Development of an information technology for detecting the sources and networks of disinformation dissemination in cyberspace based on machine learning methods
DOI:
https://doi.org/10.15587/1729-4061.2025.335501Keywords:
disinformation source detection, machine learning, disinformation network, fake news, text similarityAbstract
The object of this study is the processes of identifying sources and networks of disinformation dissemination in the cyberspace of the world. With the growing influence of social networks on public opinion, the issue of identifying and neutralizing propaganda messages is becoming particularly relevant. Conventional methods of combating propaganda such as manual content moderation have proven to be insufficiently effective due to the large amount of information generated daily.
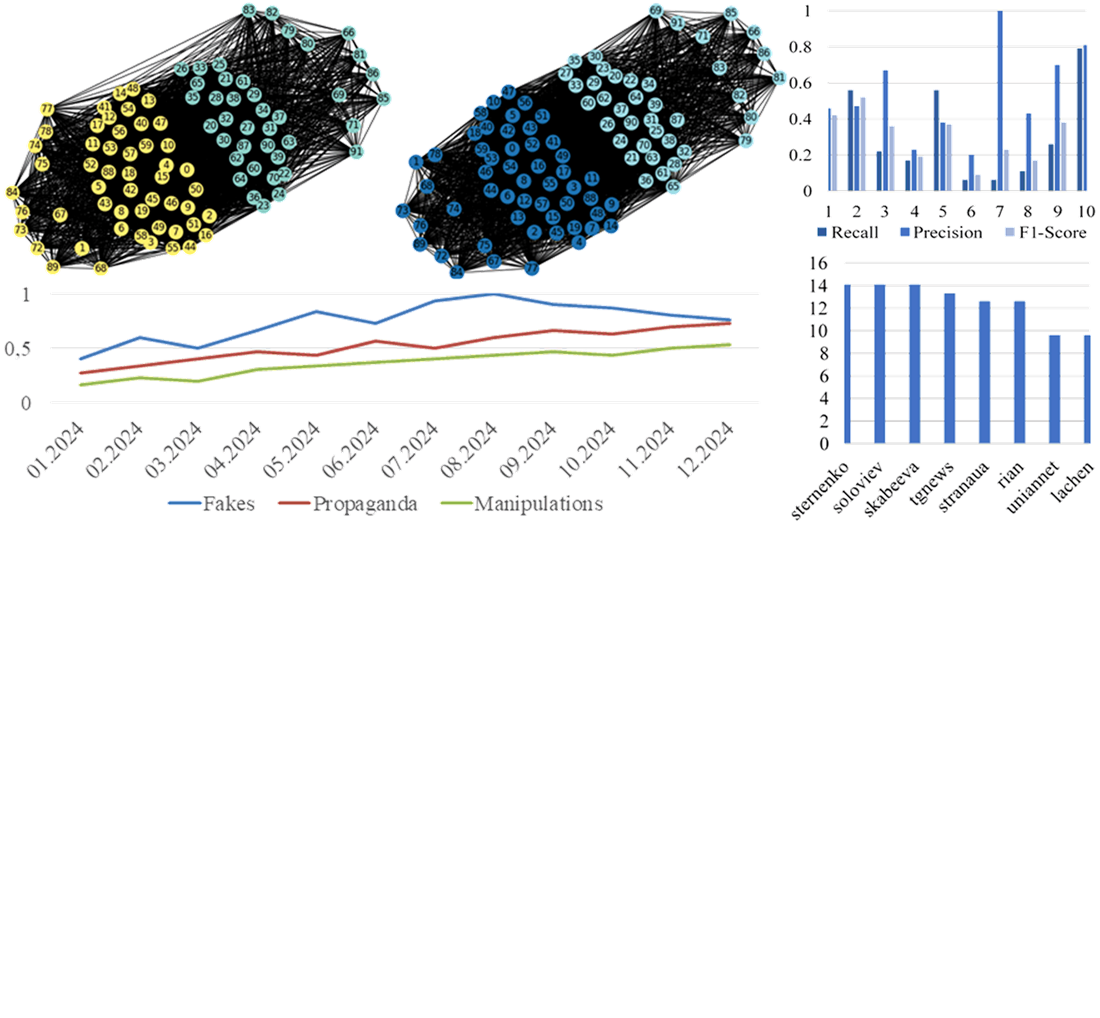
It is important to use natural language processing and machine learning methods to analyze text, identify sources of disinformation dissemination and inauthentic behavior of bots. Based on the analysis of existing methods of intelligent disinformation search, methods have been devised to identify sources and ways of disinformation dissemination in cyberspace by searching for similar text chains and analyzing the similarity of writing style.
Hybrid vector representation makes it possible to capture surface frequency characteristics of the text and semantic features, which has a positive effect on the quality of classification. Cosine similarity, Jacquard, Levenstein and Word2Vec are used to measure similarity. Clustering (DBSCAN, K-Means) helps group fake messages. Graph analysis detects central accounts and bot networks.
Evaluation of the model’s performance by key metrics showed reliable results for identifying sources of disinformation distribution: accuracy – 0.82, F1.3 – 0.8, ROC-AUC – 0.86. The identified differences in lexical patterns for the “fake” and “true” classes confirm the model’s ability to capture the content features of texts. The proposed method for detecting disinformation distribution paths serves as the basis for building scalable systems for monitoring the information space and adapting to other text classification tasks
References
- Kaliyar, R. K., Goswami, A., Narang, P., Sinha, S. (2020). FNDNet – A deep convolutional neural network for fake news detection. Cognitive Systems Research, 61, 32–44. https://doi.org/10.1016/j.cogsys.2019.12.005
- Sahoo, S. R., Gupta, B. B. (2021). Multiple features based approach for automatic fake news detection on social networks using deep learning. Applied Soft Computing, 100, 106983. https://doi.org/10.1016/j.asoc.2020.106983
- Xue, J., Wang, Y., Tian, Y., Li, Y., Shi, L., Wei, L. (2021). Detecting fake news by exploring the consistency of multimodal data. Information Processing & Management, 58 (5), 102610. https://doi.org/10.1016/j.ipm.2021.102610
- Wang, X., Xie, H., Ji, S., Liu, L., Huang, D. (2023). Blockchain-based fake news traceability and verification mechanism. Heliyon, 9 (7), e17084. https://doi.org/10.1016/j.heliyon.2023.e17084
- Martín, A., Huertas-Tato, J., Huertas-García, Á., Villar-Rodríguez, G., Camacho, D. (2022). FacTeR-Check: Semi-automated fact-checking through semantic similarity and natural language inference. Knowledge-Based Systems, 251, 109265. https://doi.org/10.1016/j.knosys.2022.109265
- Liu, X., Qi, L., Wang, L., Metzger, M. J. (2023). Checking the Fact-Checkers: The Role of Source Type, Perceived Credibility, and Individual Differences in Fact-Checking Effectiveness. Communication Research. https://doi.org/10.1177/00936502231206419
- Guo, Z., Schlichtkrull, M., Vlachos, A. (2022). A Survey on Automated Fact-Checking. Transactions of the Association for Computational Linguistics, 10, 178–206. https://doi.org/10.1162/tacl_a_00454
- Shahbazi, Z., Byun, Y.-C. (2021). Fake Media Detection Based on Natural Language Processing and Blockchain Approaches. IEEE Access, 9, 128442–128453. https://doi.org/10.1109/access.2021.3112607
- Elzayady, H., S. Mohamed, M., M. Badran, K., I. Salama, G. (2022). Detecting Arabic textual threats in social media using artificial intelligence: An overview. Indonesian Journal of Electrical Engineering and Computer Science, 25(3), 1712. https://doi.org/10.11591/ijeecs.v25.i3.pp1712-1722
- Saquete, E., Tomás, D., Moreda, P., Martínez-Barco, P., Palomar, M. (2020). Fighting post-truth using natural language processing: A review and open challenges. Expert Systems with Applications, 141, 112943. https://doi.org/10.1016/j.eswa.2019.112943
- Shu, K., Sliva, A., Wang, S., Tang, J., Liu, H. (2017). Fake News Detection on Social Media. ACM SIGKDD Explorations Newsletter, 19 (1), 22–36. https://doi.org/10.1145/3137597.3137600
- Nguyen, V. H., Sugiyama, K., Nakov, P., Kan, M. Y. (2022). FANG: Leveraging social context for fake news detection using graph representation. Communications of the ACM, 65 (4), 124–132. https://doi.org/10.1145/3517214
- Vosoughi, S., Roy, D., Aral, S. (2018). The spread of true and false news online. Science, 359 (6380), 1146–1151. https://doi.org/10.1126/science.aap9559
- Pennycook, G., Bear, A., Collins, E. T., Rand, D. G. (2020). The Implied Truth Effect: Attaching Warnings to a Subset of Fake News Headlines Increases Perceived Accuracy of Headlines Without Warnings. Management Science, 66 (11), 4944–4957. https://doi.org/10.1287/mnsc.2019.3478
- Zhou, X., Zafarani, R. (2020). A survey of fake news: Fundamental theories, detection methods, and opportunities. ACM Computing Surveys (CSUR), 53 (5), 1–40. https://doi.org/10.1145/3395046
- Shu, K., Bernard, H. R., Liu, H.; Agarwal, N., Dokoohaki, N., Tokdemir, S. (Eds.) (2019). Studying Fake News via Network Analysis: Detection and Mitigation. Emerging Research Challenges and Opportunities in Computational Social Network Analysis and Mining. Cham: Springer, 43–65. https://doi.org/10.1007/978-3-319-94105-9_3
- Thorne, J., Vlachos, A. (2018). Automated fact checking: Task formulations, methods and future directions. Proceedings of the 27th International Conference on Computational Linguistics, 3346–3359. Available at: https://aclanthology.org/C18-1283/
- Hanselowski, A., Zhang, H., Li, Z., Sorokin, D., Schiller, B., Schulz, C., Gurevych, I. (2018). UKP-Athene: Multi-Sentence Textual Entailment for Claim Verification. Proceedings of the First Workshop on Fact Extraction and VERification (FEVER), 103–108. https://doi.org/10.18653/v1/w18-5516
- Vysotska, V., Przystupa, K., Kulikov, Y., Chyrun, S., Ushenko, Y., Hu, Z., Uhryn, D. (2025). Recognizing Fakes, Propaganda and Disinformation in Ukrainian Content based on NLP and Machine-learning Technology. International Journal of Computer Network and Information Security, 17 (1), 92–127. https://doi.org/10.5815/ijcnis.2025.01.08
- Vysotska, V., Chyrun, L., Chyrun, S., Holets, I. (2024). Information technology for identifying disinformation sources and inauthentic chat users’ behaviours based on machine learning. CEUR Workshop Proceedings. Available at: https://ceur-ws.org/Vol-3723/paper24.pdf
- Martseniuk, M., Kozachok, V., Bohdanov, O., Iosifov, I., Brzhevska, Z. (2023). Analysis of methods for detecting misinformation in social networks using machine learning. Cybersecurity: Education, Science, Technique, 2 (22), 148–155. https://doi.org/10.28925/2663-4023.2023.22.148155
- Berrondo-Otermin, M., Sarasa-Cabezuelo, A. (2023). Application of Artificial Intelligence Techniques to Detect Fake News: A Review. Electronics, 12 (24), 5041. https://doi.org/10.3390/electronics12245041
- Saeidnia, H. R., Hosseini, E., Lund, B., Tehrani, M. A., Zaker, S., Molaei, S. (2025). Artificial intelligence in the battle against disinformation and misinformation: a systematic review of challenges and approaches. Knowledge and Information Systems, 67 (4), 3139–3158. https://doi.org/10.1007/s10115-024-02337-7
- Vysotska, V., Przystupa, K., Chyrun, L., Vladov, S., Ushenko, Y., Uhryn, D., Hu, Z. (2024). Disinformation, Fakes and Propaganda Identifying Methods in Online Messages Based on NLP and Machine Learning Methods. International Journal of Computer Network and Information Security, 16(5), 57–85. https://doi.org/10.5815/ijcnis.2024.05.06
- Vysotska, V., Nazarkevych, M., Vladov, S., Lozynska, O., Markiv, O., Romanchuk, R., Danylyk, V. (2024). Devising a method for detecting information threats in the Ukrainian cyber space based on machine learning. Eastern-European Journal of Enterprise Technologies, 6 (2 (132)), 36–48. https://doi.org/10.15587/1729-4061.2024.317456
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2025 Victoria Vysotska, Mariia Nazarkevych

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





