Development of a security system organization model taking into account the impact of the external environment
DOI:
https://doi.org/10.15587/1729-4061.2025.345894Keywords:
cyber-physical systems, unmanned aerial vehicles, mobile wireless network, protective elementsAbstract
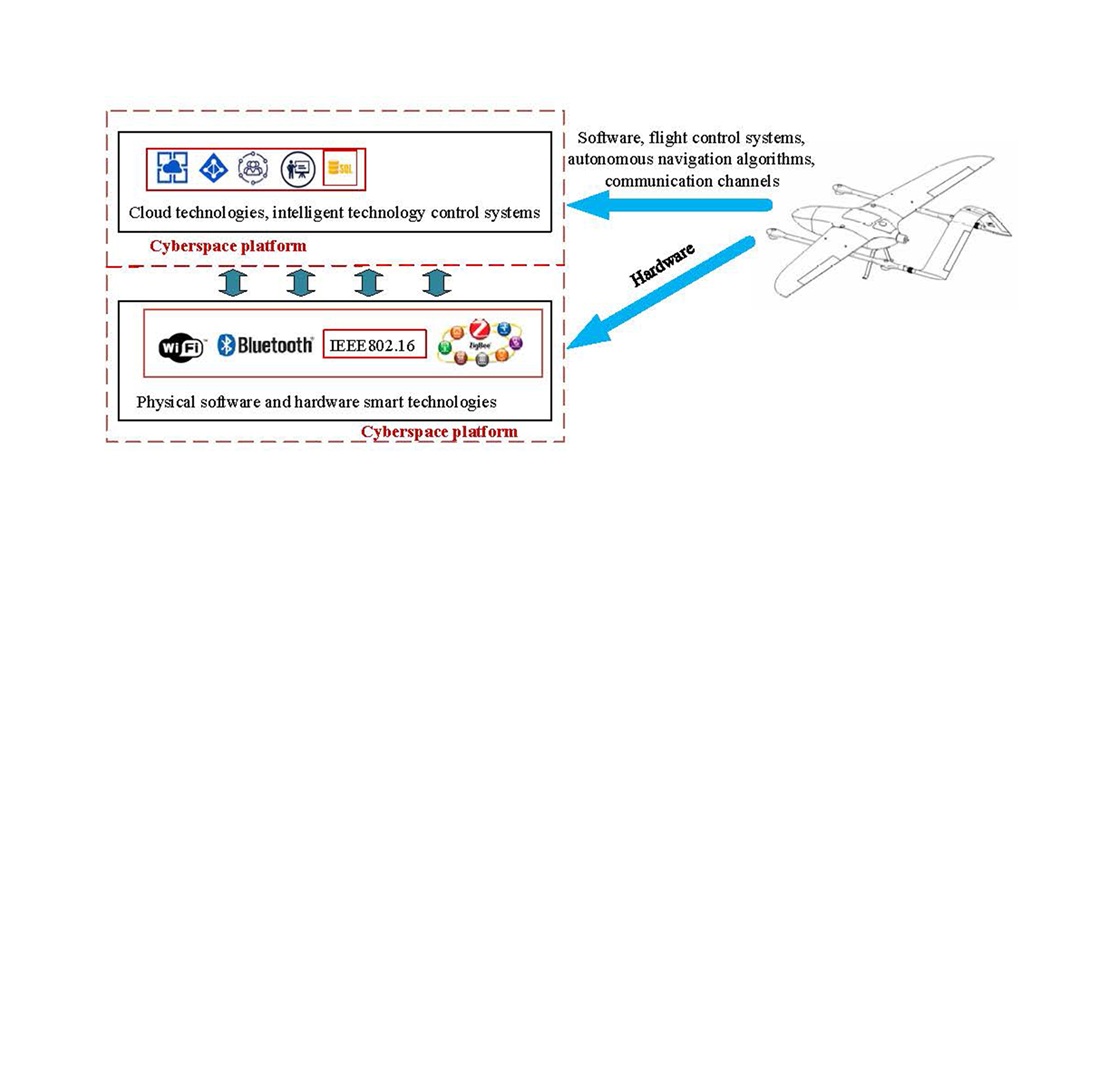
The object of this study is the process of ensuring the security of cyber-physical systems under the influence of external destructive factors, in particular information, radio-electronic, and physical attacks aimed at disrupting continuous system operation. The paper addresses the problem of determining the optimal structure of an airborne mobile network within a cyber-physical system, specifically the ratio between operational and protective elements that ensures maximum system stability under targeted attacks. The presented modeling results are based on a minimax formulation of the interaction between the system and the external environment, which makes it possible to determine critical threshold values of stability parameters.
The applied mathematical model describes both the optimal strategy of the attacking environment and the optimal initial structure of the system itself. This enables the identification of relationships between the initial ratio of operational and protective components and the minimum adversary resources required for complete system destruction. It is shown that an optimal configuration of protective elements forces the attacking environment to expend 1.5–2 times more resources compared to suboptimal structures. A correctly selected ratio of system elements slows down the degradation of the protective contour. The developed mathematical model confirms the existence of an optimal strategy for external environment behavior and an optimal initial structure of the airborne mobile network of the cyber-physical system. This approach improves the design process of cyber-physical systems at early stages, enhances their survivability, and contributes to the development of a methodology for integrated protection of airborne mobile networks under challenging real-world conditions
References
- Graf, S., Quinton, S., Girault, A., Gössler, G. (2018). Building Correct Cyber-Physical Systems: Why We Need a Multiview Contract Theory. Formal Methods for Industrial Critical Systems, 19–31. https://doi.org/10.1007/978-3-030-00244-2_2
- Bereket Abera, Y., Naudet, Y., Panetto, H. (2020). A new Paradigm and Meta-Model for Cyber-Physical-Social Systems. IFAC-PapersOnLine, 53 (2), 10949–10954. https://doi.org/10.1016/j.ifacol.2020.12.2841
- Kampourakis, V., Gkioulos, V., Katsikas, S. (2023). A systematic literature review on wireless security testbeds in the cyber-physical realm. Computers & Security, 133, 103383. https://doi.org/10.1016/j.cose.2023.103383
- Tyagi, A. K., Sreenath, N. (2021). Cyber Physical Systems: Analyses, challenges and possible solutions. Internet of Things and Cyber-Physical Systems, 1, 22–33. https://doi.org/10.1016/j.iotcps.2021.12.002
- Yaacoub, J.-P., Noura, H., Salman, O., Chehab, A. (2020). Security analysis of drones systems: Attacks, limitations, and recommendations. Internet of Things, 11, 100218. https://doi.org/10.1016/j.iot.2020.100218
- Lee, E. (2015). The Past, Present and Future of Cyber-Physical Systems: A Focus on Models. Sensors, 15 (3), 4837–4869. https://doi.org/10.3390/s150304837
- Duo, W., Zhou, M., Abusorrah, A. (2022). A Survey of Cyber Attacks on Cyber Physical Systems: Recent Advances and Challenges. IEEE/CAA Journal of Automatica Sinica, 9 (5), 784–800. https://doi.org/10.1109/jas.2022.105548
- Zuo, Z., Liu, C., Han, Q.-L., Song, J. (2022). Unmanned Aerial Vehicles: Control Methods and Future Challenges. IEEE/CAA Journal of Automatica Sinica, 9 (4), 601–614. https://doi.org/10.1109/jas.2022.105410
- Yevseiev, S., Melenti, Y., Voitko, O., Hrebeniuk, V., Korchenko, A., Mykus, S. et al. (2021). Development of a concept for building a critical infrastructure facilities security system. Eastern-European Journal of Enterprise Technologies, 3 (9 (111)), 63–83. https://doi.org/10.15587/1729-4061.2021.233533
- Lombardi, M., Vannuccini, S. (2022). Understanding emerging patterns and dynamics through the lenses of the cyber-physical universe. Patterns, 3 (11), 100601. https://doi.org/10.1016/j.patter.2022.100601
- Tariq, U., Ahmed, I., Bashir, A. K., Shaukat, K. (2023). A Critical Cybersecurity Analysis and Future Research Directions for the Internet of Things: A Comprehensive Review. Sensors, 23 (8), 4117. https://doi.org/10.3390/s23084117
- Zhao, H. (2022). Multi-vue Design Pour Cyber-physical Systems. Université Côte d'Azur, 170.
- Greer, C., Burns, M., Wollman, D., Griffor, E. (2019). Cyber-physical systems and internet of things. National Institute of Standards and Technology. https://doi.org/10.6028/nist.sp.1900-202
- Ayass, T., Coqueiro, T., Carvalho, T., Jailton, J., Araújo, J., Francês, R. (2022). Unmanned aerial vehicle with handover management fuzzy system for 5G networks: challenges and perspectives. Intelligence & Robotics. https://doi.org/10.20517/ir.2021.07
- Serkov, A., Jammine, A., Kudii, D., Nataliia, D., Farid, N.-A., Bogdan, L. (2023). Security Models and Methods of Socio-Cyberphysical Systems. 2023 7th International Symposium on Multidisciplinary Studies and Innovative Technologies (ISMSIT), 1–6. https://doi.org/10.1109/ismsit58785.2023.10304955
- Khan, M. A., Kumar, N., Alsamhi, S. H., Barb, G., Zywiołek, J., Ullah, I. et al. (2025). Security and Privacy Issues and Solutions for UAVs in B5G Networks: A Review. IEEE Transactions on Network and Service Management, 22 (1), 892–912. https://doi.org/10.1109/tnsm.2024.3487265
- Tsao, K.-Y., Girdler, T., Vassilakis, V. G. (2022). A survey of cyber security threats and solutions for UAV communications and flying ad-hoc networks. Ad Hoc Networks, 133, 102894. https://doi.org/10.1016/j.adhoc.2022.102894
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2025 Nataliia Dzheniuk, Viktor Zaika, Serhii Yevseiev, Yevhen Tarasenko, Vitalii Kryvosheiev, Serhii Kravchenko, Serhii Holdobin, Artur Ismahilov, Ihor Syvachenko

This work is licensed under a Creative Commons Attribution 4.0 International License.
The consolidation and conditions for the transfer of copyright (identification of authorship) is carried out in the License Agreement. In particular, the authors reserve the right to the authorship of their manuscript and transfer the first publication of this work to the journal under the terms of the Creative Commons CC BY license. At the same time, they have the right to conclude on their own additional agreements concerning the non-exclusive distribution of the work in the form in which it was published by this journal, but provided that the link to the first publication of the article in this journal is preserved.
A license agreement is a document in which the author warrants that he/she owns all copyright for the work (manuscript, article, etc.).
The authors, signing the License Agreement with TECHNOLOGY CENTER PC, have all rights to the further use of their work, provided that they link to our edition in which the work was published.
According to the terms of the License Agreement, the Publisher TECHNOLOGY CENTER PC does not take away your copyrights and receives permission from the authors to use and dissemination of the publication through the world's scientific resources (own electronic resources, scientometric databases, repositories, libraries, etc.).
In the absence of a signed License Agreement or in the absence of this agreement of identifiers allowing to identify the identity of the author, the editors have no right to work with the manuscript.
It is important to remember that there is another type of agreement between authors and publishers – when copyright is transferred from the authors to the publisher. In this case, the authors lose ownership of their work and may not use it in any way.





