Design of a QKD protocol resistant to insider attacks in fully connected decentralized networks
DOI:
https://doi.org/10.15587/1729-4061.2025.337992Keywords:
QKD, superposition, decentralization, blockchain, authentication, cybersecurity, trust-scoring, sybil-resistance, insider, replayAbstract
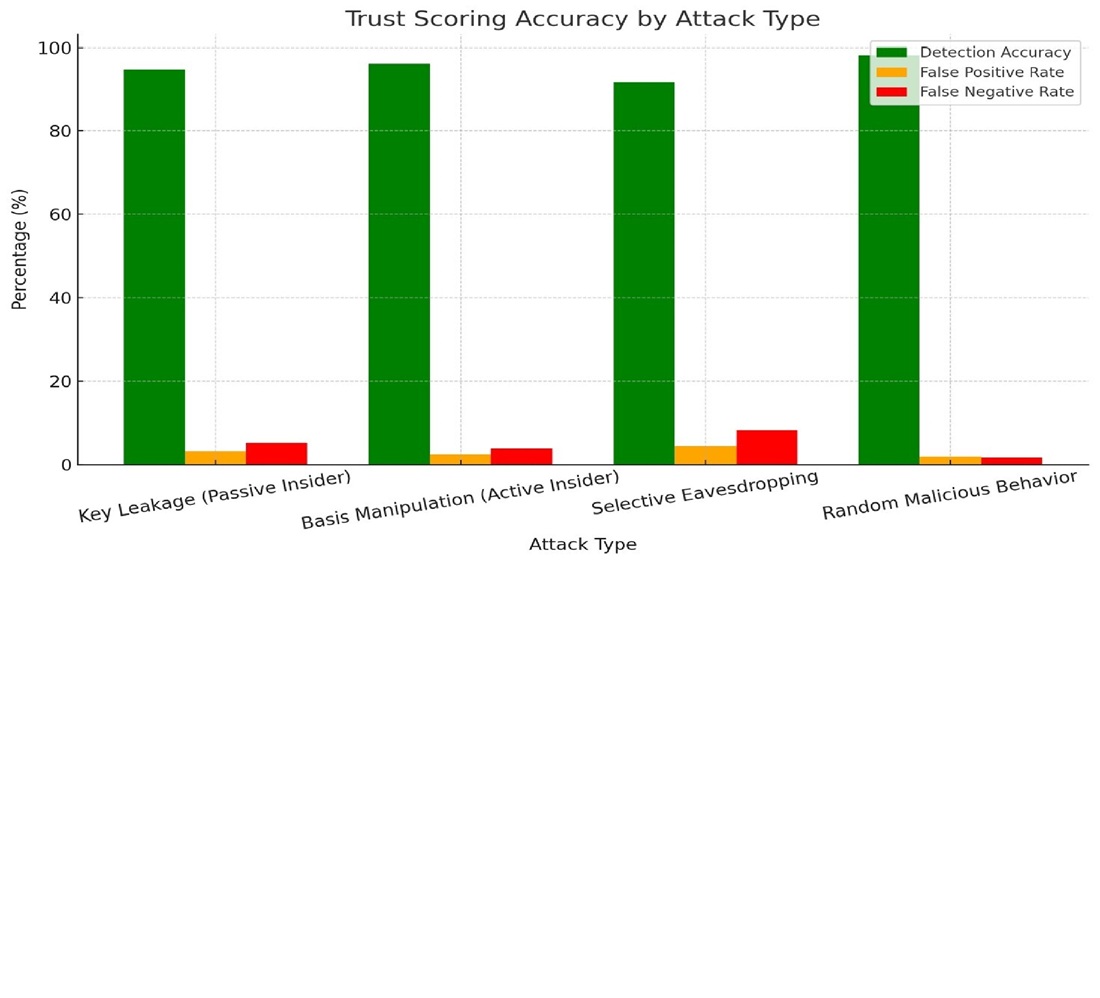
This research focuses on enhancing the security of decentralized quantum key distribution (QKD) networks, where the absence of a central authority creates significant challenges such as malicious node infiltration, undetected key leakage, and unauthorized re-entry of revoked participants. Traditional authentication and trust models are insufficient for fully distributed QKD topologies, which remain highly vulnerable to insider threats and persistent compromise. To address these risks, let’s propose a layered security framework composed of three integrated components: Challenge-Response Authentication (CRA), Dynamic Trust Scoring (DTS), and Blockchain-Based Access Control (BBAC). CRA verifies node legitimacy through randomized quantum-state interactions, significantly reducing impersonation and quantum replay attacks. DTS implements real-time trust evaluation using anomaly detection to dynamically downgrade compromised nodes based on their behavioral deviations. BBAC maintains an immutable and tamper-proof trust ledger to block revoked nodes from re-entering under falsified identities and resists Sybil attacks using post-quantum cryptographic primitives. Simulation results confirm that the system improves detection rates of covert threats, ensures authentication latency under 10 ms, and reduces re-entry success to zero. The proposed architecture ensures long-term scalability and resilience, making it applicable to critical domains such as finance, national infrastructure, and military communication. This work contributes a novel, verifiable, and scalable solution to one of the most pressing open problems in distributed quantum networks
References
- Begimbayeva, Y., Ussatova, O., Zhaxalykov, T., Akhtanov, A., Pashkevich, R., Arshidinova, M. (2024). Development of superposition-based quantum key distribution protocol in decentralized full mesh networks. Eastern-European Journal of Enterprise Technologies, 6 (9 (132)), 39–46. https://doi.org/10.15587/1729-4061.2024.318588
- Begimbayeva, Y., Zhaxalykov, T., Makarov, M. V., Ussatova, O. (2024). Hybrid QKD Approach for Multi-User Quantum Networks: Practical Concept. 2024 20th International Asian School-Seminar on Optimization Problems of Complex Systems (OPCS), 44–48. https://doi.org/10.1109/opcs63516.2024.10720438
- Akhtar, N., Gilbert, A. (2024). Quantum-Enhanced Cryptography: Safeguarding Blockchain and IoT Ecosystems. ResearchGate. https://doi.org/10.13140/RG.2.2.23987.54567
- Nwaga, P., Idima, S. (2025). Post-Quantum Cryptographic Algorithms for Secure Communication in Decentralized Blockchain and Cloud Infrastructure. International Journal of Computer Applications Technology and Research. https://doi.org/10.7753/ijcatr1104.1008
- Mohammed, A. (2024). Cyber Security Implications of Quantum Computing: Shor’s Algorithm and Beyond. Innovative Computer Science Journal, 11 (1), 1-23. https://doi.org/10.5281/ZENODO.14759704
- Harinath, D., Bandi, M., Patil, A., Murthy, R. (2024). Enhanced Data Security and Privacy in IoT Devices Using Blockchain Technology and Quantum Cryptography. Journal of Systems Engineering and Electronics, 34 (6), 61–67. Available at: https://www.researchgate.net/publication/387495645_Enhanced_Data_Security_and_Privacy_in_IoT_devices_using_Blockchain_Technology_and_Quantum_Cryptography
- Ma, X., Wang, C., Li, Z., Zhu, H. (2021). Multi-Party Quantum Key Distribution Protocol with New Bell States Encoding Mode. International Journal of Theoretical Physics, 60 (4), 1328–1338. https://doi.org/10.1007/s10773-021-04758-4
- Ahmed, S., Roseth, T. (2025). Quantum Computing and Blockchain Synergy: A New Paradigm for Information Security. ResearchGate. https://doi.org/10.13140/RG.2.2.23987.54567
- Wu, F., Zhou, B., Song, J., Xie, L. (2025). Quantum-resistant blockchain and performance analysis. The Journal of Supercomputing, 81 (3). https://doi.org/10.1007/s11227-025-07018-y
- Radanliev, P. (2024). Artificial intelligence and quantum cryptography. Journal of Analytical Science and Technology, 15 (1). https://doi.org/10.1186/s40543-024-00416-6
- Ustimenko, V., Pustovit, O. (2025). On the Postquantum Protocol-Based Short Digital Signatures with Multivariate Maps Over Arithmetical Rings. Advances in Information and Communication. Cham: Springer, 688–699. https://doi.org/10.1007/978-3-031-84460-7_44
- Mangla, C., Rani, S., Atiglah, H. K. (2022). Secure Data Transmission Using Quantum Cryptography in Fog Computing. Wireless Communications and Mobile Computing, 2022, 1–8. https://doi.org/10.1155/2022/3426811
- Alshowkan, M., Evans, P. G., Starke, M., Earl, D., Peters, N. A. (2022). Authentication of smart grid communications using quantum key distribution. Scientific Reports, 12 (1). https://doi.org/10.1038/s41598-022-16090-w
- Popa, A.-B. (2024). Advancements in Quantum Communications: Security, Utility, Performance, and Adoption. [PhD Thesis Summary, National University of Science and Technology POLITEHNICA Bucharest]. Available at: https://docs.upb.ro/wp-content/uploads/2024/12/popa_alin_rezumat.pdf
- Yuan, Q., Yuan, H., Zhou, M., Wen, J., Li, J., Hao, B. (2025). A improved group quantum key distribution protocol with multi-party collaboration. Scientific Reports, 15 (1). https://doi.org/10.1038/s41598-024-84244-z
- Xiong, J., Shen, L., Liu, Y., Fang, X. (2025). Enhancing IoT security in smart grids with quantum-resistant hybrid encryption. Scientific Reports, 15 (1). https://doi.org/10.1038/s41598-024-84427-8
- da Silva, R. F. (2024). A blockchain architecture with quantum key distribution (QKD). International Journal of Blockchains and Cryptocurrencies, 5 (3), 161–170. https://doi.org/10.1504/ijbc.2024.143407
- Jarry, H., Olaoye, G., Frank, E., Brightwood, S., Olusegun, J. (2024). Practical Implementation of Quantum Cryptography in Network Security. ResearchGate. Available at: https://www.researchgate.net/publication/384884900
- Asha, H. P., Jingle, I. D. J. (2025). Secure Communication in Fog Nodes through Quantum Key Distribution. Advanced Network Technologies and Intelligent Computing. Springer, 32–46. https://doi.org/10.1007/978-3-031-83783-8_2
- Smailov, N., Akmardin, S., Ayapbergenova, A., Ayapbergenova, G., Kadyrova, R., Sabibolda, A. (2025). Analiza wydajności VLC w optycznych systemach komunikacji bezprzewodowej do zastosowań wewnętrznych. Informatyka, Automatyka, Pomiary w Gospodarce i Ochronie Środowiska, 15 (2), 135–138. https://doi.org/10.35784/iapgos.6971
- Smailov, N., Orynbet, M., Nazarova, A., Torekhan, Z., Koshkinbayev, S., Yssyraiyl, K. et al. (2025). Optymalizacja pracy światłowodowych czujników w warunkach kosmicznych. Informatyka, Automatyka, Pomiary w Gospodarce i Ochronie Środowiska, 15 (2), 130–134. https://doi.org/10.35784/iapgos.7200
- Kapalova, N., Algazy, K., Haumen, A., Sakan, K. (2023). Statistical analysis of the key scheduling of the new lightweight block cipher. International Journal of Electrical and Computer Engineering, 13 (6), 6817–6826. https://doi.org/10.11591/ijece.v13i6.pp6817-6826
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2025 Yenlik Begimbayeva, Temirlan Zhaxalykov, Amir Akhtanov, Ruslan Pashkevich, Olga Ussatova, Mukaddas Arshidinova

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





