Покращене виявлення нелегальних транзакцій з bitcoin за допомогою відбору ознак на основі генетичного алгоритму
DOI:
https://doi.org/10.15587/1729-4061.2025.335630Ключові слова:
bitcoin, нелегальні транзакції, машинне навчання, генетичні алгоритми, криптовалютна форензікаАнотація
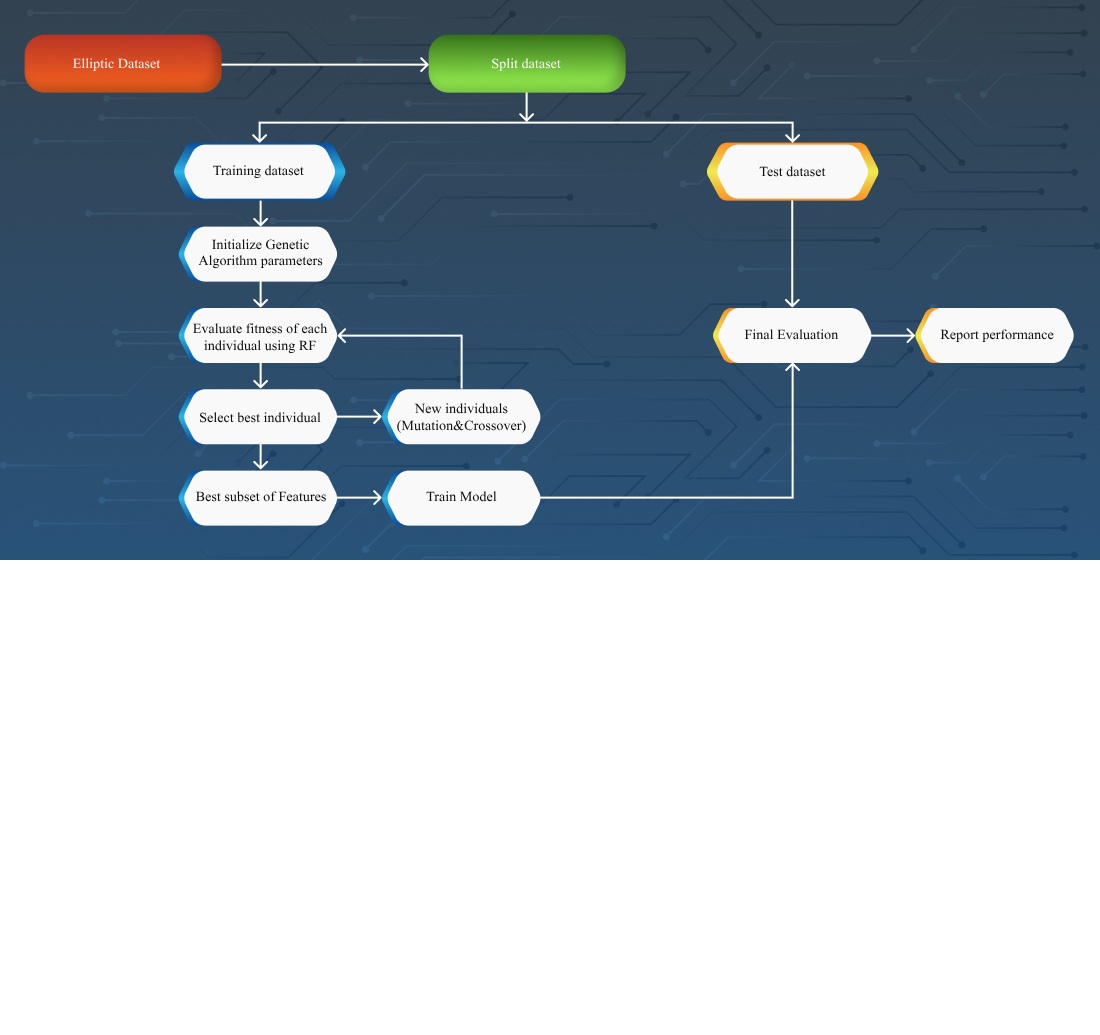
Об'єктом цього дослідження є процес класифікації незаконних транзакцій Bitcoin у наборах даних блокчейну. Проблема, яку розглянуто у цій роботі, полягає у складності виявлення підозрілої активності у криптовалютних мережах через високу розмірність даних транзакцій і відсутність семантичних міток, що обмежує ефективність традиційних методів ручного створення ознак. Запропонований метод поєднує галузеві індикатори нелегальної поведінки з механізмом вибору ознак на основі ГА, який динамічно формує інформативні підмножини ознак. Розроблена система була реалізована та оцінена на наборах даних Elliptic і Elliptic++ із використанням моделі випадкового лісу. Отримані результати демонструють, що метод на основі ГА суттєво підвищує продуктивність моделі: найкраща конфігурація досягла F1-міри 84,3%, точності 99,4% і повноти 73,1%. У порівнянні з базовими підходами на тих самих наборах даних, этот метод забезпечує відносне покращення на 0,9% за F1-мірою, на 0,3% за точністю та на 1,2% за повнотою. Ефективність запропонованого рішення пояснюється його здатністю виявляти приховані закономірності у даних транзакцій без залежності від ручних евристик, а також завдяки оптимізованим параметрам ГА. Відмінною рисою цього методу є поєднання евристичного пошуку з категоріями ознак, визначених на основі предметної області, що підвищує точність класифікації та знижує складність моделі. Отримані результати можуть бути застосовані на практиці, наприклад, для форензичного аналізу криптовалютних транзакцій. Однак успішна імплементація вимагає доступу до історичних записів транзакцій і достатніх обчислювальних ресурсів для обробки великих, насичених ознаками наборів даних
Посилання
- Berentsen, A., Schar, F. (2018). The Case for Central Bank Electronic Money and the Non-case for Central Bank Cryptocurrencies. Review, 100 (2), 97–106. https://doi.org/10.20955/r.2018.97-106
- Gajdek, S., Kozak, S. (2019). Bitcoin as an Electronic Payment Tool. Zeszyty Naukowe Uniwersytetu Przyrodniczo-Humanistycznego w Siedlcach. Seria: Administracja i Zarządzanie, 47 (120), 33–39. https://doi.org/10.34739/zn.2019.47.04
- Bunjaku, F., Gjorgieva-Trajkovska, O., Kacarski, E. M. (2017). Cryptocurrencies – advantages and disadvantages. Journal of Economics, 2 (1), 31–39.
- Sicignano, G. J. (2021). Money Laundering using Cryptocurrency: The Case of Bitcoin! Athens Journal of Law, 7 (2), 253–264. https://doi.org/10.30958/ajl.7-2-7
- How terrorist groups are exploiting crypto to raise funds and evade detection. Elliptic. Available at: https://www.elliptic.co/blog/how-terrorist-organizations-are-exploiting-crypto-to-raise-funds-and-evade-detection Last accessed: 18.03.2024
- Crypto crime mid-year update: Crime down 65% overall, but ransomware headed for huge year thanks to return of big game hunting (2023). Chainalysis Team. Available at: https://www.chainalysis.com/blog/crypto-crime-midyear-2023-update-ransomware-scams/ Last accessed: 18.03.2024
- Crypto Crime Trends: Illicit Volumes Portend Record Year as On-Chain Crime Becomes Increasingly Diverse and Professionalized (2025). Chainalysis Team. Available at: https://www.chainalysis.com/blog/2025-crypto-crime-report-introduction/ Last accessed: 15.02.2025
- Chuen, D. L. K. (2015). Handbook of Digital Currency: Bitcoin, Innovation, Financial Instruments, and Big Data. London: Academic Press. Available at: https://www.researchgate.net/publication/286223926_Handbook_of_Digital_Currency_Bitcoin_Innovation_Financial_Instruments_and_Big_Data Last accessed: 01.03.2024
- Weber, M., Domeniconi, G., Chen, J., Weidele, D. K. I., Bellei, C., Robinson, T., Leiserson, C. E. (2019). Anti-Money Laundering in Bitcoin: Experimenting with Graph Convolutional Networks for Financial Forensics. Proceedings of the Workshop on Anomaly Detection in Finance (KDD ’19). Anchorage. https://doi.org/10.48550/arXiv.1908.02591
- Alarab, I., Prakoonwit, S., Nacer, M. I. (2020). Comparative Analysis Using Supervised Learning Methods for Anti-Money Laundering in Bitcoin. Proceedings of the International Conference on Machine Learning Technologies, 11–17. https://doi.org/10.1145/3409073.3409078
- Alarab, I., Prakoonwit, S., Nacer, M. I. (2020). Competence of Graph Convolutional Networks for Anti-Money Laundering in Bitcoin Blockchain. Proceedings of the 2020 5th International Conference on Machine Learning Technologies, 23–27. https://doi.org/10.1145/3409073.3409080
- Elmougy, Y., Liu, L. (2023). Demystifying Fraudulent Transactions and Illicit Nodes in the Bitcoin Network for Financial Forensics. Proceedings of the 29th ACM SIGKDD Conference on Knowledge Discovery and Data Mining. Long Beach, 3979–3990. https://doi.org/10.1145/3580305.3599803
- Pham, T. B., Lee, S. (2016). Anomaly detection in bitcoin network using unsupervised learning methods. arXiv, arXiv:1611.03941. https://doi.org/10.48550/arXiv.1908.02591
- Lorenz, J., Silva, M. I., Aparício, D., Ascensão, J. T., Bizarro, P. (2020). Machine learning methods to detect money laundering in the bitcoin blockchain in the presence of label scarcity. Proceedings of the First ACM International Conference on AI in Finance. New York, 1–8. https://doi.org/10.1145/3383455.3422549
- Nerurkar, P., Bhirud, S., Patel, D., Ludinard, R., Busnel, Y., & Kumari, S. (2020). Supervised learning model for identifying illegal activities in Bitcoin. Applied Intelligence, 51 (6), 3824–3843. https://doi.org/10.1007/s10489-020-02048-w
- Tayebi, M., El Kafhali, S. (2022). Performance analysis of metaheuristics based hyperparameters optimization for fraud transactions detection. Evolutionary Intelligence, 17 (2), 921–939. https://doi.org/10.1007/s12065-022-00764-5
- Bouchlaghem, Y., Akhiat, Y., Amjad, S. (2022). Feature Selection: A Review and Comparative Study. E3S Web of Conferences, 351, 01046. https://doi.org/10.1051/e3sconf/202235101046
- Breiman, L. (2001). Random Forests. Machine Learning, 45 (1), 5–32. https://doi.org/10.1023/a:1010933404324
- Katoch, S., Chauhan, S. S., Kumar, V. (2020). A review on genetic algorithm: past, present, and future. Multimedia Tools and Applications, 80 (5), 8091–8126. https://doi.org/10.1007/s11042-020-10139-6
- Contreras, R. C., Xavier da Silva, V. T., Xavier da Silva, I. T., Viana, M. S., Santos, F. L. dos, Zanin, R. B. et al. (2024). Genetic Algorithm for Feature Selection Applied to Financial Time Series Monotonicity Prediction: Experimental Cases in Cryptocurrencies and Brazilian Assets. Entropy, 26 (3), 177. https://doi.org/10.3390/e26030177
- Taha, A. A., Malebary, S. J. (2020). An Intelligent Approach to Credit Card Fraud Detection Using an Optimized Light Gradient Boosting Machine. IEEE Access, 8, 25579–25587. https://doi.org/10.1109/access.2020.2971354
- Howcroft, E. (2023). Crypto ransom attacks rise in first half of 2023, chainalysis says. Available at: https://www.reuters.com/technology/crypto-ransom-attacks-rise-first-half-2023-chainalysis-2023-07-12/ Last accessed: 15.02.2025
- Aziz, R. M., Baluch, M. F., Patel, S., Ganie, A. H. (2022). LGBM: a machine learning approach for Ethereum fraud detection. International Journal of Information Technology, 14 (7), 3321–3331. https://doi.org/10.1007/s41870-022-00864-6
- Kute, D. V., Pradhan, B., Shukla, N., Alamri, A. (2021). Deep Learning and Explainable Artificial Intelligence Techniques Applied for Detecting Money Laundering–A Critical Review. IEEE Access, 9, 82300–82317. https://doi.org/10.1109/access.2021.3086230
- Černevičienė, J., Kabašinskas, A. (2024). Explainable artificial intelligence (XAI) in finance: a systematic literature review. Artificial Intelligence Review, 57 (8). https://doi.org/10.1007/s10462-024-10854-8
##submission.downloads##
Опубліковано
Як цитувати
Номер
Розділ
Ліцензія
Авторське право (c) 2025 Medet Shaizat, Shynar Mussiraliyeva

Ця робота ліцензується відповідно до Creative Commons Attribution 4.0 International License.
Закріплення та умови передачі авторських прав (ідентифікація авторства) здійснюється у Ліцензійному договорі. Зокрема, автори залишають за собою право на авторство свого рукопису та передають журналу право першої публікації цієї роботи на умовах ліцензії Creative Commons CC BY. При цьому вони мають право укладати самостійно додаткові угоди, що стосуються неексклюзивного поширення роботи у тому вигляді, в якому вона була опублікована цим журналом, але за умови збереження посилання на першу публікацію статті в цьому журналі.
Ліцензійний договір – це документ, в якому автор гарантує, що володіє усіма авторськими правами на твір (рукопис, статтю, тощо).
Автори, підписуючи Ліцензійний договір з ПП «ТЕХНОЛОГІЧНИЙ ЦЕНТР», мають усі права на подальше використання свого твору за умови посилання на наше видання, в якому твір опублікований. Відповідно до умов Ліцензійного договору, Видавець ПП «ТЕХНОЛОГІЧНИЙ ЦЕНТР» не забирає ваші авторські права та отримує від авторів дозвіл на використання та розповсюдження публікації через світові наукові ресурси (власні електронні ресурси, наукометричні бази даних, репозитарії, бібліотеки тощо).
За відсутності підписаного Ліцензійного договору або за відсутністю вказаних в цьому договорі ідентифікаторів, що дають змогу ідентифікувати особу автора, редакція не має права працювати з рукописом.
Важливо пам’ятати, що існує і інший тип угоди між авторами та видавцями – коли авторські права передаються від авторів до видавця. В такому разі автори втрачають права власності на свій твір та не можуть його використовувати в будь-який спосіб.