Development of a multi-loop security system of information interactions in socio-cyberphysical systems
DOI:
https://doi.org/10.15587/1729-4061.2023.289467Keywords:
socio-cyber-physical system, security model of information interactions, social engineering, targeted attacksAbstract
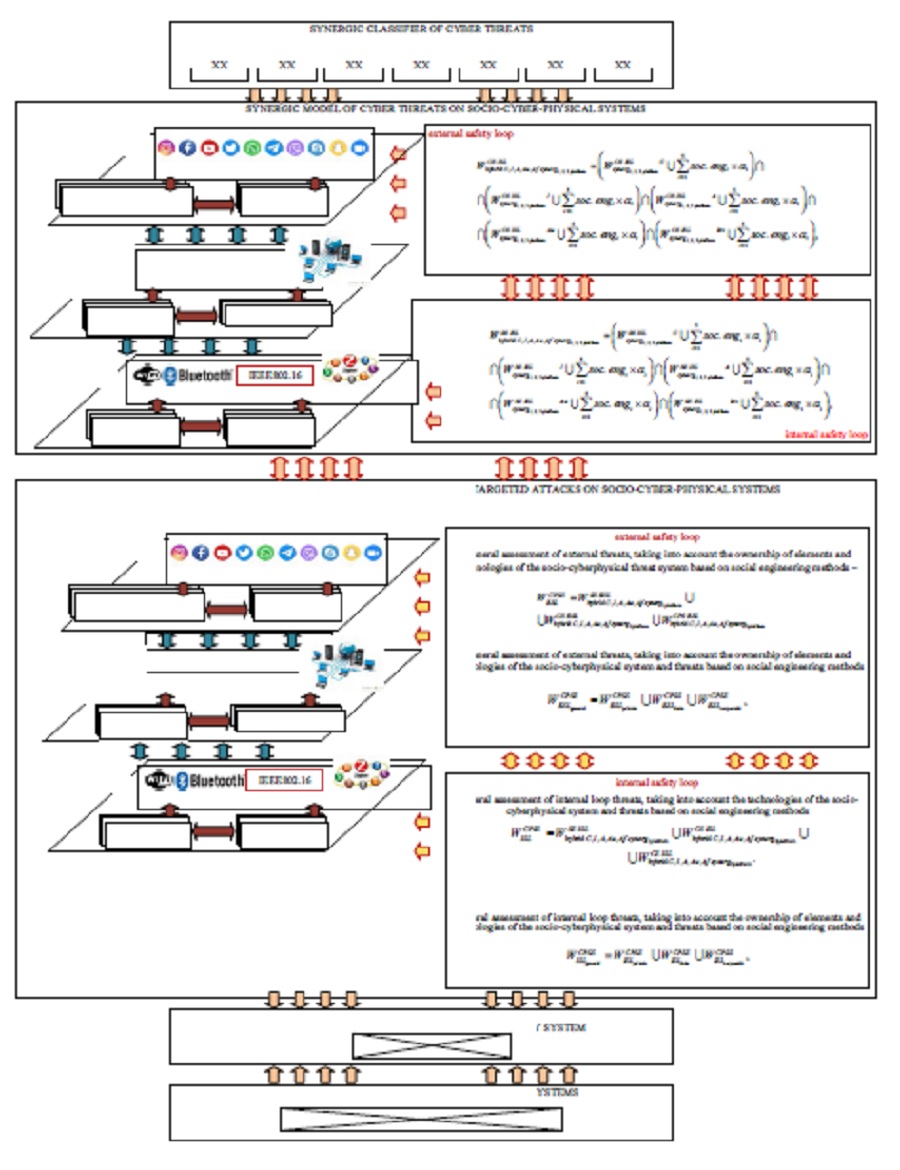
The object of the study is a multi-loop security system of information interactions in socio-cyberphysical systems. The dynamic nature of physical environments inherently challenges the ability of socio-cyber-physical systems to perform adequate control actions for physical assets in many contexts. However, adaptation and evolution actions must be evaluated before implementation in the control system to ensure fault tolerance while minimizing risks. Therefore, the design of socio-cyber-physical systems must ensure not only reliable autonomy, but also operational fault tolerance and safety. The proposed approach is based on the integration of targeted (mixed) threats based on the synthesis of technical cyber threats with social engineering methods. This approach allows forming a dynamic security model based on the analysis of the interaction of various agents in socio-cyberphysical systems, which makes it possible to increase the level of counteraction to targeted (mixed) cyber threats.
The results of modeling are based on the proposed classification of threats using social engineering methods, which allows cyberattackers to ensure the probability of implementing targeted threats up to 95–98 %. The proposed classification of threats based on social engineering methods will allow forming an additional parameter for the objectivity of target threats, taking into account their integration and synergy. At the same time, the presented model will make it possible to timely provide knowledge about the possibility of implementing a targeted attack and timely take preventive countermeasures. This approach will improve the set of protection measures, as well as promptly create an increase in the level of resistance of the company's personnel (organization, enterprise, etc.) to threats of social engineering
References
- Graf, S., Quinton, S., Girault, A., Gössler, G. (2018). Building Correct Cyber-Physical Systems: Why We Need a Multiview Contract Theory. Lecture Notes in Computer Science, 19–31. doi: https://doi.org/10.1007/978-3-030-00244-2_2
- Bereket Abera, Y., Naudet, Y., Panetto, H. (2020). A new Paradigm and Meta-Model for Cyber-Physical-Social Systems. IFAC-PapersOnLine, 53 (2), 10949–10954. doi: https://doi.org/10.1016/j.ifacol.2020.12.2841
- Yilma, B. A., Naudet, Y., Panetto, H. (2019). Introduction to Personalisation in Cyber-Physical-Social Systems. Lecture Notes in Computer Science, 25–35. doi: https://doi.org/10.1007/978-3-030-11683-5_3
- Yilma, B. A., Panetto, H., Naudet, Y. (2019). A Meta-Model of Cyber-Physical-Social System: The CPSS Paradigm to Support Human-Machine Collaboration in Industry 4.0. IFIP Advances in Information and Communication Technology, 11–20. doi: https://doi.org/10.1007/978-3-030-28464-0_2
- Naudet, Y., Yilma, B. A., Panetto, H. (2018). Personalisation in Cyber Physical and Social Systems: the Case of Recommendations in Cultural Heritage Spaces. 2018 13th International Workshop on Semantic and Social Media Adaptation and Personalization (SMAP). doi: https://doi.org/10.1109/smap.2018.8501890
- Zeng, J., Yang, L. T., Lin, M., Ning, H., Ma, J. (2020). A survey: Cyber-physical-social systems and their system-level design methodology. Future Generation Computer Systems, 105, 1028–1042. doi: https://doi.org/10.1016/j.future.2016.06.034
- Sheth, A., Anantharam, P., Henson, C. (2013). Physical-Cyber-Social Computing: An Early 21st Century Approach. IEEE Intelligent Systems, 28 (1), 78–82. doi: https://doi.org/10.1109/mis.2013.20
- Wang, F.-Y. (2010). The Emergence of Intelligent Enterprises: From CPS to CPSS. IEEE Intelligent Systems, 25 (4), 85–88. doi: https://doi.org/10.1109/mis.2010.104
- Dzheniuk, N., Yevseiev, S., Opirskyy, I., Voropay, N., Korolev, R., Sydorenko, Z. (2023). Sociocyberphysical System Wireless Air Network Topology Synthesis Model. Mizhnarodnyi naukovo-praktychnyi forum «Tsyfrova realnist». Kiberbezpeka ta informatsiyni tekhnolohiyi v umovakh hibrydnykh viyn. Kharkiv-Odesa, 4–10.
- Horváth, I., Rusák, Z., Li, Y. (2017). Order Beyond Chaos: Introducing the Notion of Generation to Characterize the Continuously Evolving Implementations of Cyber-Physical Systems. Volume 1: 37th Computers and Information in Engineering Conference. doi: https://doi.org/10.1115/detc2017-67082
- Tanik, U. J., Begley, A. (2013). An Adaptive Cyber-Physical System Framework for Cyber-Physical Systems Design Automation. Applied Cyber-Physical Systems, 125–140. doi: https://doi.org/10.1007/978-1-4614-7336-7_11
- Yin, D., Ming, X., Zhang, X. (2020). Understanding Data-Driven Cyber-Physical-Social System (D-CPSS) Using a 7C Framework in Social Manufacturing Context. Sensors, 20 (18), 5319. doi: https://doi.org/10.3390/s20185319
- Hao, K. (2020). OpenAI is giving Microsoft exclusive access to its GPT-3 language model. MIT Technology Review. Available at: https://www.technologyreview.com/2020/09/23/1008729/openai-is-giving-microsoft-exclusive-access-to-its-gpt-3-language-model/
- Goldstein, J. A., Sastry, G., Musser, M., DiResta, R., Gentzel, M., Sedova. K. (2023). Generative Language Models and Automated Influence Operations: Emerging Threats and Potential Mitigations. Available at: https://cdn.openai.com/papers/forecasting-misuse.pdf
- Tabassi, E. (2023). Artificial Intelligence Risk Management Framework. NIST AI 100-1. NIST. doi: https://doi.org/10.6028/nist.ai.100-1
- Wang, Z., Sun, L., Zhu, H. (2020). Defining Social Engineering in Cybersecurity. IEEE Access, 8, 85094–85115. doi: https://doi.org/10.1109/access.2020.2992807
- NIST Special Publication 1270. Proposes a framework for identifying and managing bias in artificial intelligence.
- Foster, D. (2023). Generative Deep Learning. O'Reilly Media, Inc.
- Yevseiev, S., Milevskyi, S., Bortnik, L., Alexey, V., Bondarenko, K., Pohasii, S. (2022). Socio-Cyber-Physical Systems Security Concept. 2022 International Congress on Human-Computer Interaction, Optimization and Robotic Applications (HORA). doi: https://doi.org/10.1109/hora55278.2022.9799957
- Wang, Z., Zhu, H., Sun, L. (2021). Social Engineering in Cybersecurity: Effect Mechanisms, Human Vulnerabilities and Attack Methods. IEEE Access, 9, 11895–11910. doi: https://doi.org/10.1109/access.2021.3051633
- Prete, E. D., Pera, F., Faramondi, L., Fioravanti, C., Guarino, S., Oliva, G., Setola, R. (2020). Anomaly and Attack Detection in Supervisory Control Networks for Cyber-Physical Systems. Proceedings of the 30th European Safety and Reliability Conference and 15th Probabilistic Safety Assessment and Management Conference. doi: https://doi.org/10.3850/978-981-14-8593-0_4315-cd
- Toublanc, T., Guillet, S., de Lamotte, F., Berruet, P., Lapotre, V. (2017). Using a Virtual Plant to Support the Development of Intelligent Gateway for Sensors/Actuators Security. IFAC-PapersOnLine, 50 (1), 5837–5842. doi: https://doi.org/10.1016/j.ifacol.2017.08.541
- Calefato, F., Lanubile, F., Novielli, N. (2017). A Preliminary Analysis on the Effects of Propensity to Trust in Distributed Software Development. 2017 IEEE 12th International Conference on Global Software Engineering (ICGSE). doi: https://doi.org/10.1109/icgse.2017.1
- Lombardi, M., Vannuccini, S. (2022). Understanding emerging patterns and dynamics through the lenses of the cyber-physical universe. Patterns, 3 (11), 100601. doi: https://doi.org/10.1016/j.patter.2022.100601
- Roy, T., Tariq, A., Dey, S. (2022). A Socio-Technical Approach for Resilient Connected Transportation Systems in Smart Cities. IEEE Transactions on Intelligent Transportation Systems, 23 (6), 5019–5028. doi: https://doi.org/10.1109/tits.2020.3045854
- Hamzaoui, M. A., Julien, N. (2022). Social Cyber-Physical Systems and Digital Twins Networks: A perspective about the future digital twin ecosystems. IFAC-PapersOnLine, 55 (8), 31–36. doi: https://doi.org/10.1016/j.ifacol.2022.08.006
- Li, X., Ye, P., Li, J., Liu, Z., Cao, L., Wang, F.-Y. (2022). From Features Engineering to Scenarios Engineering for Trustworthy AI: I&I, C&C, and V&V. IEEE Intelligent Systems, 37 (4), 18–26. doi: https://doi.org/10.1109/mis.2022.3197950
- Lezoche, M., Panetto, H. (2018). Cyber-Physical Systems, a new formal paradigm to model redundancy and resiliency. Enterprise Information Systems, 14 (8), 1150–1171. doi: https://doi.org/10.1080/17517575.2018.1536807
- Sowe, S. K., Simmon, E., Zettsu, K., de Vaulx, F., Bojanova, I. (2016). Cyber-Physical-Human Systems: Putting People in the Loop. IT Professional, 18 (1), 10–13. doi: https://doi.org/10.1109/mitp.2016.14
- Smirnov, A., Shilov, N., Gusikhin, O. (2017). Cyber-physical-human system for connected car-based e-tourism: Approach and case study scenario. 2017 IEEE Conference on Cognitive and Computational Aspects of Situation Management (CogSIMA). doi: https://doi.org/10.1109/cogsima.2017.7929591
- Kumar, S. A. P., Bhargava, B., Macedo, R., Mani, G. (2017). Securing IoT-Based Cyber-Physical Human Systems against Collaborative Attacks. 2017 IEEE International Congress on Internet of Things (ICIOT). doi: https://doi.org/10.1109/ieee.iciot.2017.11
- Zhu, Y., Tan, Y., Li, R., Luo, X. (2015). Cyber-Physical-Social-Thinking Modeling and Computing for Geological Information Service System. 2015 International Conference on Identification, Information, and Knowledge in the Internet of Things (IIKI). doi: https://doi.org/10.1109/iiki.2015.48
- Kannisto, J., Makitalo, N., Aaltonen, T., Mikkonen, T. (2016). Programming Model Perspective on Security and Privacy of Social Cyber-physical Systems. 2016 IEEE International Conference on Mobile Services (MS). doi: https://doi.org/10.1109/mobserv.2016.23
- Xu, Q., Su, Z., Yu, S. (2018). Green Social CPS Based E-Healthcare Systems to Control the Spread of Infectious Diseases. 2018 IEEE International Conference on Communications (ICC). doi: https://doi.org/10.1109/icc.2018.8422421
- Rose, S., Borchert, O., Mitchell, S., Connelly, S. (2020). Zero Trust Architecture. NIST. doi: https://doi.org/10.6028/nist.sp.800-207
- Yevseiev, S., Tolkachov, M., Shetty, D., Khvostenko, V., Strelnikova, A., Milevskyi, S., Golovashych, S. (2023). The concept of building security of the network with elements of the semiotic approach. ScienceRise, 1, 24–34. doi: https://doi.org/10.21303/2313-8416.2023.002828
- Gilchrist, A. (2016). Industry 4.0. Apress Berkeley, 250. doi: https://doi.org/10.1007/978-1-4842-2047-4
- EFFRA. Factories of the Future: Multi-annual Roadmap for the Contractual PPP under Horizon 2020. European Commission. Available at: https://www.effra.eu/sites/default/files/factories_of_the_future_2020_roadmap.pdf
- Monostori, L. (2014). Cyber-physical Production Systems: Roots, Expectations and R&D Challenges. Procedia CIRP, 17, 9–13. doi: https://doi.org/10.1016/j.procir.2014.03.115
- Uhlemann, T. H.-J., Lehmann, C., Steinhilper, R. (2017). The Digital Twin: Realizing the Cyber-Physical Production System for Industry 4.0. Procedia CIRP, 61, 335–340. doi: https://doi.org/10.1016/j.procir.2016.11.152
- Kang, H. S., Lee, J. Y., Choi, S., Kim, H., Park, J. H., Son, J. Y. et al. (2016). Smart manufacturing: Past research, present findings, and future directions. International Journal of Precision Engineering and Manufacturing-Green Technology, 3 (1), 111–128. doi: https://doi.org/10.1007/s40684-016-0015-5
- Sniderman, B., Mahto, M., Cotteleer, M. J. (2016). Industry 4.0 and Manufacturing Ecosystems – Exploring the World of Connected Enterprises. Deloitte University Press. Available at: https://www2.deloitte.com/content/dam/insights/us/articles/manufacturing-ecosystems-exploring-world-connected-enterprises/DUP_2898_Industry4.0ManufacturingEcosystems.pdf
- Hermann, M., Pentek, T., Otto, B. (2016). Design Principles for Industrie 4.0 Scenarios. 2016 49th Hawaii International Conference on System Sciences (HICSS). doi: https://doi.org/10.1109/hicss.2016.488
- Goldstein, J. A., Sastry, G., Musser, M., DiResta, R., Gentzel, M., Sedova, K. (2023). Forecasting potential misuses of language models for disinformation campaigns—and how to reduce risk. Stanford. Available at: https://cyber.fsi.stanford.edu/io/news/forecasting-potential-misuses-language-models-disinformation-campaigns-and-how-reduce-risk
- Kato, T., Kudo, Y., Miyakoshi, J., Otsuka, J., Saigo, H., Karasawa, K. et al. (2020). Rational Choice Hypothesis as X-point of Utility Function and Norm Function. Applied Economics and Finance, 7 (4), 63. doi: https://doi.org/10.11114/aef.v7i4.4890
- Heath, J. (2008). Following the Rules: Practical Reasoning and Deontic Constraint. Oxford University Press. doi: https://doi.org/10.1093/acprof:oso/9780195370294.001.0001
- Yevseiev, S., Melenti, Y., Voitko, O., Hrebeniuk, V., Korchenko, A., Mykus, S., Milov, O. et al. (2021). Development of a concept for building a critical infrastructure facilities security system. Eastern-European Journal of Enterprise Technologies, 3 (9 (111)), 63–83. doi: https://doi.org/10.15587/1729-4061.2021.233533
- Androshchuk, А., Yevseiev, S., Melenchuk, V., Lemeshko, O., Lemeshko, V. (2020). Improvement of project risk assessment methods of implementation of automated information components of non-commercial organizational and technical systems. EUREKA: Physics and Engineering, 1, 48–55. doi: https://doi.org/10.21303/2461-4262.2020.001131
- Yevseiev, S., Ponomarenko, V., Laptiev, O., Milov, O., Korol, O., Milevskyi, S. et. al.; Yevseiev, S., Ponomarenko, V., Laptiev, O., Milov, O. (Eds.) (2021). Synergy of building cybersecurity systems. Kharkiv: РС ТЕСHNOLOGY СЕNTЕR, 188. doi: https://doi.org/10.15587/978-617-7319-31-2
- Yevseiev, S., Hryshchuk, R., Molodetska, K., Nazarkevych, M., Hrytsyk, V., Milov, O. et. al.; Yevseiev, S., Hryshchuk, R., Molodetska, K., Nazarkevych, M. (Eds.) (2022). Modeling of security systems for critical infrastructure facilities. Kharkiv: РС ТЕСHNOLOGY СЕNTЕR, 196. doi: https://doi.org/10.15587/978-617-7319-57-2
- Yevseiev, S., Khokhlachova, Yu., Ostapov, S., Laptiev, O., Korol, O., Milevskyi, S. et. al.; Yevseiev, S., Khokhlachova, Yu., Ostapov, S., Laptiev, O. (Eds.) (2023). Models of socio-cyber-physical systems security. Kharkiv: РС ТЕСHNOLOGY СЕNTЕR, 184. doi: https://doi.org/10.15587/978-617-7319-72-5
- Shmatko, O., Balakireva, S., Vlasov, A., Zagorodna, N., Korol, O., Milov, O. et al. (2020). Development of methodological foundations for designing a classifier of threats to cyberphysical systems. Eastern-European Journal of Enterprise Technologies, 3 (9 (105)), 6–19. doi: https://doi.org/10.15587/1729-4061.2020.205702
- Angiulli, F., Fassetti, F., Serrao, C. (2023). Anomaly detection with correlation laws. Data & Knowledge Engineering, 145, 102181. doi: https://doi.org/10.1016/j.datak.2023.102181
- Bonabeau, E. (2002). Agent-based modeling: Methods and techniques for simulating human systems. Proceedings of the National Academy of Sciences, 99, 7280–7287. doi: https://doi.org/10.1073/pnas.082080899
- Macal, C. M. (2016). Everything you need to know about agent-based modelling and simulation. Journal of Simulation, 10 (2), 144–156. doi: https://doi.org/10.1057/jos.2016.7
- Walker, J. J. (2012). Cyber security concerns for emergency management. Emergency Management. doi: https://doi.org/10.5772/34104
- Ali, N. S. (2016). A four-phase methodology for protecting web applications using an effective real-time technique. International Journal of Internet Technology and Secured Transactions, 6 (4), 303. doi: https://doi.org/10.1504/ijitst.2016.10003854
- Park, K.-J., Zheng, R., Liu, X. (2012). Cyber-physical systems: Milestones and research challenges. Computer Communications, 36 (1), 1–7. doi: https://doi.org/10.1016/j.comcom.2012.09.006
- Hansman, S., Hunt, R. (2005). A taxonomy of network and computer attacks. Computers & Security, 24 (1), 31–43. doi: https://doi.org/10.1016/j.cose.2004.06.011
- Goel, S., Chen, V. (2005). Information security risk analysis – a matrix-based approach. Proceedings of the Information Resource Management Association (IRMA) International Conference. San Diego. Available at: https://www.albany.edu/~GOEL/publications/goelchen2005.pdf
- Kjaerland, M. (2006). A taxonomy and comparison of computer security incidents from the commercial and government sectors. Computers & Security, 25 (7), 522–538. doi: https://doi.org/10.1016/j.cose.2006.08.004
- Blackwell, C. (2010). A security ontology for incident analysis. Proceedings of the Sixth Annual Workshop on Cyber Security and Information Intelligence Research. doi: https://doi.org/10.1145/1852666.1852717
- Ahmad, R., Yunos, Z. (2012). A dynamic cyber terrorism framework. International Journal of Computer Science and Information Security, 10 (2), 149–158.
- Judіn, O. K. (2015). Derzhavnі іnformacіynі resursi [State information resources]. Metodologіya pobudovi klasifіkatora zagroz. Kyiv: NAU, 214.
- Sznajd-Weron, K., Sznajd, J. (2000). Opinion evolution in closed community. International Journal of Modern Physics C, 11 (06), 1157–1165. doi: https://doi.org/10.1142/s0129183100000936
- Deffuant, G., Neau, D., Amblard, F., Weisbuch, G. (2000). Mixing beliefs among interacting agents. Advances in Complex Systems, 03, 87–98. doi: https://doi.org/10.1142/s0219525900000078
- Hegselmann, R., Krause, U. (2002). Opinion dynamics and bounded confidence: Models, analysis and simulation. Journal of Artificial Societies and Social Simulation, 5 (3). Available at: https://www.jasss.org/5/3/2.html
- Weimer, C. W., Miller, J. O., Hill, R. R. (2016). Agent-based modeling: An introduction and primer. 2016 Winter Simulation Conference (WSC). doi: https://doi.org/10.1109/wsc.2016.7822080
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2023 Serhii Yevseiev, Nataliia Dzheniuk, Maksym Tolkachov, Oleksandr Milov, Tetiana Voitko, Mykhailo Prygara, Oleksandr Shpak, Natalia Voropay, Andrii Volkov, Oleksandr Lezik

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





