Підвищення захищеності програмних реалізацій електронного підпису Falcon від атак на основі шуму обчислень з плаваючою точкою
DOI:
https://doi.org/10.15587/1729-4061.2024.310521Ключові слова:
квантово-стійкі перетворення, Falcon, плаваюча точка, фіксована точка, NIST, NTRUАнотація
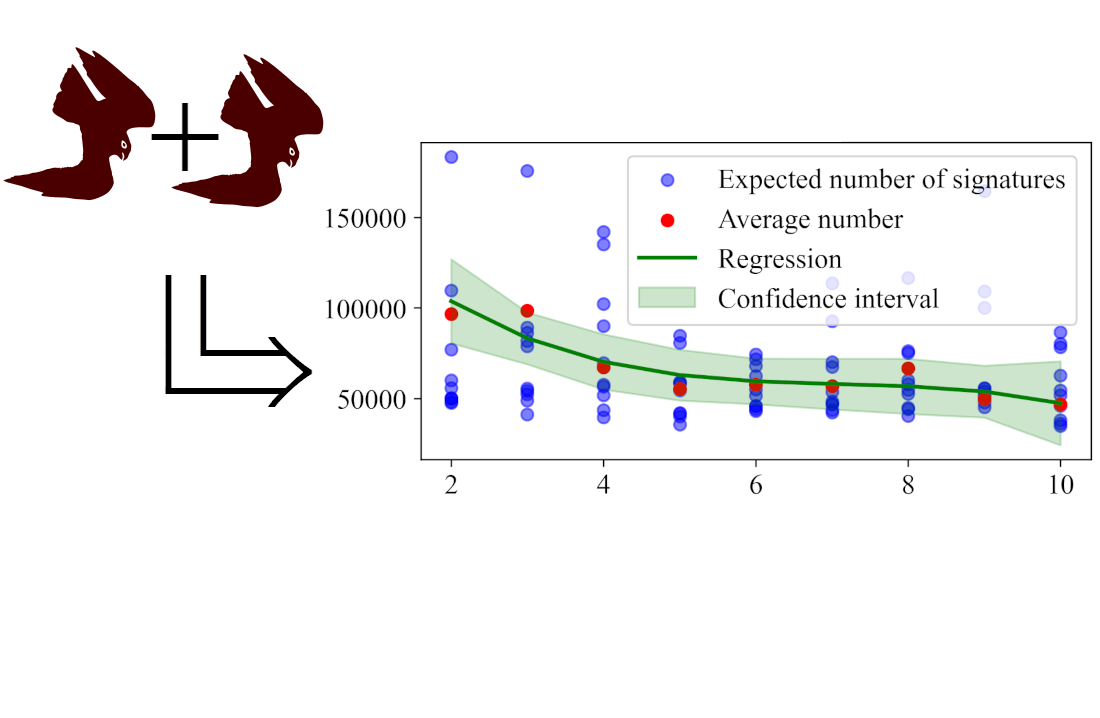
Об’єктом дослідження є електронні підписи. Схема електронного підпису Falcon є одним з фіналістів конкурсу NIST з квантово-стійкої криптографії. Однією з її ключових особливостей є використання обчислень з плаваючою крапкою, котре призводить до можливості атаки відновлення ключів при наявності двох неспівпадаючих підписів, сформованих в особливих умовах. Робота присвячена проблемі удосконалення ЕП (електронного підпису) Falcon з метою унеможливлення таких атак, а також використання обчислень з фіксованою точкою замість обчислень з плаваючою точкою в схемі ЕП Falcon. Головним результатом роботи є пропозиції щодо методів покращення безпеки Falcon від атак, заснованих на особливостях використання обчислень з плаваючою точкою. Запропоновані методи покращення безпеки відрізняються від інших використанням обчислень з фіксованою крапкою з конкретним експериментально визначеним масштабом в одному випадку. В іншому випадку - пропозиціями щодо модифікації операцій в ході виконання яких виникають умови для виконання атаки на рівні реалізації. У результаті проведеного аналізу було уточнено ймовірності вдалого проведення атаки на відновлення таємного ключа для еталонної реалізації ЕП Falcon. Було локалізовано конкретні місця в коді, що роблять атаку можливою та запропоновано модифікацію коду, що робить проведення атаки неможливим. Додатково було визначено необхідний масштаб для обчислень з фіксованою точкою, при якому можливо повністю позбутися обчислень з плаваючою точкою. Отримані результати можуть бути використані для якісного покращення безпеки існуючих ЕП. Це дозволить створити надійніші та більш захищені інформаційні системи, що використовують ЕП. Крім того, отримані результати можуть бути впроваджені в існуючі системи для забезпечення їхньої стійкості до сучасних загроз
Посилання
- Fouque, P., Hoffstein, J., Kirchner, P., Lyubashevsky, V., Pornin, T., Prest, T. et al. (2020). Falcon: Fast-Fourier Lattice-based Compact Signatures over NTRU. Available at: https://falcon-sign.info/falcon.pdf
- Post-Quantum Cryptography PQC. NIST. Available at: https://csrc.nist.gov/projects/post-quantum-cryptography
- Prest, T. (2017). Sharper Bounds in Lattice-Based Cryptography Using the Rényi Divergence. Advances in Cryptology – ASIACRYPT 2017, 347–374. https://doi.org/10.1007/978-3-319-70694-8_13
- Pornin, T. (2019). New Efficient, Constant-Time Implementations of Falcon. ePrint IACR. Available at: https://eprint.iacr.org/2019/893
- Karabulut, E., Aysu, A. (2021). FALCON Down: Breaking FALCON Post-Quantum Signature Scheme through Side-Channel Attacks. 2021 58th ACM/IEEE Design Automation Conference (DAC). https://doi.org/10.1109/dac18074.2021.9586131
- Guerreau, M., Martinelli, A., Ricosset, T., Rossi, M. (2022). The Hidden Parallelepiped Is Back Again: Power Analysis Attacks on Falcon. IACR Transactions on Cryptographic Hardware and Embedded Systems, 141–164. https://doi.org/10.46586/tches.v2022.i3.141-164
- Potii, O., Kachko, O., Kandii, S., Kaptol, Y. (2024). Determining the effect of a floating point on the Falcon digital signature algorithm security. Eastern-European Journal of Enterprise Technologies, 1 (9 (127)), 52–59. https://doi.org/10.15587/1729-4061.2024.295160
- Pornin, T. (2023). Improved Key Pair Generation for Falcon, BAT and Hawk. Cryptology ePrint Archive. Available at: https://eprint.iacr.org/2023/290
- Gentry, C., Peikert, C., Vaikuntanathan, V. (2007). Trapdoors for Hard Lattices and New Cryptographic Constructions. Cryptology ePrint Archive. Available at: https://eprint.iacr.org/2007/432
- Albrecht, M., Ducas, L. (2021). Lattice Attacks on NTRU and LWE: A History of Refinements. Cryptology ePrint Archive. Available at: https://eprint.iacr.org/2021/799
- Prest, T. (2015). Gaussian Sampling in Lattice-Based Cryptography. THALES. Available at: https://tprest.github.io/pdf/pub/thesis-thomas-prest.pdf
- Ducas, L., Prest, T. (2016). Fast Fourier Orthogonalization. Proceedings of the ACM on International Symposium on Symbolic and Algebraic Computation. https://doi.org/10.1145/2930889.2930923
- Fisher, R. A. (1922). On the Interpretation of χ 2 from Contingency Tables, and the Calculation of P. Journal of the Royal Statistical Society, 85 (1), 87. https://doi.org/10.2307/2340521
- Simard, R., L’Ecuyer, P. (2011). Computing the Two-Sided Kolmogorov-Smirnov Distribution. Journal of Statistical Software, 39 (11). https://doi.org/10.18637/jss.v039.i11
- Wilk, M. B., Gnanadesikan, R. (1968). Probability plotting methods for the analysis for the analysis of data. Biometrika, 55 (1), 1–17. https://doi.org/10.1093/biomet/55.1.1
- What Every Computer Scientist Should Know About Floating-Point Arithmetic. Available at: https://docs.oracle.com/cd/E19957-01/806-3568/ncg_goldberg.html
- IEEE Std 754TM-2008. IEEE Standard for Floating-Point Arithmetic. IEEE Computer Society. Available at: https://iremi.univ-reunion.fr/IMG/pdf/ieee-754-2008.pdf
- Pornin, T., Prest, T. (2019). More Efficient Algorithms for the NTRU Key Generation Using the Field Norm. Public-Key Cryptography – PKC 2019, 504–533. https://doi.org/10.1007/978-3-030-17259-6_17
- [FALCON OFFICIAL] Keygen implementation. Available at: https://groups.google.com/a/list.nist.gov/g/pqc-forum/c/bjVkrZmI9VM
##submission.downloads##
Опубліковано
Як цитувати
Номер
Розділ
Ліцензія
Авторське право (c) 2024 Olena Kachko, Yurii Gorbenko, Serhii Kandii, Yevhenii Kaptol

Ця робота ліцензується відповідно до Creative Commons Attribution 4.0 International License.
Закріплення та умови передачі авторських прав (ідентифікація авторства) здійснюється у Ліцензійному договорі. Зокрема, автори залишають за собою право на авторство свого рукопису та передають журналу право першої публікації цієї роботи на умовах ліцензії Creative Commons CC BY. При цьому вони мають право укладати самостійно додаткові угоди, що стосуються неексклюзивного поширення роботи у тому вигляді, в якому вона була опублікована цим журналом, але за умови збереження посилання на першу публікацію статті в цьому журналі.
Ліцензійний договір – це документ, в якому автор гарантує, що володіє усіма авторськими правами на твір (рукопис, статтю, тощо).
Автори, підписуючи Ліцензійний договір з ПП «ТЕХНОЛОГІЧНИЙ ЦЕНТР», мають усі права на подальше використання свого твору за умови посилання на наше видання, в якому твір опублікований. Відповідно до умов Ліцензійного договору, Видавець ПП «ТЕХНОЛОГІЧНИЙ ЦЕНТР» не забирає ваші авторські права та отримує від авторів дозвіл на використання та розповсюдження публікації через світові наукові ресурси (власні електронні ресурси, наукометричні бази даних, репозитарії, бібліотеки тощо).
За відсутності підписаного Ліцензійного договору або за відсутністю вказаних в цьому договорі ідентифікаторів, що дають змогу ідентифікувати особу автора, редакція не має права працювати з рукописом.
Важливо пам’ятати, що існує і інший тип угоди між авторами та видавцями – коли авторські права передаються від авторів до видавця. В такому разі автори втрачають права власності на свій твір та не можуть його використовувати в будь-який спосіб.