020, 1–15. doi: https://doi.org/10.1155/2020/6102824
- Naim, M., Ali Pacha, A., Serief, C. (2021). A novel satellite image encryption algorithm based on hyperchaotic systems and Josephus problem. Advances in Space Research, 67 (7), 2077–2103. doi: https://doi.org/10.1016/j.asr.2021.01.018
- Wang, X., Su, Y., Luo, C., Nian, F., Teng, L. (2022). Color image encryption algorithm based on hyperchaotic system and improved quantum revolving gate. Multimedia Tools and Applications, 81 (10), 13845–13865. doi: https://doi.org/10.1007/s11042-022-12220-8
- Naim, M., Ali Pacha, A. (2021). New chaotic satellite image encryption by using some or all the rounds of the AES algorithm. Information Security Journal: A Global Perspective, 1–25. doi: https://doi.org/10.1080/19393555.2021.1982082
- Han, F., Liao, X., Yang, B., Zhang, Y. (2017). A hybrid scheme for self-adaptive double color-image encryption. Multimedia Tools and Applications, 77 (11), 14285–14304. doi: https://doi.org/10.1007/s11042-017-5029-7
- Zhang, T., Li, S., Ge, R., Yuan, M., Ma, Y. (2016). A Novel 1D Hybrid Chaotic Map-Based Image Compression and Encryption Using Compressed Sensing and Fibonacci-Lucas Transform. Mathematical Problems in Engineering, 2016, 1–15. doi: https://doi.org/10.1155/2016/7683687
- Pan, C., Ye, G., Huang, X., Zhou, J. (2019). Novel Meaningful Image Encryption Based on Block Compressive Sensing. Security and Communication Networks, 2019, 1–12. doi: https://doi.org/10.1155/2019/6572105
- Sun, S., Guo, Y., Wu, R. (2019). A Novel Image Encryption Scheme Based on 7D Hyperchaotic System and Row-column Simultaneous Swapping. IEEE Access, 7, 28539–28547. doi: https://doi.org/10.1109/access.2019.2901870
- Chandramouli, R., Bapatla, S., Subbalakshmi, K. P., Uma, R. N. (2006). Battery power-aware encryption. ACM Transactions on Information and System Security, 9 (2), 162–180. doi: https://doi.org/10.1145/1151414.1151417
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2022 Sabreen Ali Hussein, Aseel Hamoud Hamza, Suhad Al-Shoukry, Musaddak Maher Abdul Zahra, Ali Saleem Abu Nouwar, Sarah Ali Abdulkareem, Mohammed Hasan Ali, Mustafa Musa Jaber

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





